An Android privacy disclosure behavior detection method and technology based on information flow
A detection technology and privacy leakage technology, applied in the field of mobile security privacy leakage behavior detection technology and system, can solve the problems of dynamic analysis limitation, program interruption, etc., and achieve the effects of expanding the scope, improving the detection rate, and high code coverage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The present invention will be further described below in conjunction with accompanying drawings and examples.
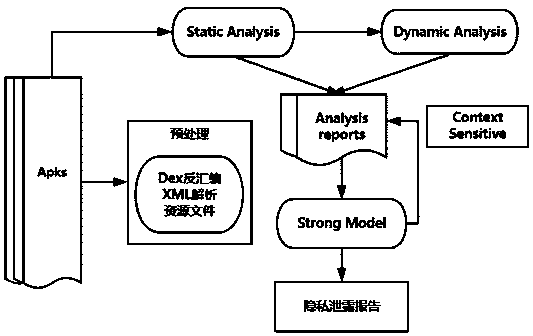
[0027] Such as figure 1 As shown, a method for identifying Android privacy information leakage behavior based on information flow analysis, the steps are as follows.
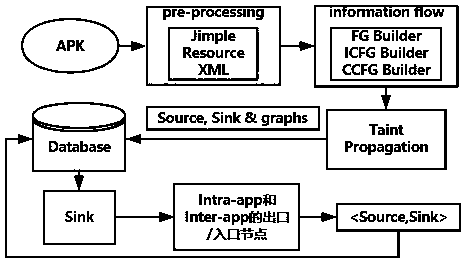
[0028] The control flow graph building block is based on source code analysis and Jimple intermediate representation. The source code contains method call parameters for component communication, corresponding permissions and intent attributes. The intent information is used to match the called component and transmit privacy information. In order to match the calling component and the called Invoke components, use intent information to match the filter rules of components, and call components need corresponding permissions to access the called components. In order to detect whether there is a privacy information leakage behavior in component communication, the invention defines the API of the cal...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More