Security risk monitoring method and system, computer equipment and storage medium
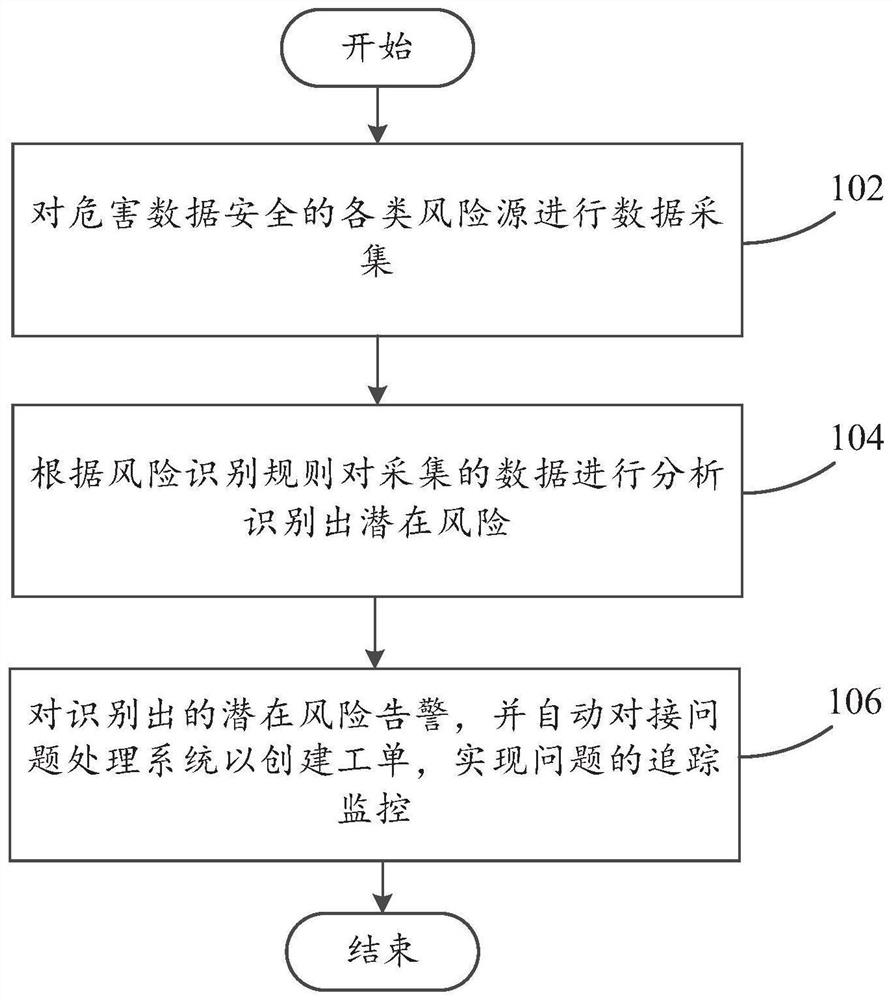
A security risk and monitoring system technology, applied in the computer field, can solve problems such as a single risk monitoring item and cannot be solved in a closed loop, so as to achieve the effect of ensuring security protection capabilities and improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the following will clearly and completely describe the technical solutions of the embodiments of the present invention in conjunction with the accompanying drawings. Obviously, the described embodiments are part of the embodiments of the present invention , but not all examples. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts fall within the protection scope of the present invention.
