Big data platform access control method and server
A big data platform and access control technology, applied in the field of communication, can solve the problem of inability to access terminal devices
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
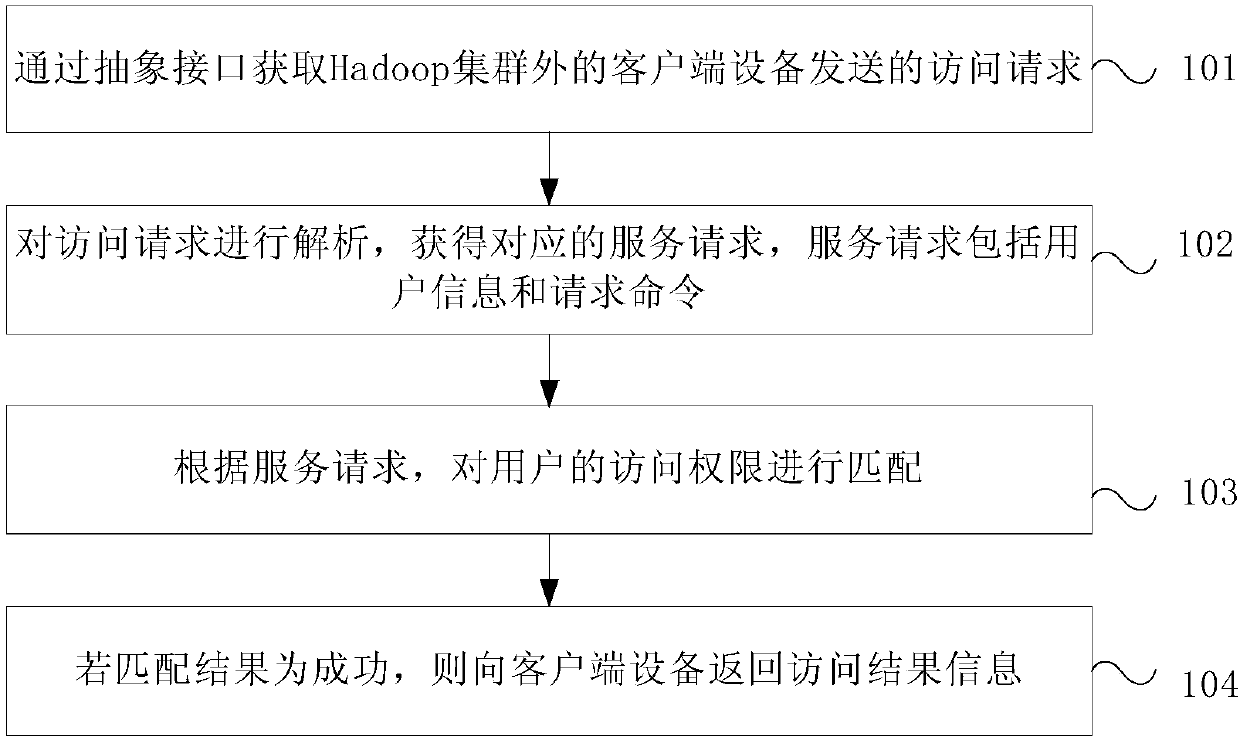
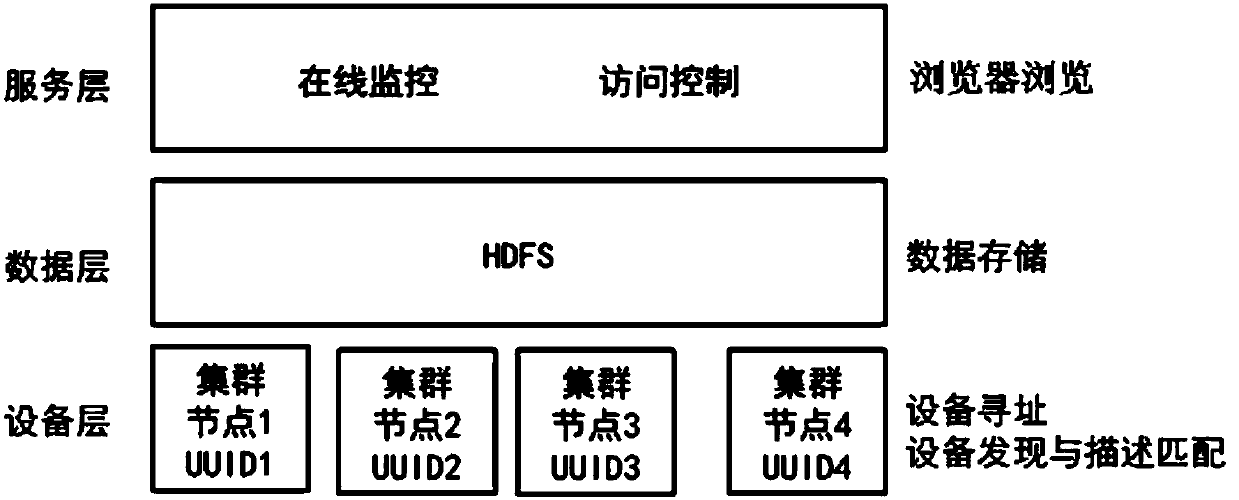
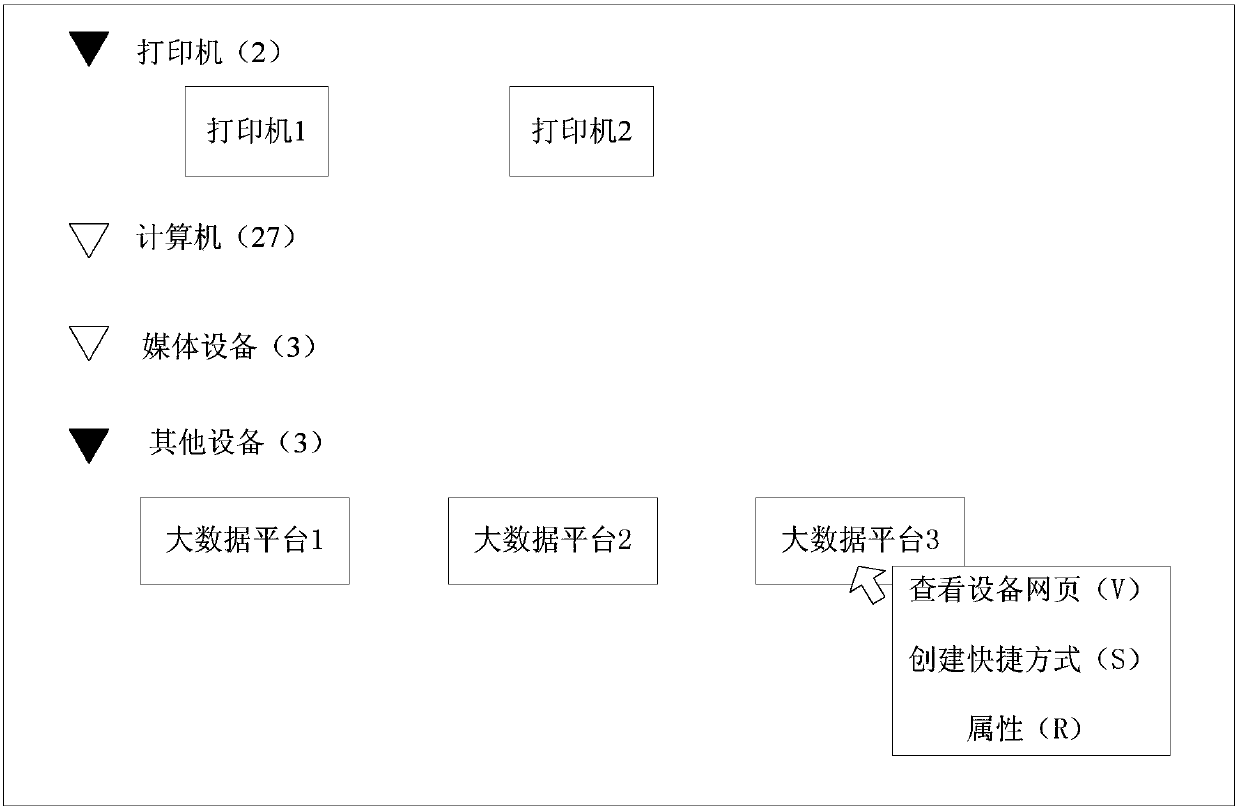
[0032] This embodiment provides an access control method for a big data platform, which is used to control client devices outside the Hadoop cluster to automatically discover the big data platform, and access the big data platform through a visualized browser interface. The execution subject of this embodiment is the master node device in the Hadoop cluster, and the master node device may be a server.
[0033] Such as figure 1 As shown, it is a schematic flow diagram of the access control method of the big data platform provided by this embodiment, and the method includes:
[0034] Step 101, obtain an access request sent by a client device outside the Hadoop cluster through an abstract interface.
[0035] Among them, the abstract interface is the interface established by deploying the DPWS framework on the node devices in the Hadoop cluster.
[0036] Step 102, analyze the access request to obtain the corresponding service request, the service request includes user informatio...
Embodiment 2
[0060] This embodiment provides a further supplementary description of the access control method of the big data platform provided in the first embodiment.
[0061] On the basis of the first embodiment above, optionally, if the matching result is failure, return access failure information to the client device; generate and store user access log information.
[0062] Specifically, when the data to be accessed by the user does not match the user's authority, information about access failure is returned to the client device, and user access log information is generated. The user access log information may specifically include access time, specific Operation (delete, query, modify, etc.), user name, password and other information.
[0063] Optionally, after step 102, before step 103 or after step 103 or at the same time as step 103, the method may further include: according to the service request, determine one or more corresponding target slave node devices that respond to the se...
Embodiment 3
[0073] This embodiment provides a server for executing the access control method of the big data platform in the first embodiment above, and the server can be used as a master node server in a Hadoop cluster.
[0074] Such as Figure 7 As shown, it is a schematic structural diagram of the server provided in this embodiment. The server 30 includes a receiving module 31 , an analyzing module 32 , a matching module 33 and a sending module 34 .
[0075] Wherein, the receiving module 31 is used to obtain the access request sent by the client device outside the Hadoop cluster through an abstract interface, and the abstract interface is an interface established by deploying the DPWS framework for node devices in the Hadoop cluster; the parsing module 32 is used to parse the access request , to obtain the corresponding service request, the service request includes user information and request command; the matching module 33 is used to match the access rights of the user according to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More