Verification method and device, server and terminal
A server and terminal technology, applied in the computer field, can solve problems such as loss of verification and easy cracking of verification codes, and achieve high security and hard-to-crack effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0085] The technical solutions in the embodiments of the present invention will be described below with reference to the drawings in the embodiments of the present invention.
[0086] The embodiment of the present invention discloses a verification method, device, server and terminal, which will be described in detail below.
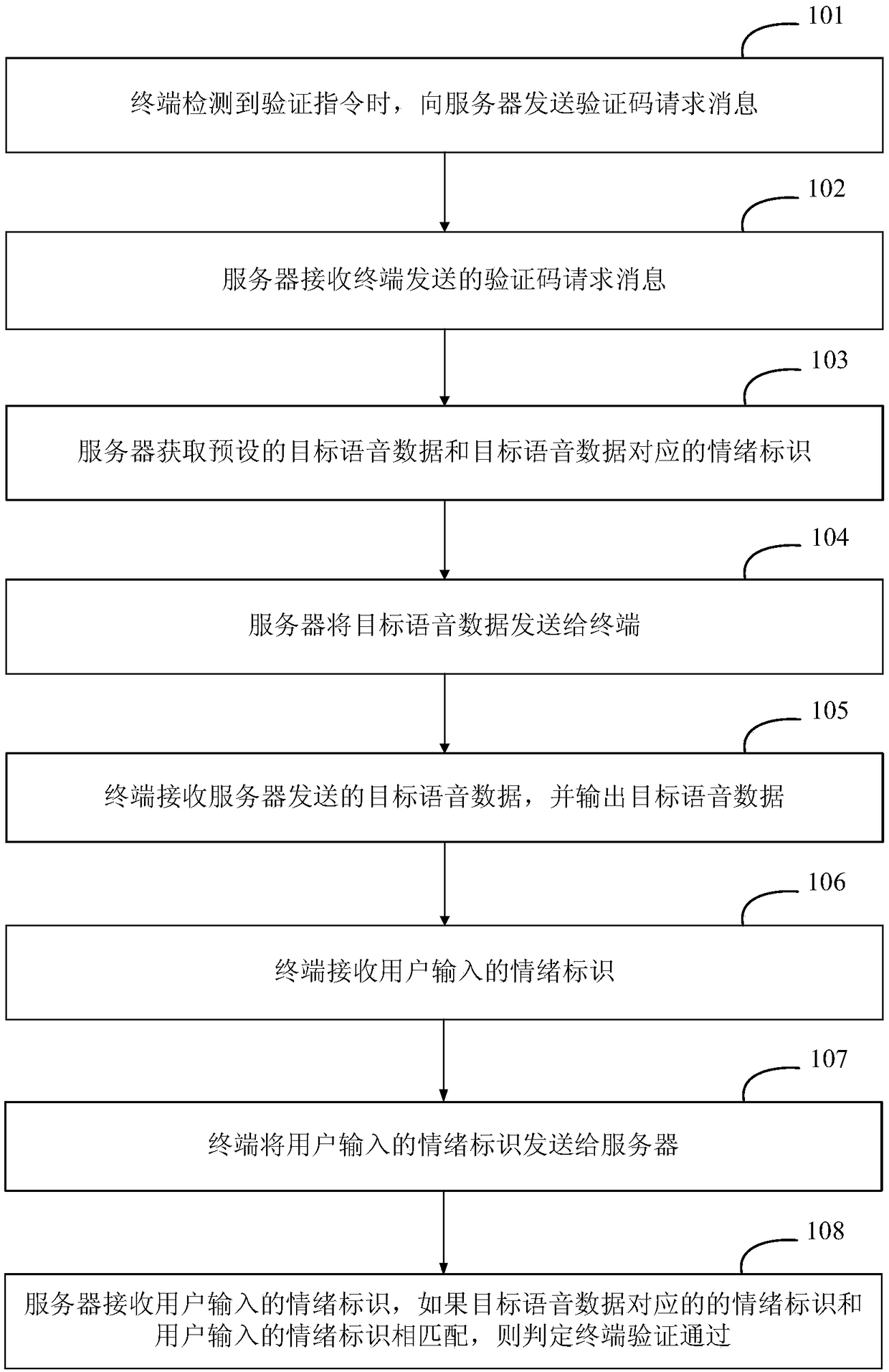
[0087] Such as figure 1 as shown, figure 1 A flowchart of a verification method provided by an embodiment of the present invention includes the following steps:
[0088] Step 101, when the terminal detects a verification instruction, it sends a verification code request message to the server.
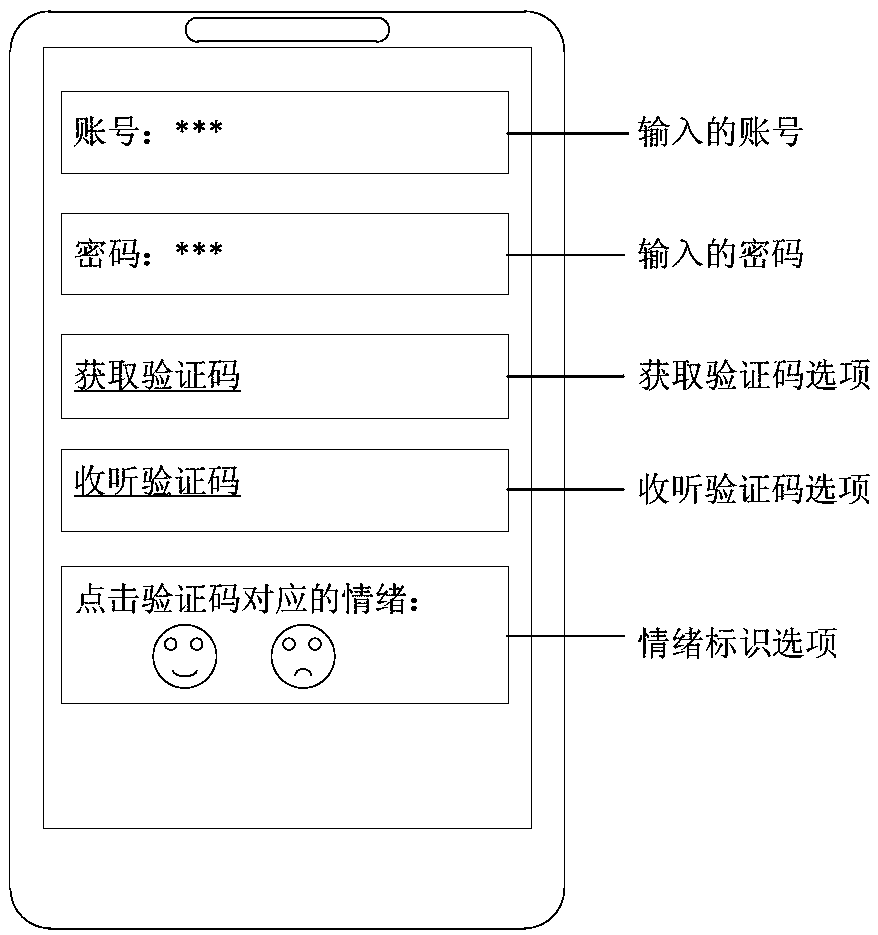
[0089] In the implementation, the user can use the network service through the terminal, and when using some network services, authentication will be required. For example, when a user logs in to an email account, an input box for entering the account number and password will be displayed on the login interface, and an option for obtaining a verification code c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More