[0043] Before introducing the embodiments of the present invention, several concepts are clarified:
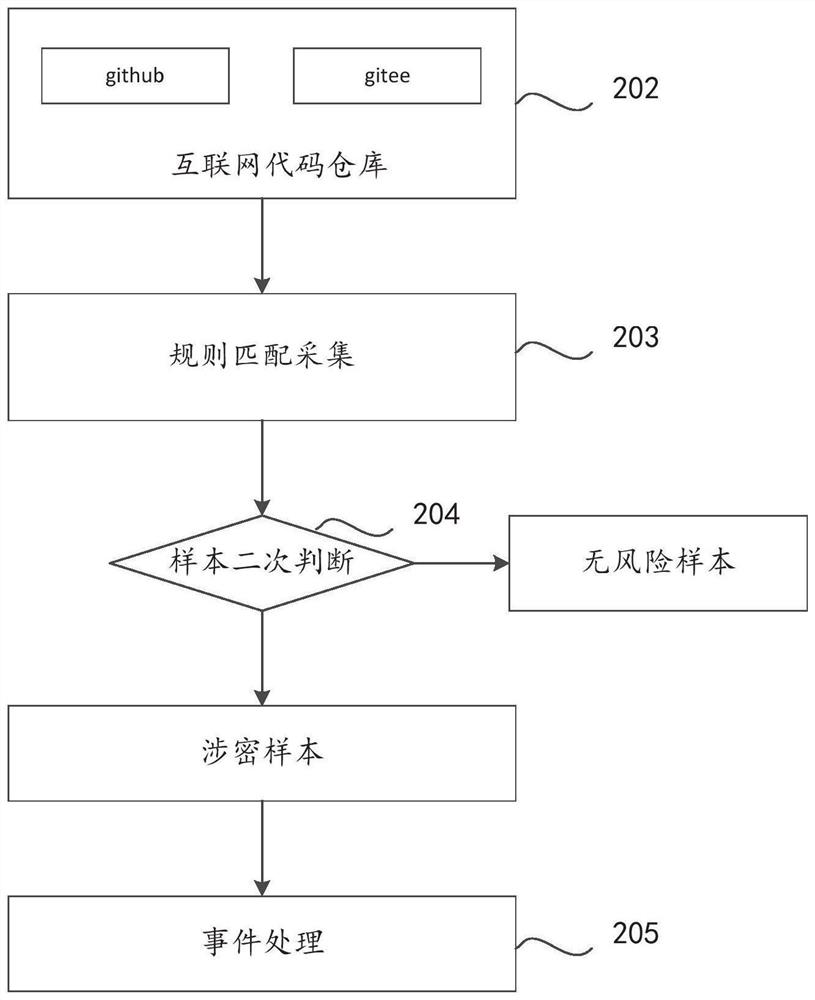
[0044] Internet Code Warehouse: A Code Hosting Platform for Open Source and Proprietary Software Projects
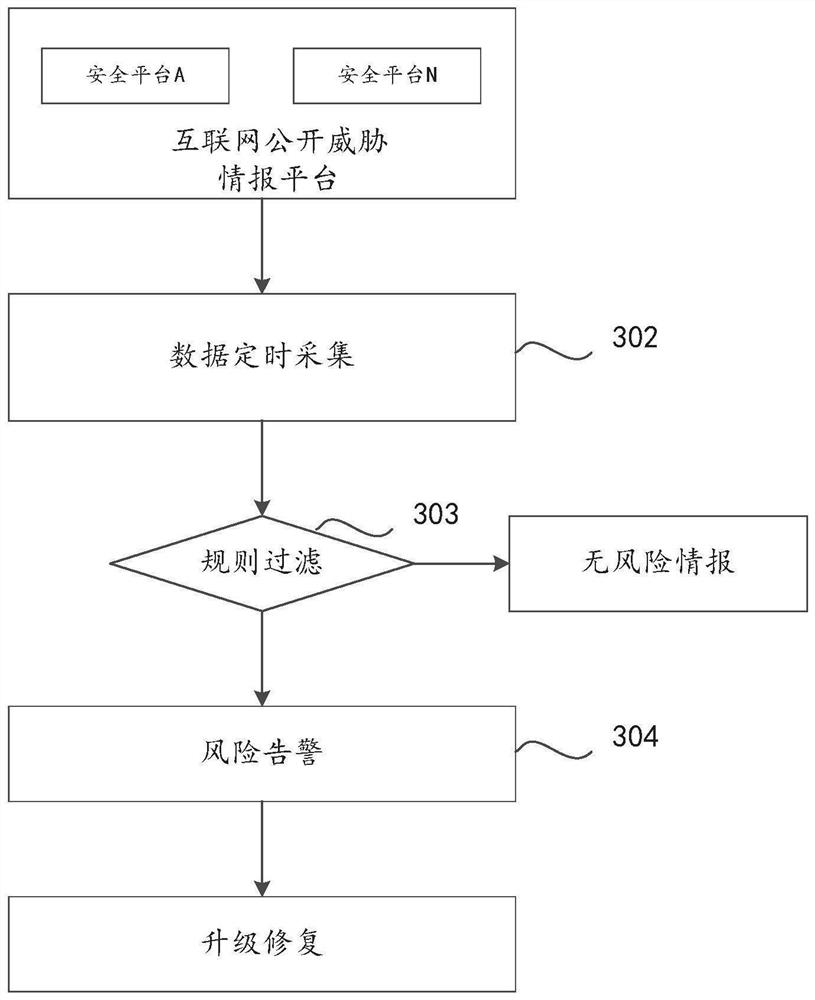
[0045] IDS: According to the configured security policy, monitor various attack behaviors to ensure the confidentiality, integrity and availability of networ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More