Mobile storage system access control method and device supporting service security mark
A technology of security marking and mobile storage, applied in the computer field, can solve the problems of unsupported access environment control and fine-grained data control, and achieve the effect of improving access control and data control capabilities
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0018] Preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
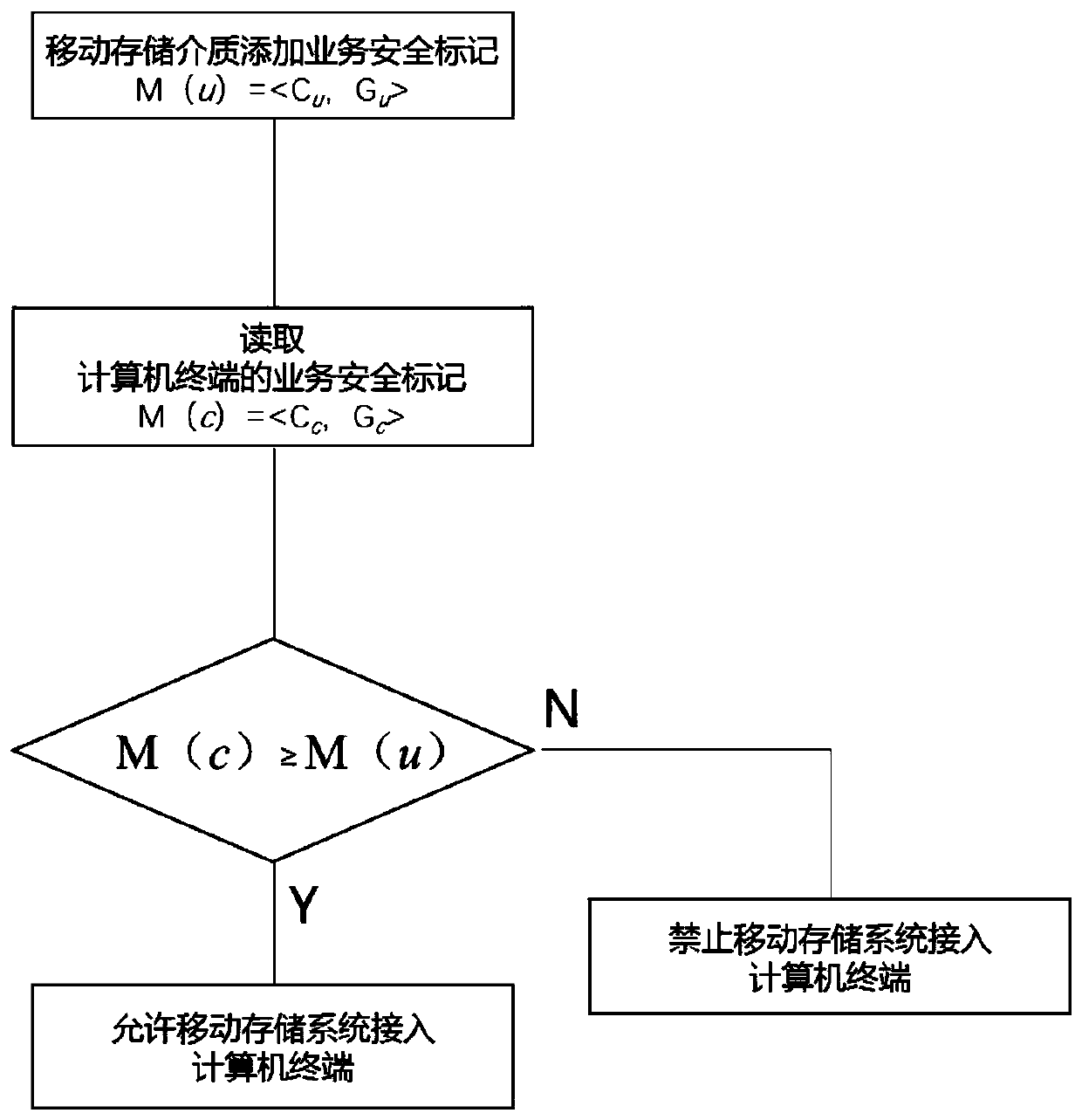
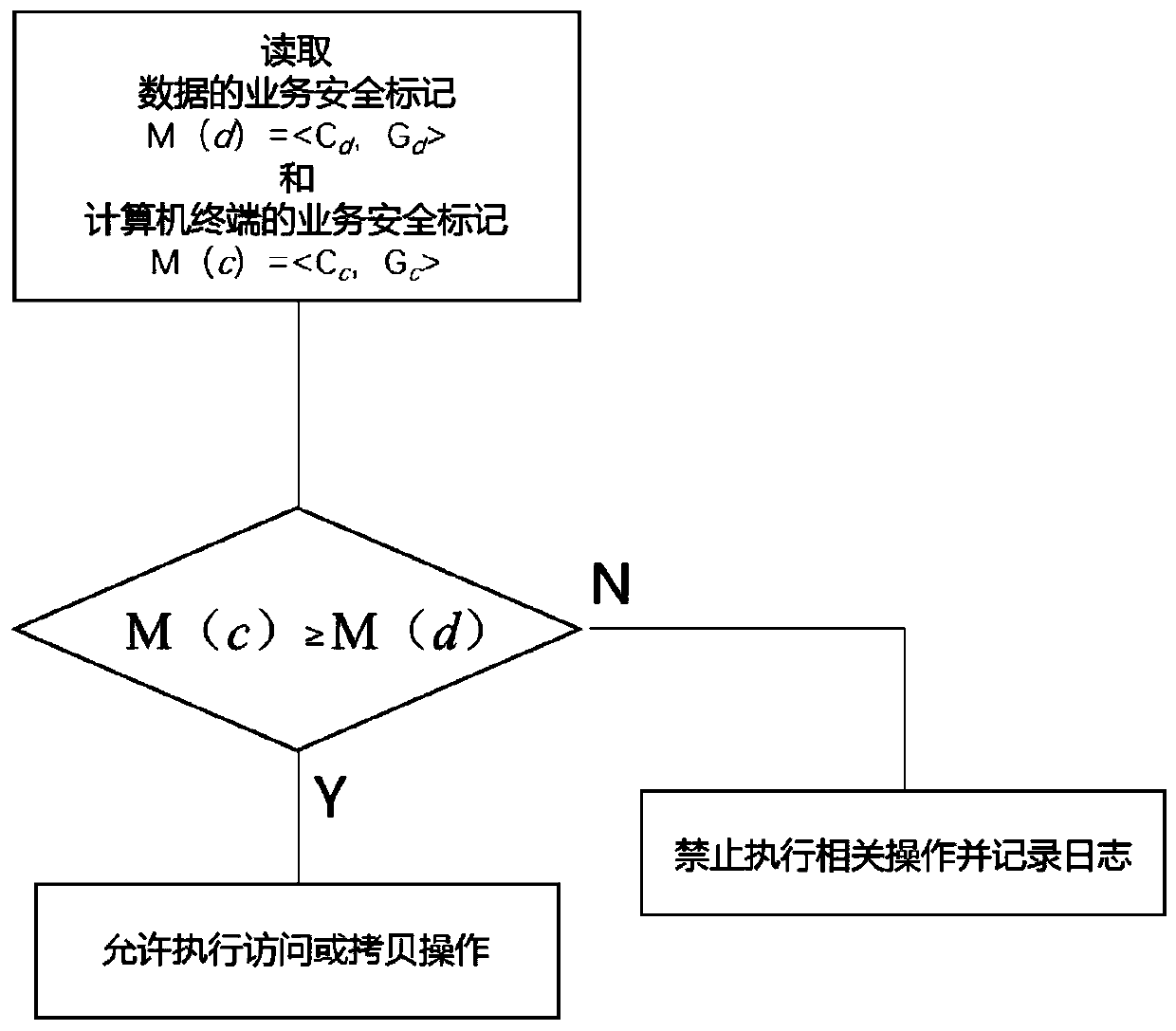
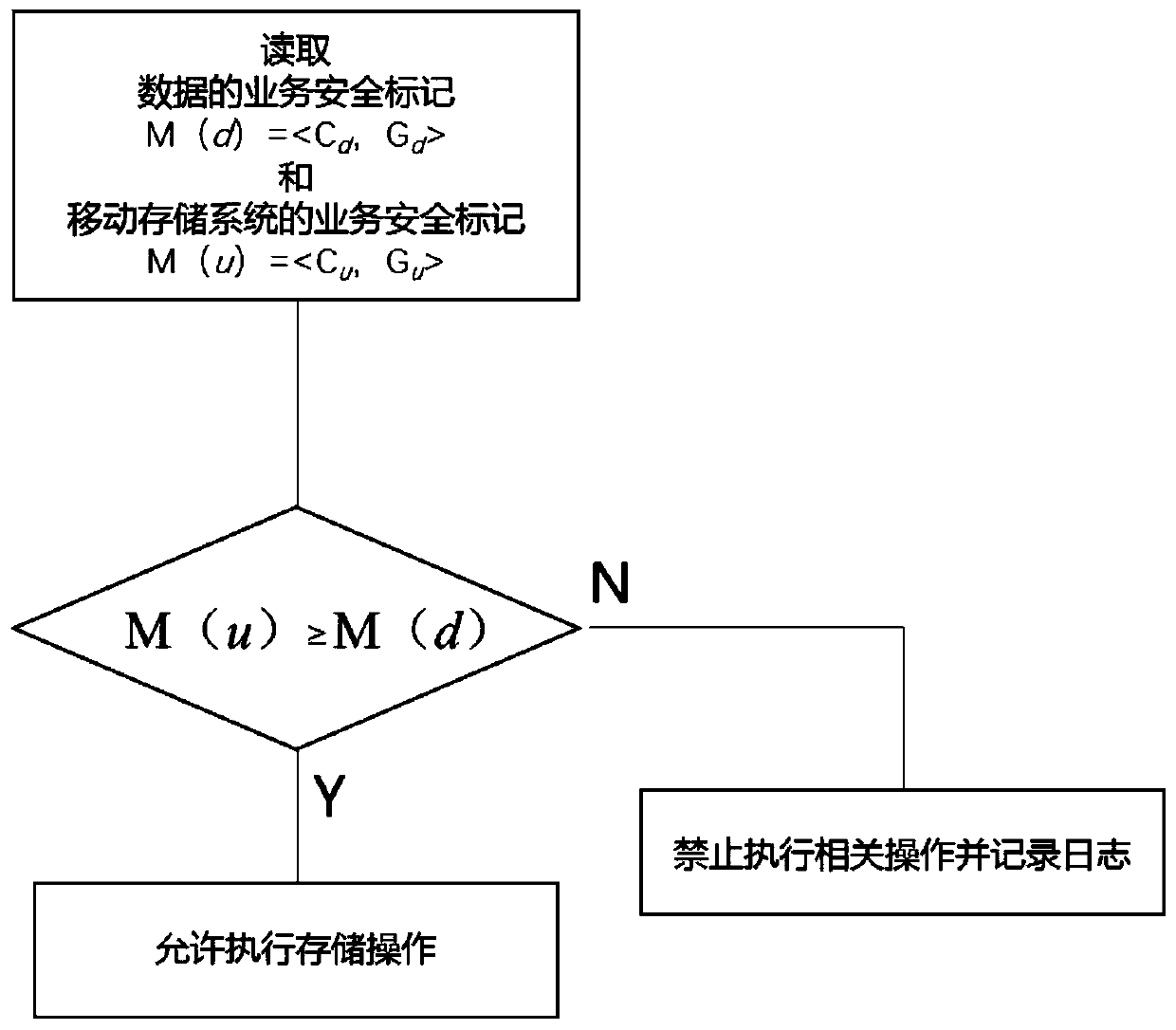
[0019] In order to achieve the above object, the present invention provides a mobile storage system access and data control method that supports service security marking, the method includes the following steps:
[0020] Business Security Tag Definitions:
[0021] The service security mark M is a tuple group including various service security attributes, M=. Where C is the security level; G is multiple business security attributes G i set of , G={g 1 , g 2 ,... g n}, g i It can be business security attributes such as business categories, work groups, roles, and environmental requirements; F is the operation control attribute f j set of , F={f 1 ,f 2 ,... f m}, f j It ca...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More