A switching method, device and network architecture
A network architecture and network technology, applied in the field of communication, can solve problems such as inapplicability of new network architectures
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
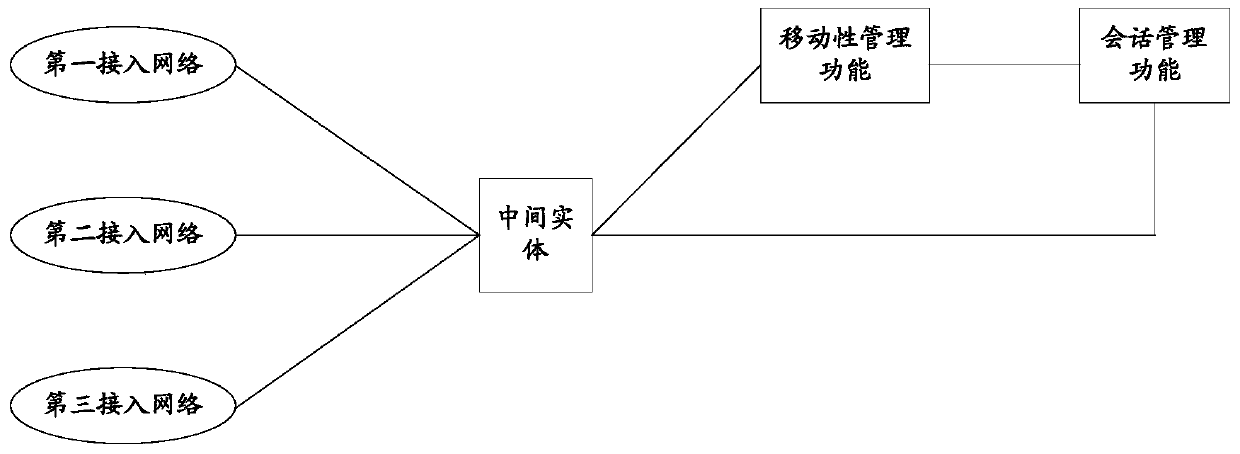
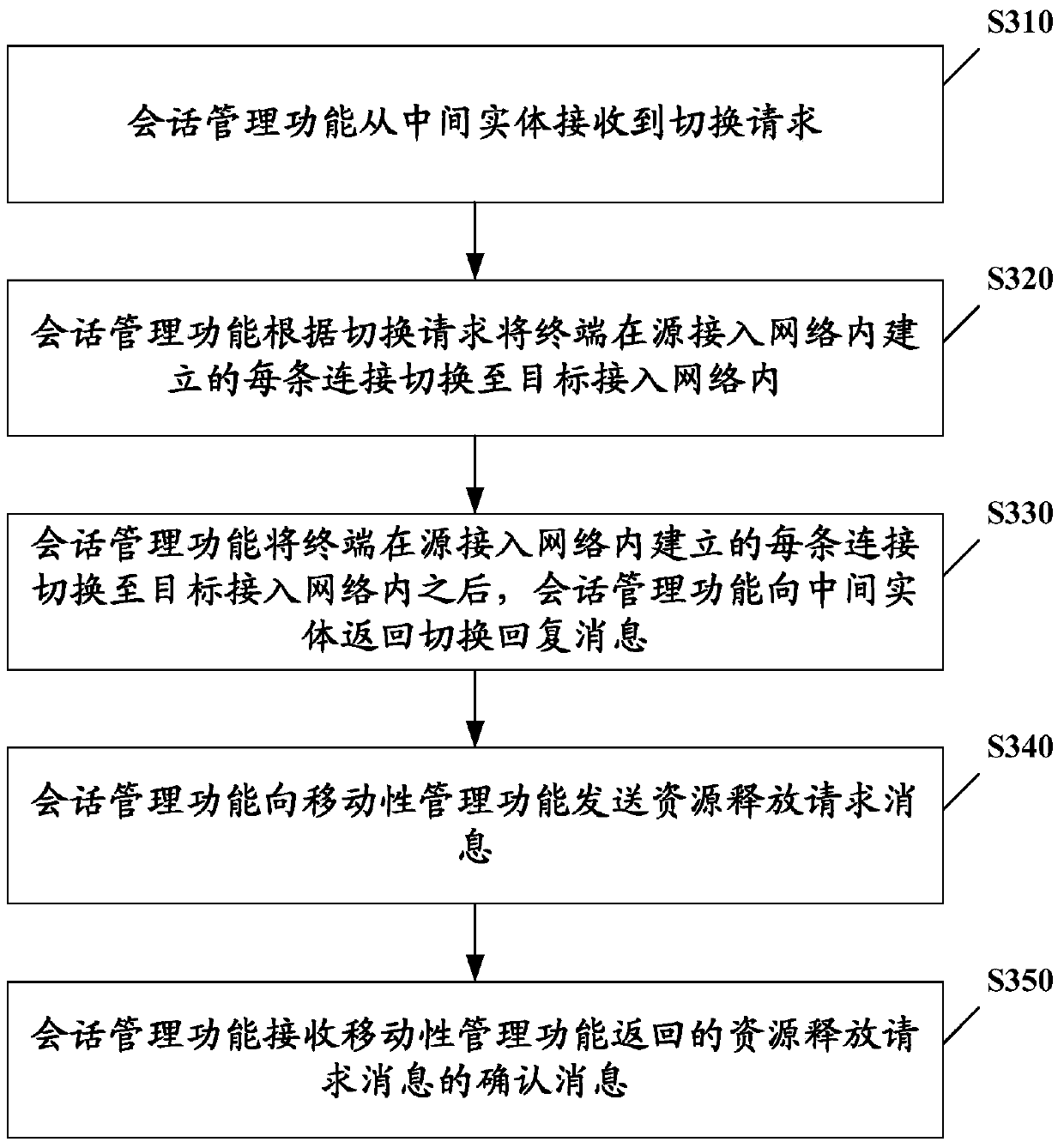
[0070] Combine below figure 2 The network architecture in the application scenario, refer to image 3 A handover method according to an exemplary embodiment of the present invention will be described. It should be noted that the above application scenarios are only shown for the purpose of understanding the spirit and principle of the present invention, and the implementation manners of the present invention are not limited in this regard. On the contrary, the embodiments of the present invention can be applied to any applicable scene.
[0071] image 3 Schematically shows a flow chart of an embodiment of a handover method according to an embodiment of the present invention, the network architecture to which the handover method is applicable includes: an access network, an intermediate