Security risk assessment method for block chain
A security risk and blockchain technology, applied in computer security devices, instruments, payment systems, etc., can solve problems such as researching blockchain security risks, blockchain security risk impacts, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
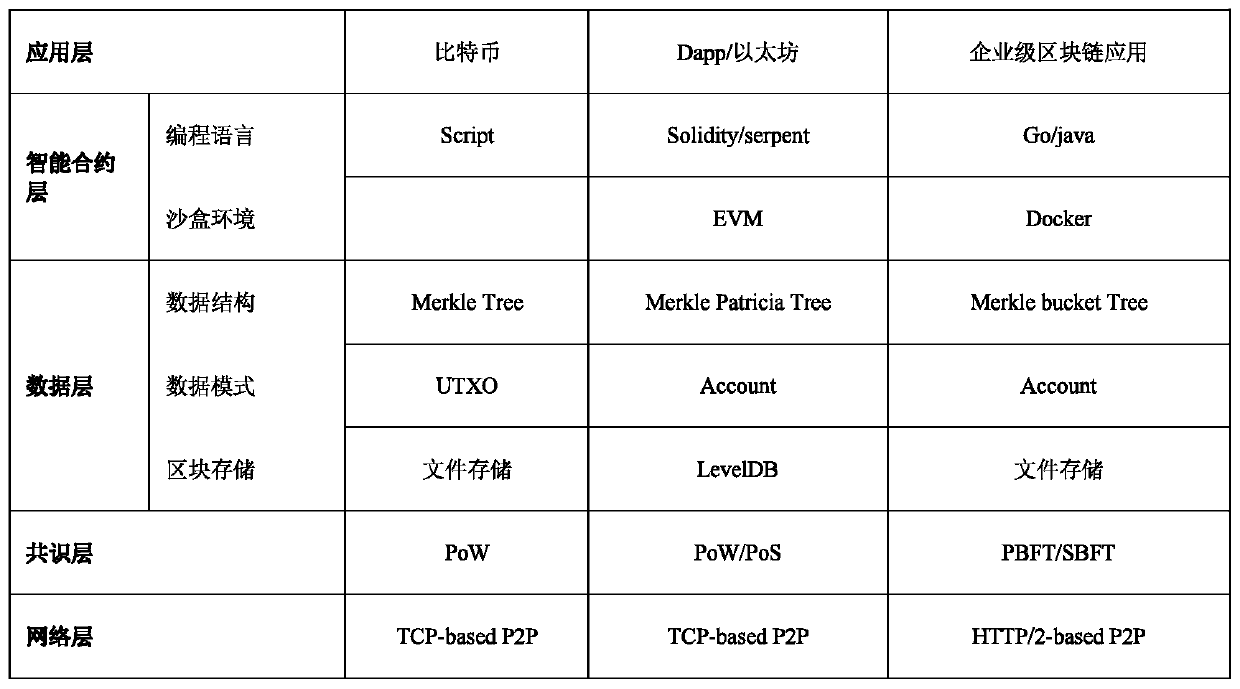
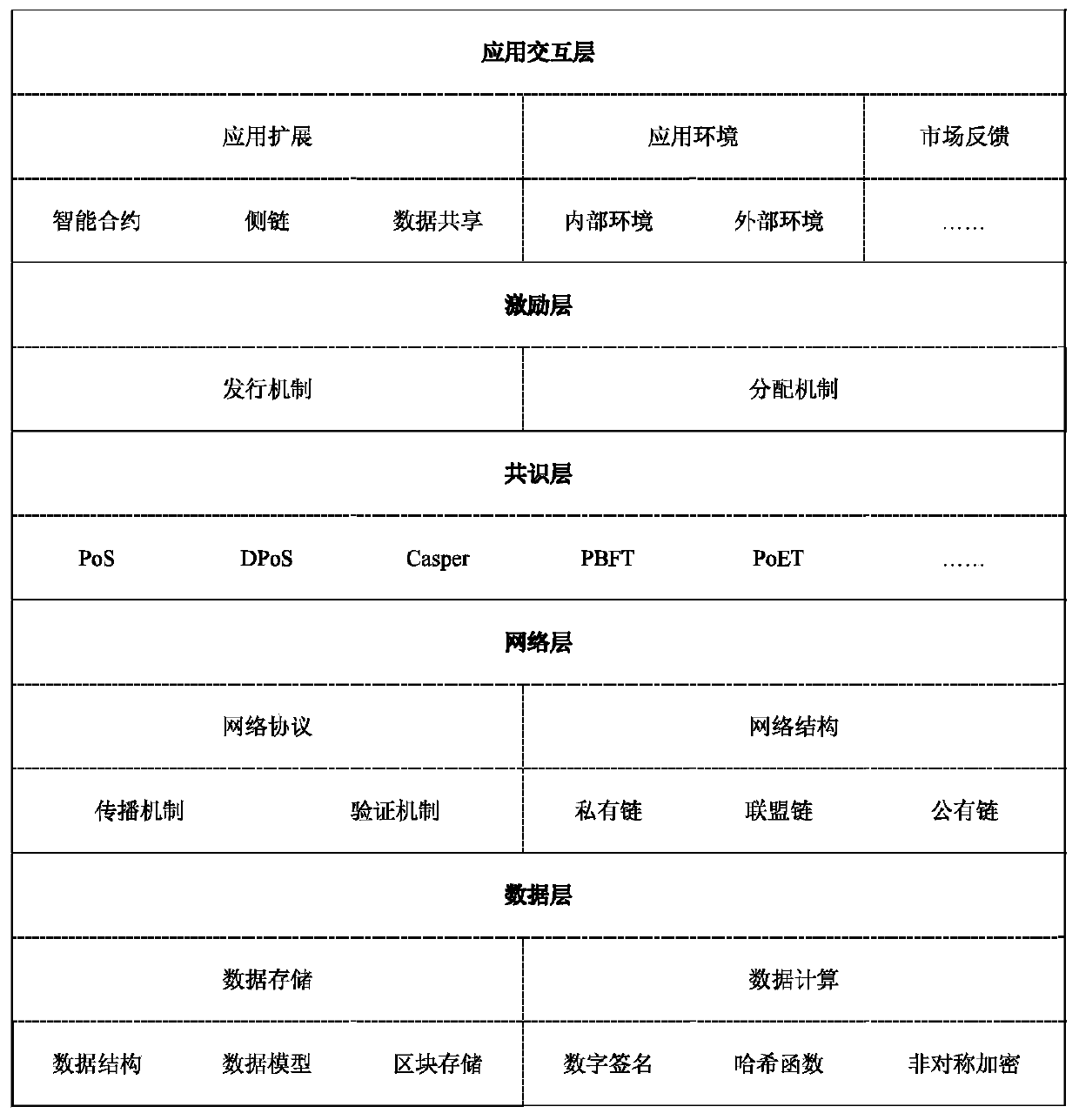
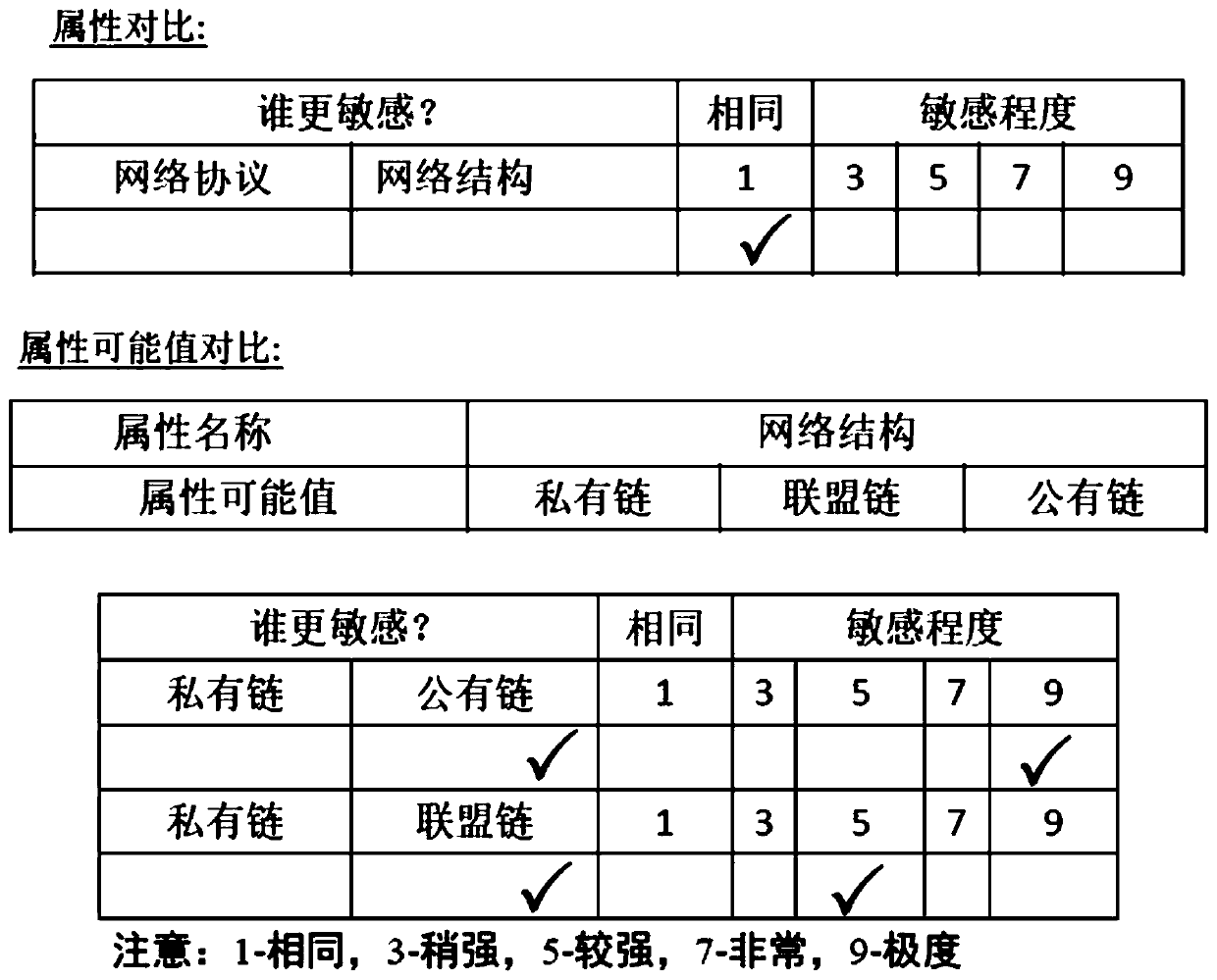
Method used
Image
Examples
Embodiment Construction
[0110] Below in conjunction with example the present invention will be further described:
[0111] 1) Description of the experimental environment
[0112] So far, there are only two authoritative institutions in the world that have conducted technical security risk assessments on blockchains and released data. One is the China Information Industry Development Center - CCID Blockchain Research Institute. The assessment object is public chains, and the number of assessments is 31. Items, the evaluation content includes the realization of functions, basic performance, security and degree of centralization; the other is the independent rating agency in the United States - Weiss Ratings, the evaluation object is the public chain, the number of evaluations is 93, and the evaluation content includes functions, basic performance, security sex and energy management. In order to verify the feasibility of this model, this experiment selected 30 well-known public chain systems as the exp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More