System and method for detecting malicious behaviors in computer system
A computer system and malicious technology, applied in computer security devices, computing, special data processing applications, etc., can solve the problems of insufficient detection of malicious activities and increased complexity of the system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0020] In an embodiment, a functional relationship means a type of association (relationship) between objects in which each object changes concurrently with each other. In functional relations, the main indicators of causality are lacking, especially productivity (objects do not generate each other), temporal asymmetry (objects coexist, one of them does not precede the other) and irreversibility.
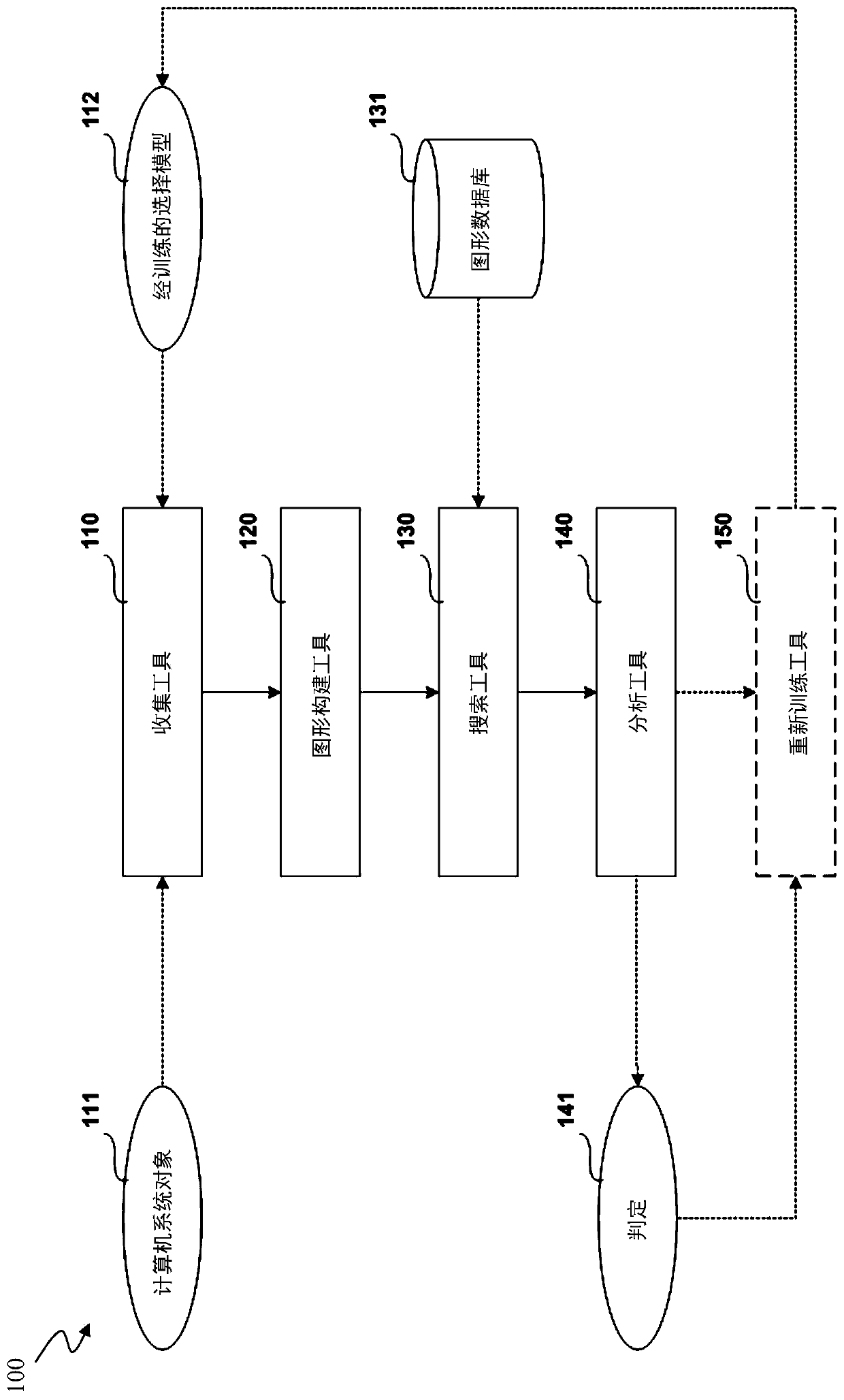
[0021] refer to figure 1 , depicts a block diagram of a system 100 for detecting malicious activity in a computer system, according to an embodiment. In an embodiment, the system 100 generally includes a collection tool 110 , a trained selection model 112 , a graph construction tool 120 , a graph database 131 , a search tool 130 and an analysis tool 140 . Optionally, system 100 may include retraining tool 150 . As will be described, system 100 operates on computer system object 111 and will include one or more decisions 141 .
[0022] Collection tool 110 is configured to collect...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com