A method for using a quantum key through IKEv2 negotiation
A quantum key and quantum technology, applied in the field of communication, can solve the problem of insufficient security of network encryption methods, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0050] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the drawings in the embodiments of the present invention. Obviously, the described embodiments It is a part of embodiments of the present invention, but not all embodiments.
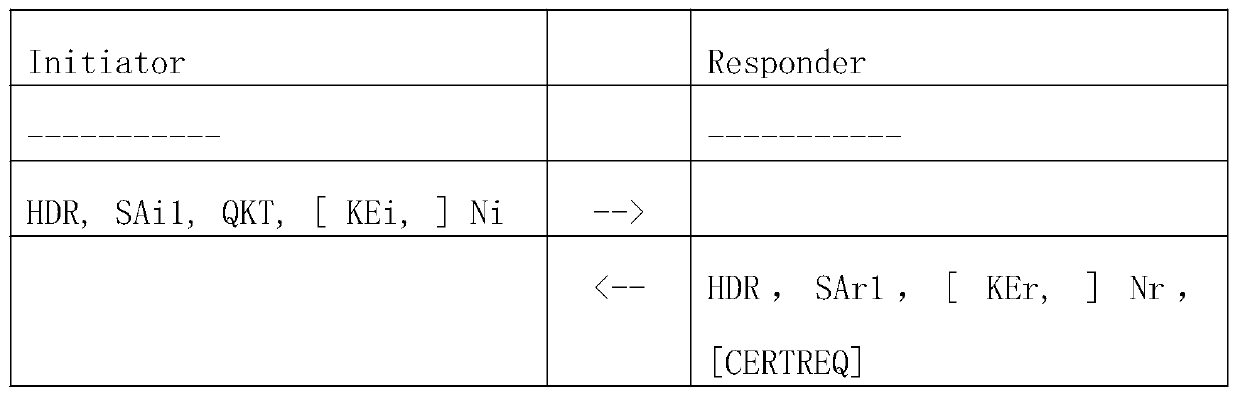
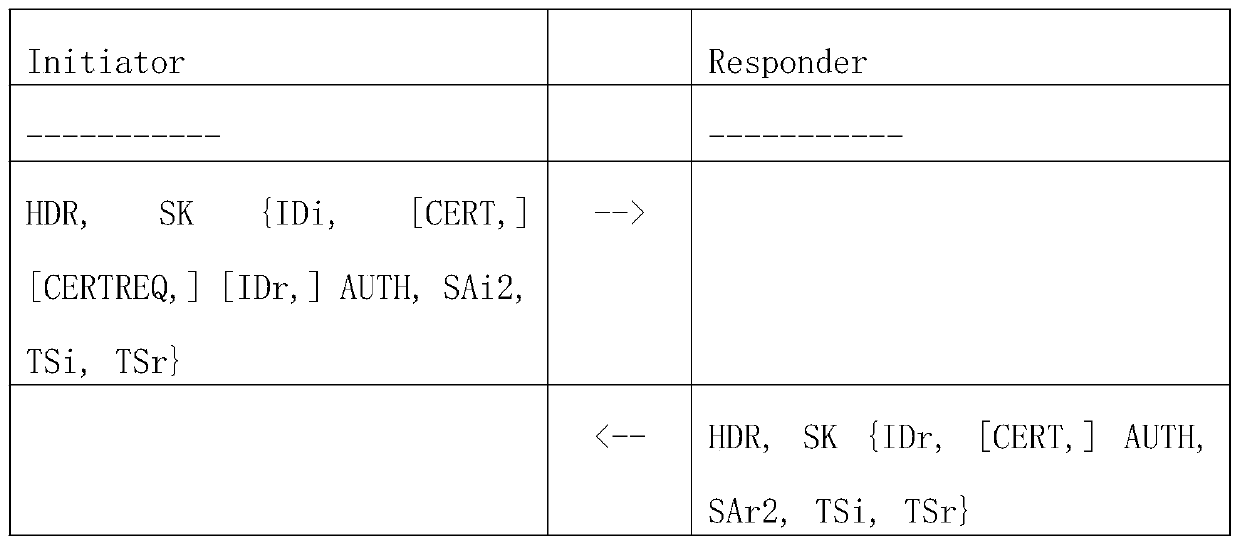
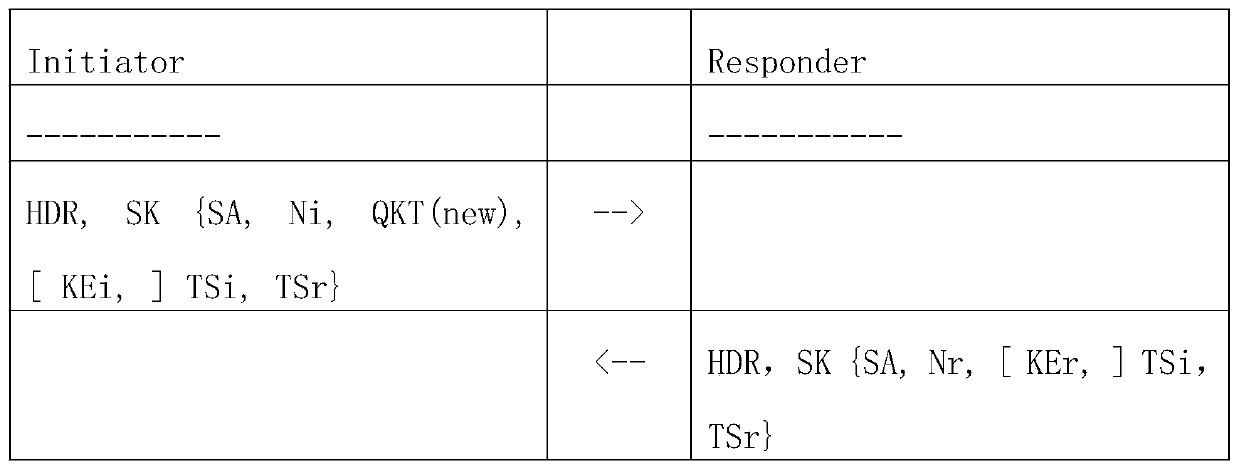
[0051] Such as figure 1 As shown, the IKEv2 negotiation method described in this embodiment uses a quantum key, adopts the IKEv2 pre-shared key mode, and uses the quantum key to establish an IPESC tunnel. The main steps are as follows:
[0052] S100. The initiator and the responder use the quantum key distribution protocol QKD to generate a quantum key QK, and use QK to replace or combine the shared key g^ir generated by Diffie-Hellman key exchange;
[0053] S200. Use the quantum key ticket QKT to uniquely identify the quantum key QK generated this...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More