A method for protecting the interaction integrity and confidentiality of a trusted application and a common application
A common application and integrity technology, applied in the field of protecting the interactive integrity and confidentiality of trusted applications and common applications, can solve problems such as direct attacks without consideration
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0053] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention. Obviously, the described embodiments are part of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts shall fall within the protection scope of the present invention.
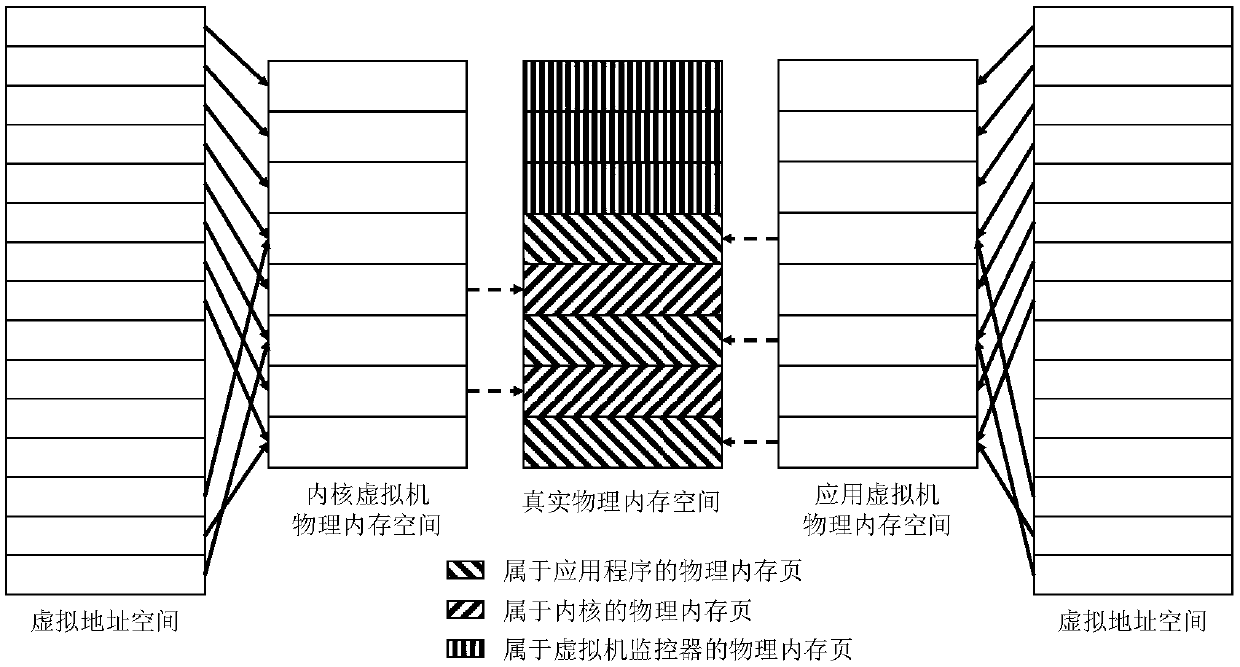
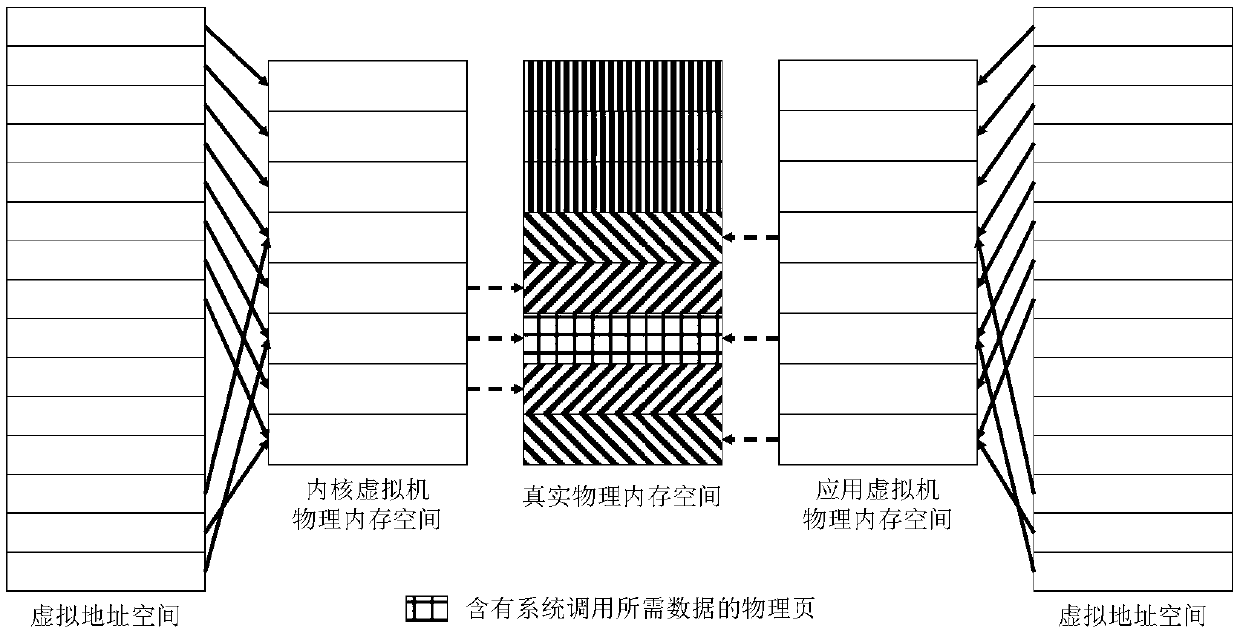
[0054] The principle of the present invention is to place the kernel and the application of the rich execution environment in different virtual machines to run, and realize the transparent compatibility with the kernel and the application with the support of the virtual machine monitor and the user state library.
[0055] Concrete steps of the present invention include:
[0056] 1. When an ordinary application requests protection, the user state library ac...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More