Vulnerability scanner and plug-in scheduling method thereof
A vulnerability scanner and vulnerability scanning technology, applied in the field of network security, can solve the problems of slow scanning speed, taking up a lot of time and memory capacity, and unable to meet the growth rate of plug-ins, so as to improve the scanning speed and save memory space.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The technical solutions of the present invention will be clearly and completely described below in conjunction with the accompanying drawings and embodiments of the present invention. The following embodiments are only preferred embodiments of the present invention, not all embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without making creative efforts belong to the protection scope of the present invention.
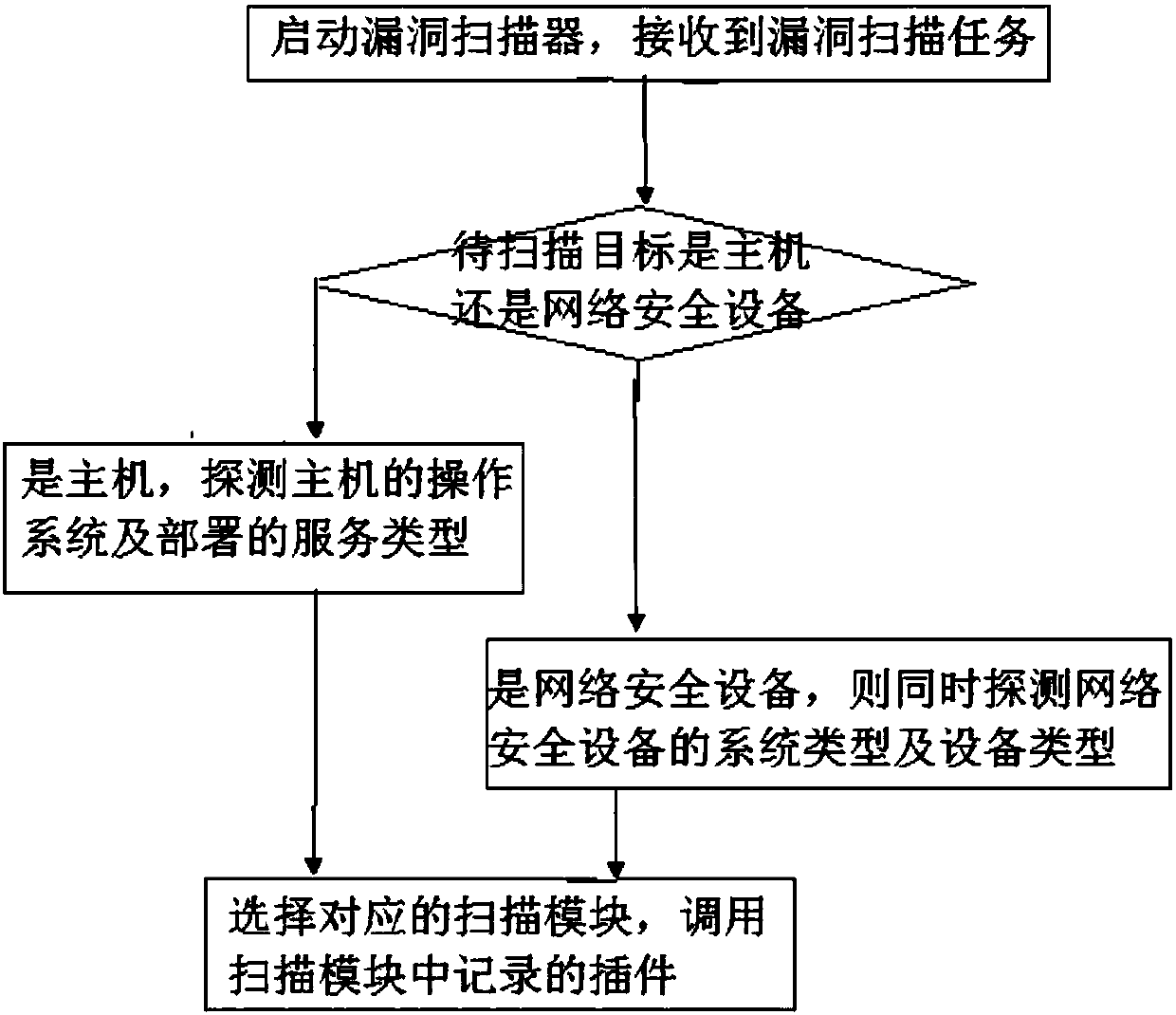
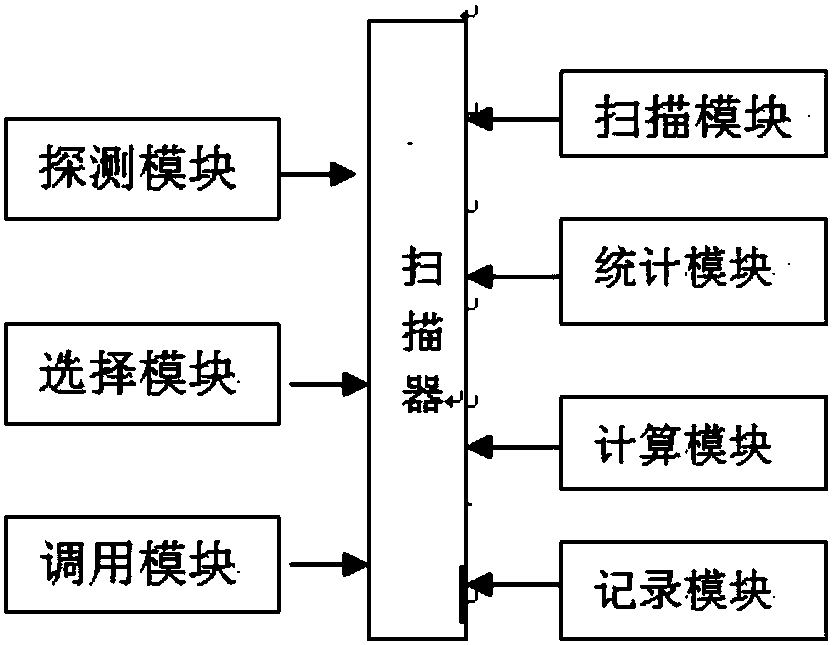
[0030] The present invention provides a vulnerability scanning plug-in scheduling method, such as figure 1 , specifically through the following steps:
[0031] After starting the vulnerability scanner and receiving the vulnerability scanning task, identify whether the target to be scanned is a host or a network security device; use the nmap tool to detect the target to be scanned, and if the target to be scanned is a host, simultaneously detect the operating system and deployed services of ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More