Permission processing method and device and permission control method and device
A processing method and permission control technology, applied in the field of data processing, can solve problems such as cumbersome configuration process, error-prone, and high system intrusion
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0098] In the following description, numerous specific details are set forth in order to provide a thorough understanding of the application. However, the present application can be implemented in many other ways different from those described here, and those skilled in the art can make similar promotions without violating the connotation of the present application. Therefore, the present application is not limited by the specific implementation disclosed below.
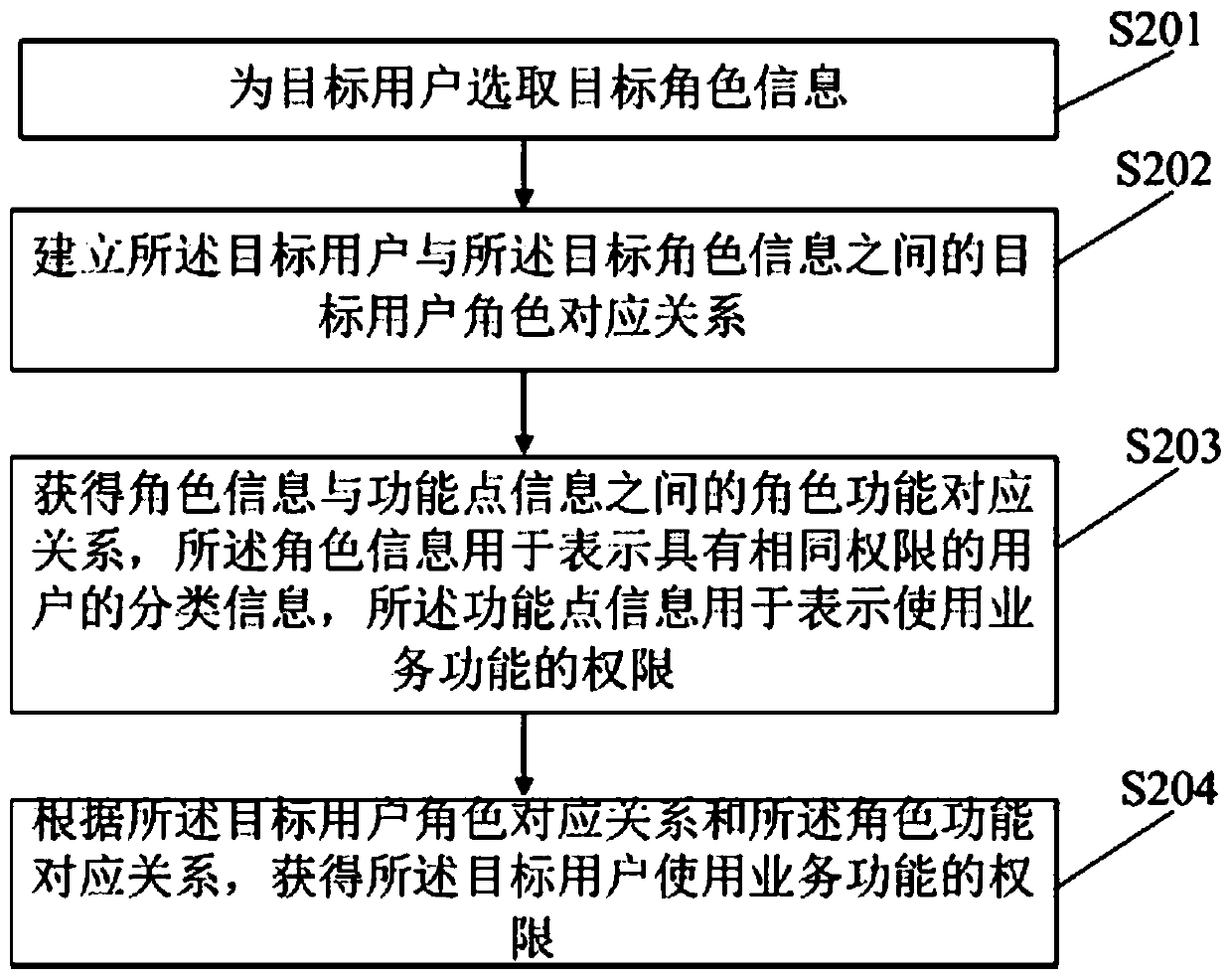
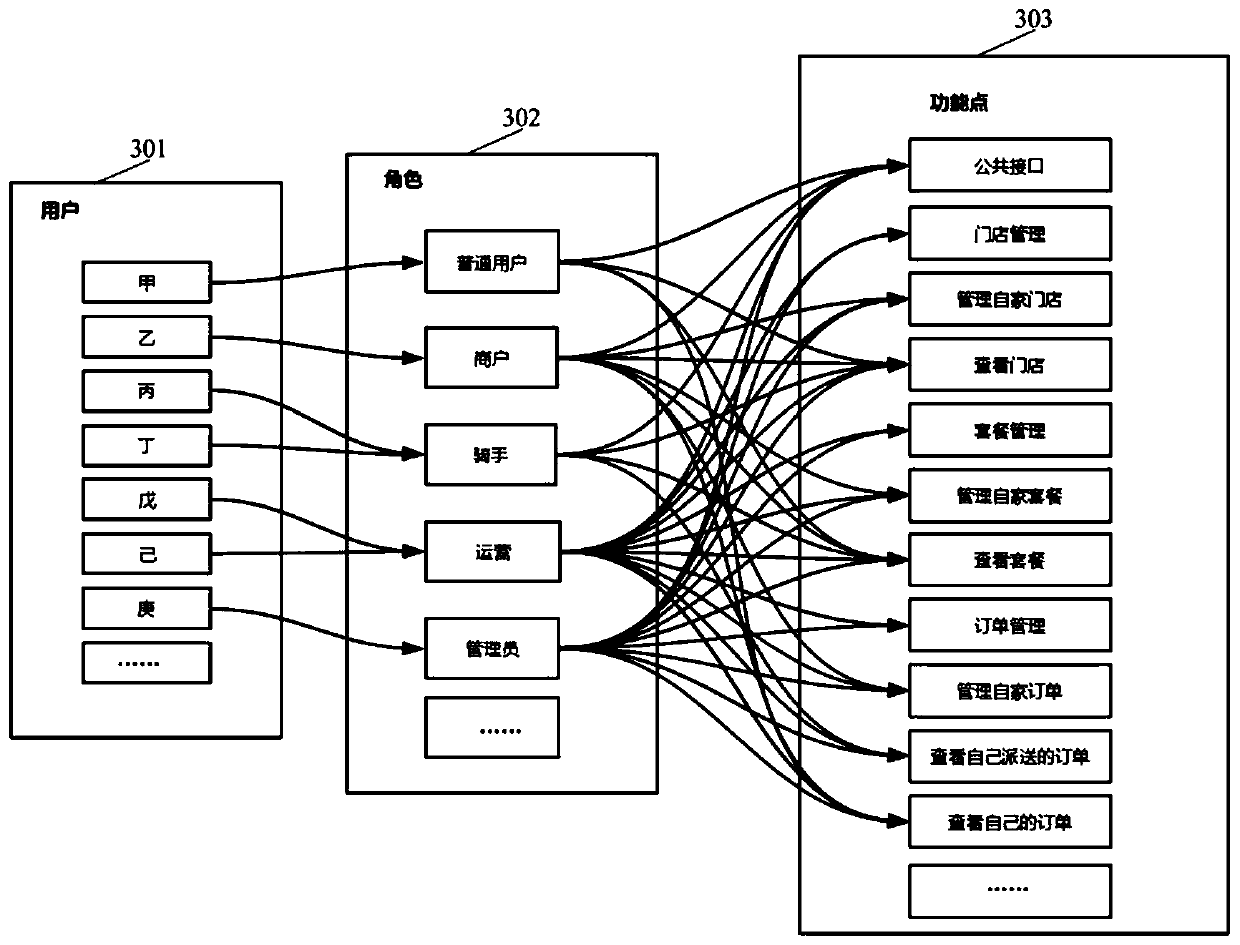
[0099] The present application provides a permission processing method, device and electronic equipment. The present application also relates to a permission control method, device and electronic equipment. The present application also relates to another permission processing method, device and electronic equipment. Each will be described in detail in the following examples.