entity, and a mobility management function (also referred to as a mobile property management function entity) and session management function (also called session management function entity)...
no. 2 example
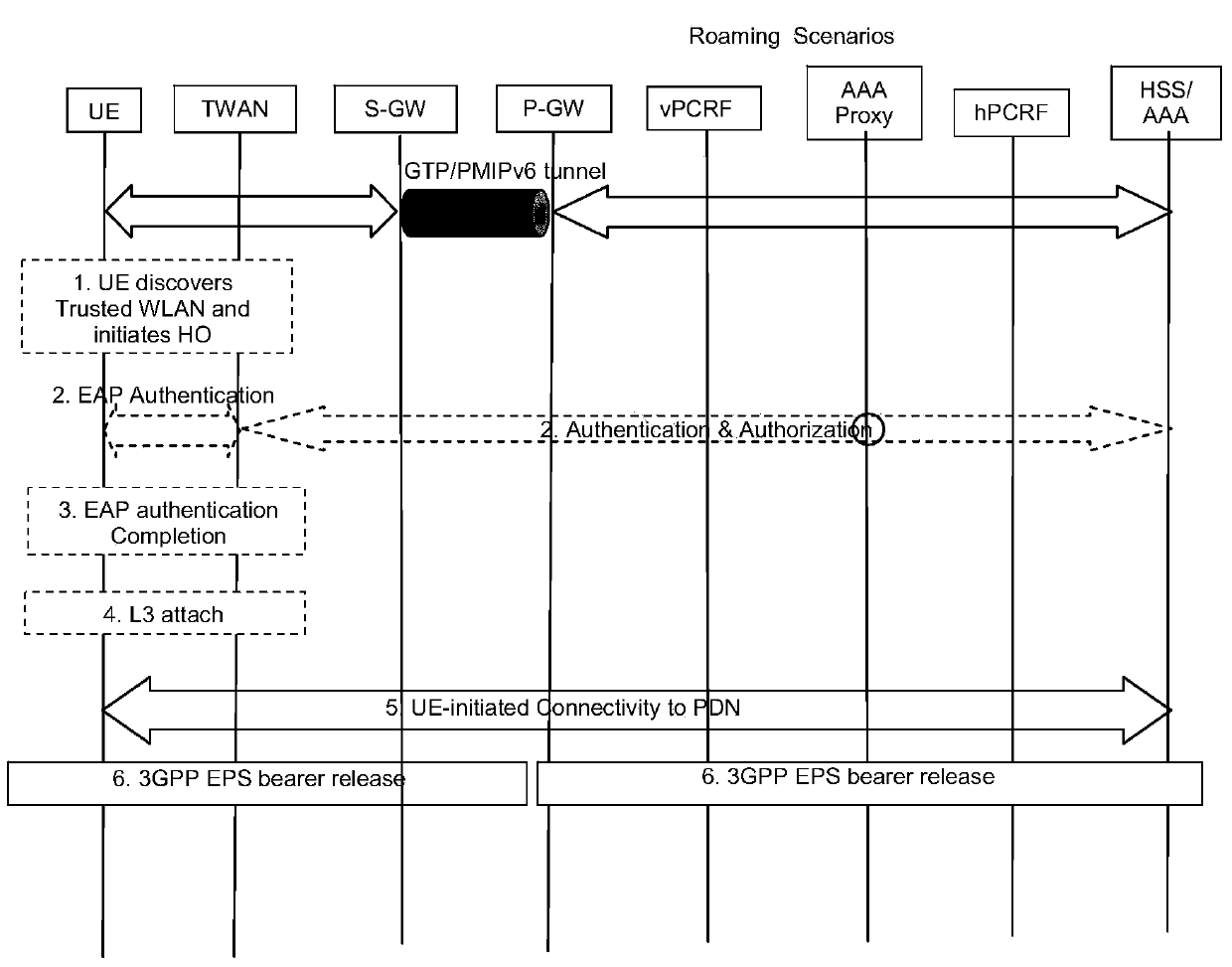
[0085] This embodiment introduces the process of UE switching from 3GPP access to trusted non-3GPP access.
[0086] see Figure 4 , the figure shows the scene of the second embodiment, Figure 4 The shown scenario shows the control plane function and the transmission function. The session management function controls the establishment and release of the user plane connection. The specific establishment and release process depends on the protocol used by the user plane. The dotted line in the figure indicates the transmission path of the user plane after the UE switches to non-3GPP access. In this scenario: the UE attached to the 3GPP access moves to the coverage of the trusted non-3GPP access network, and the UE decides to switch from the 3GPP access to the trusted non-3GPP access (such as TWAN).
[0087] see Figure 5 , the specific switching process is as follows.
[0088] Step S501, the UE sends a PDN (Packet Data Network) connection request message to the TWAN (Trusted...
no. 3 example
[0099] This embodiment introduces the process of UE switching from 3GPP access to untrusted non-3GPP access. see Figure 6 , the figure shows that the UE attached to the 3GPP access moves to the coverage of the untrusted non-3GPP access network, and the UE decides to switch from the 3GPP access to the untrusted non-3GPP access.
[0100] see Figure 7 , the specific switching process is as follows.
[0101] Step S701, the UE initiates the IKEv2 authentication and tunnel establishment process, and indicates the handover to the intermediate entity during the process;
[0102] Step S702, the intermediate entity searches for the context of the UE according to the IKEv2 message, and sends a connection request to the session management function used by the UE in the source access, and the request message carries the UE identifier and handover prompt;
[0103]Step S703, the session management function sends a connection establishment message to the user plane function that provides...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More