Method and device for processing web application programs
A processing method and web application technology, applied in the computer field, can solve problems such as low security, achieve the effects of improving security, strengthening protection, and increasing the difficulty of cracking
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
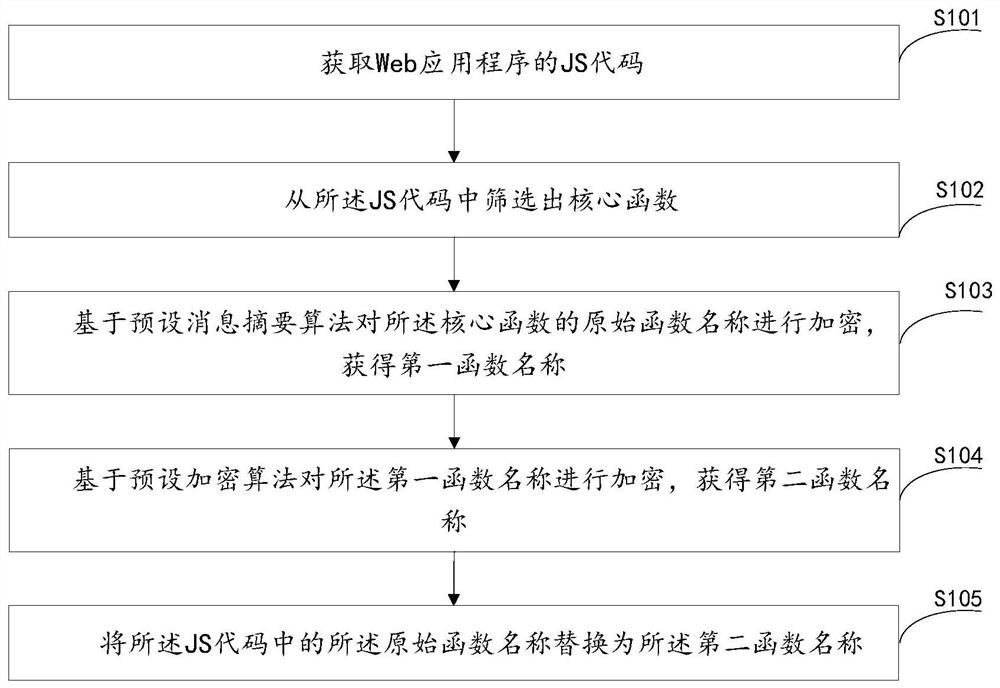
[0048] This embodiment provides a processing method for a Web application, such as figure 1 As shown, the method includes:
[0049] Step S101: Obtain the JS code of the web application.
[0050] Specifically, JS code is JavaScript code, which is a literal scripting language, and also a dynamic type, weak type, and prototype-based language with built-in support types. Usually used to write web applications.
[0051] Step S102: Filter out core functions from the JS code.
[0052] Specifically, the JS code includes implementation codes for core functions and security functions of the web application, and these codes are implemented by using functions, that is, core functions.
[0053]In an optional implementation, in order to better conceal the core functions, this implementation will also filter out some non-core functions, and the number of non-core functions can be selected according to needs, for example, the number of core functions is 50, the number of non-core function...
Embodiment 3
[0117] Based on the same inventive concept, the present application also provides a computer-readable storage medium 300 on which a computer program 311 is stored, and when the program is executed by a processor, the method in Embodiment 1 is implemented.
[0118] Specifically, the above program is configured to perform the following steps:
[0119] Get the JS code of the web application;
[0120] Filter out core functions from the JS code;
[0121] Encrypting the original function name of the core function based on a preset message digest algorithm to obtain a first function name;
[0122] Encrypting the first function name based on a preset encryption algorithm to obtain a second function name;
[0123] replacing the original function name in the JS code with the second function name.
Embodiment 4
[0125] Based on the same inventive concept, this application also provides a kind of computer equipment, please refer to Figure 4 , including a memory 401, a processor 402, and a computer program 403 stored in the memory and operable on the processor, and the processor 402 implements the method in Embodiment 1 when executing the program.
[0126] Specifically, the above processor is configured to perform the following steps:
[0127] Get the JS code of the web application;
[0128] Filter out core functions from the JS code;
[0129] Encrypting the original function name of the core function based on a preset message digest algorithm to obtain a first function name;
[0130] Encrypting the first function name based on a preset encryption algorithm to obtain a second function name;
[0131] replacing the original function name in the JS code with the second function name.
[0132] The above one or more technical solutions in the embodiments of the present application have ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More