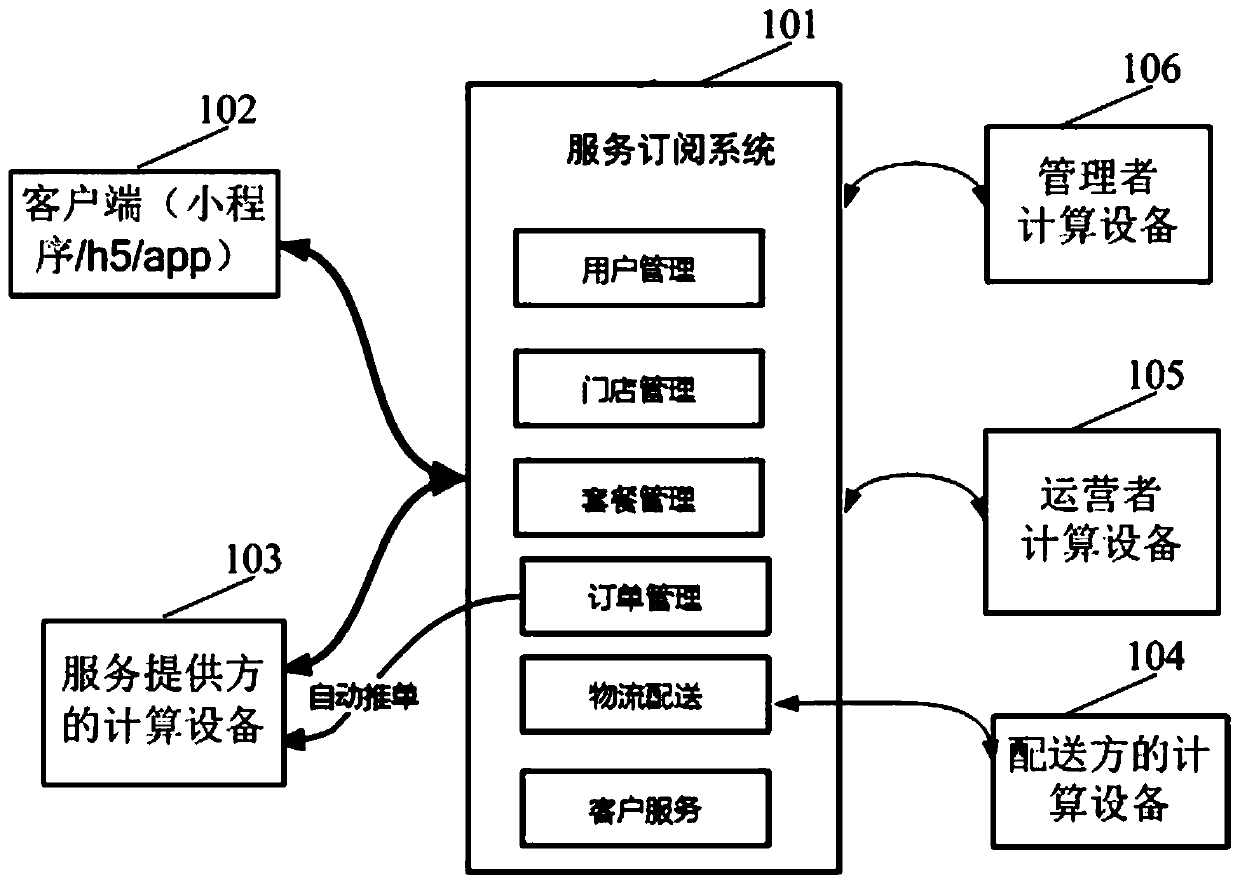
[0100] For ease of understanding, the system environment of the service subscription system deploying the authorization processing method is...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More