File decryption method, file encryption method, file management system and storage medium
A file encryption and file technology, applied in the field of encryption and decryption, can solve the problems of loss, low file confidentiality, and easy decryption or forgery of the decryption method, so as to improve confidentiality and meet the needs of privacy and security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example 1
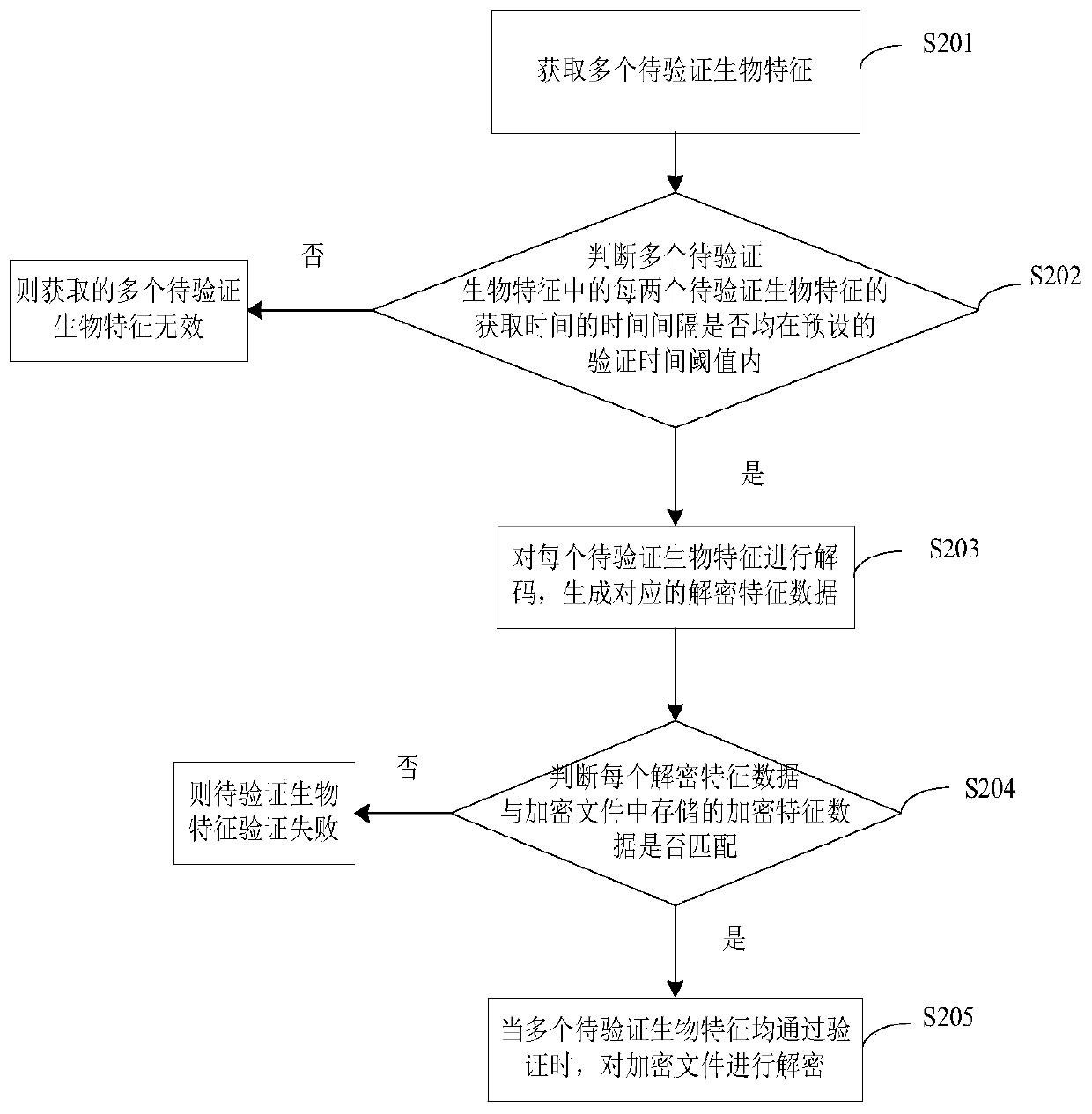
[0055] figure 2 A schematic flowchart of a file decryption method provided in Example 1 of the present application is shown. Such as figure 2 As shown, another file decryption method provided by this application includes steps S201 to S205.
[0056] In step S201, multiple biometric features to be verified are acquired.
[0057] In step S202, it is judged whether the time interval between the acquisition time of every two biometric features to be verified among the multiple biometric features to be verified is within the preset verification time threshold, and if so, the acquired multiple biometric features to be verified If it is valid, step S203 is executed; if not, the acquired biometric features to be verified are invalid.
