Weak command detection system and realization method and WEB platform
A detection system, weak password technology, applied in transmission systems, electrical components, digital data authentication, etc., can solve problems such as loss of enterprises and users, and achieve the effect of avoiding and solving risks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] The present invention will be further described in detail below in conjunction with examples, but the embodiments of the present invention are not limited thereto.
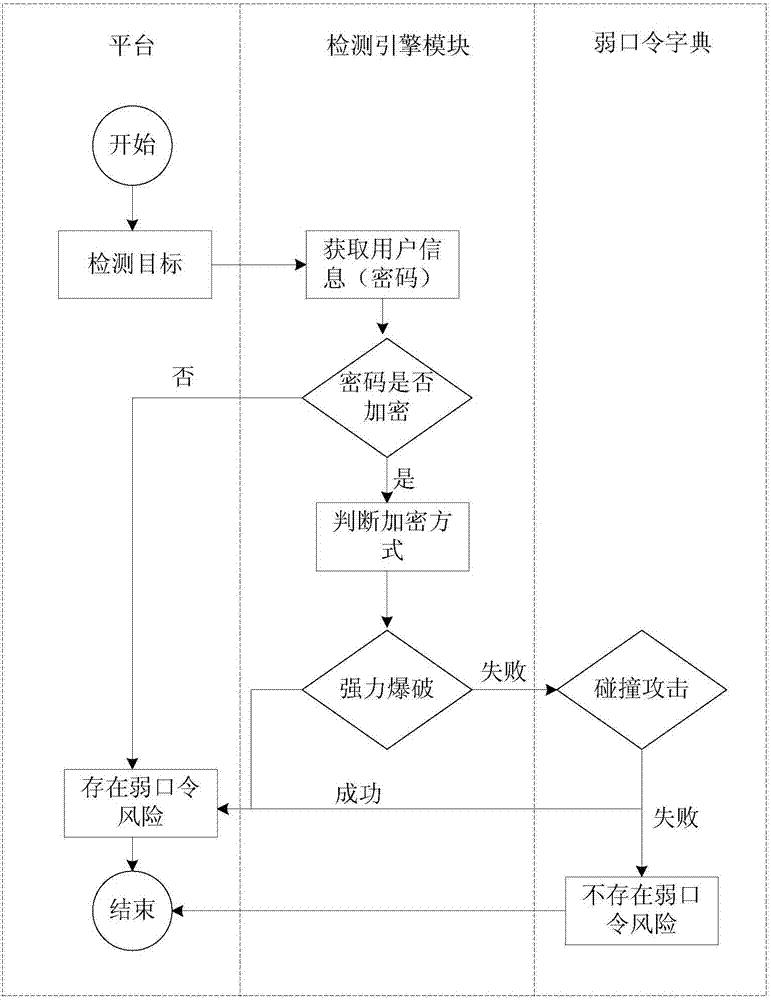
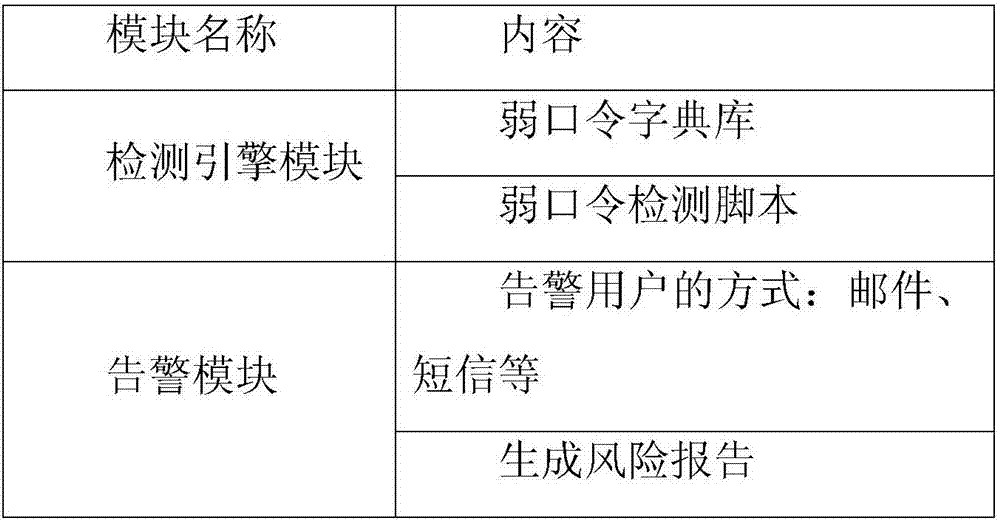
[0031] see figure 1 as shown, figure 1 It shows a flow chart of weak password detection according to an embodiment of the present invention, a method for implementing weak password detection based on a WEB platform, belonging to a cloud security vulnerability detection platform, and integrating a weak password detection script in a vulnerability detection engine. The user logs in to the cloud security vulnerability detection platform, enters the detection target such as the URL, domain name or IP to be detected, selects the weak password detection item in the detection configuration, and after clicking detection, the system will adjust the weak password detection script in the vulnerability detection engine , for detection. The weak password detection script is mainly used to obtain user information, anal...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More