[0058] Wherein, the preset verification time threshold can be set according to the degree of file security requirements and the performance of the corresponding biological feature collection device to be verified in the actual application process. ...
example 2
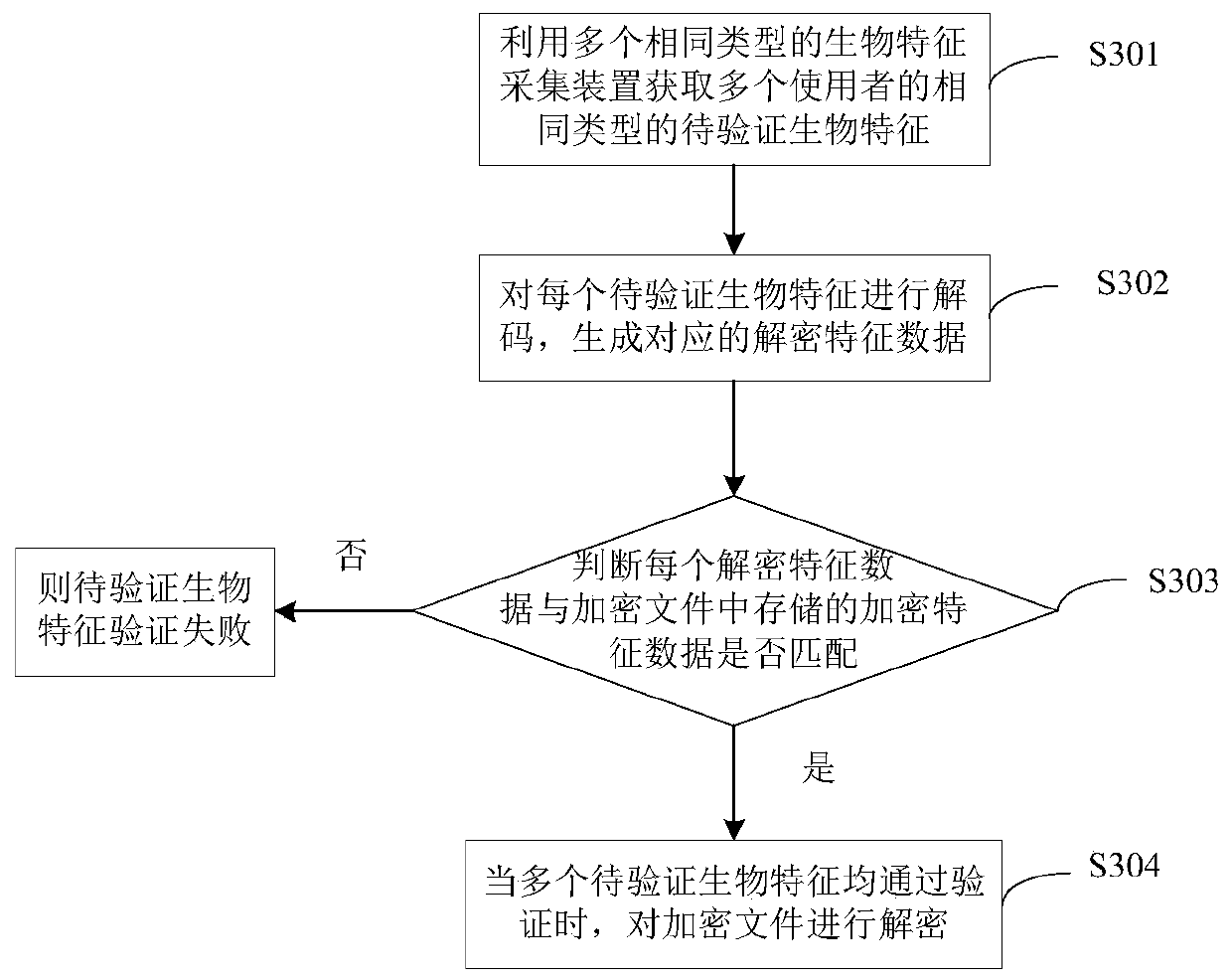
[0068] image 3 A schematic flowchart of a file decryption method provided in Example 2 of the present application is shown. Such as image 3 As shown, a file decryption method provided by the present application includes steps S301 to S304.
[0069] In step S301, a plurality of same type of biological feature acquisition devices are used to acquire the same type of biological features to be verified of multiple users.
[0070] This step may be, using multiple same type of biological feature collection devices communicatively connected to the same terminal to acquire the same type of biological features to be verified of multiple users. As a specific example, when the files on the mobile phone are encrypted using the features of two faces, correspondingly, the cameras on the left and right screens of the folding screen mobile phone can be used to simultaneously capture the files of two different users. facial features as the biometrics to be verified. When the folding scre...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com