Method for realizing installation tracking based on file filtering driver
A file filter-driven and file-driven technology, applied in computer security devices, software deployment, instruments, etc., can solve problems such as inability to host security protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
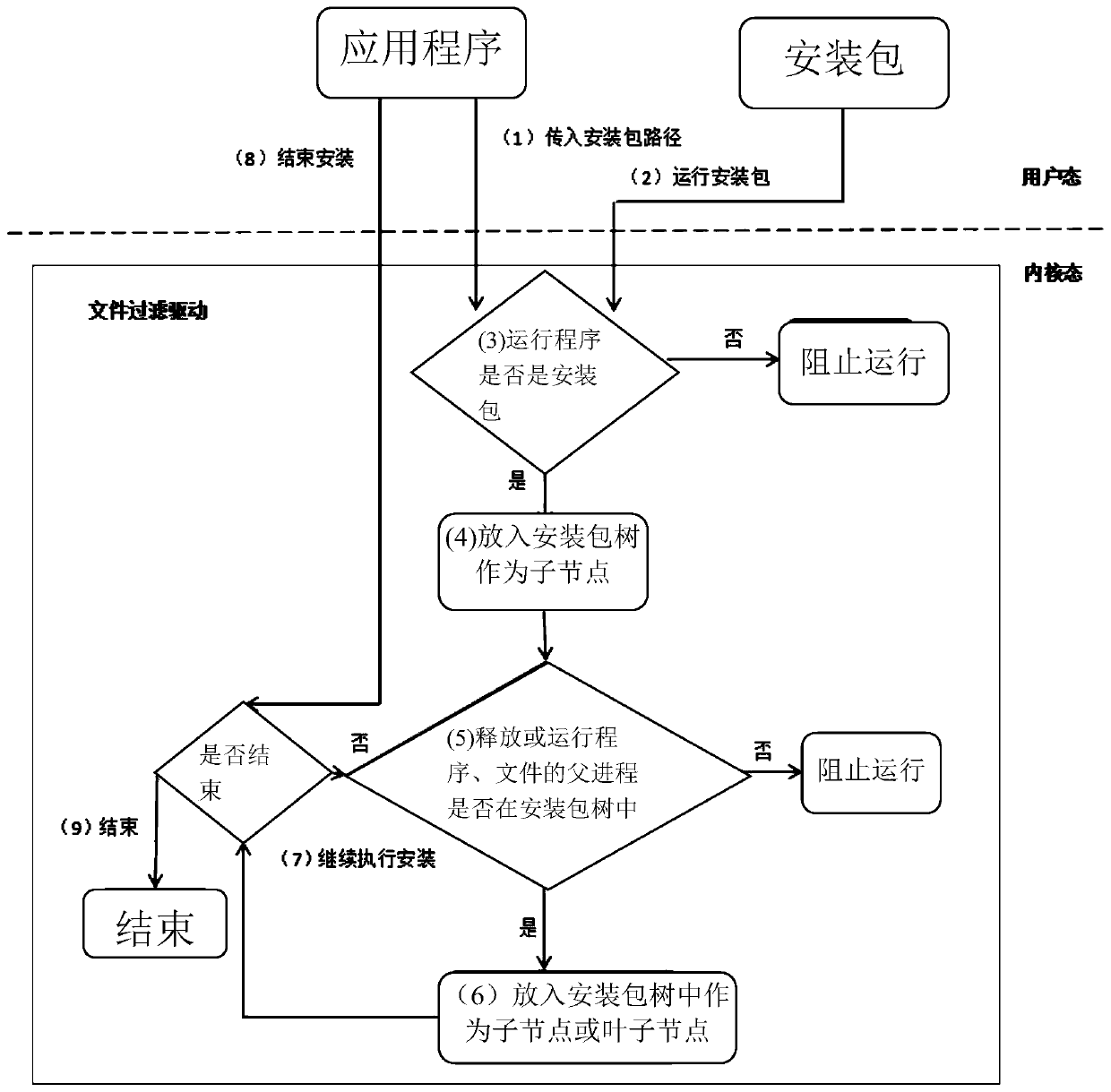
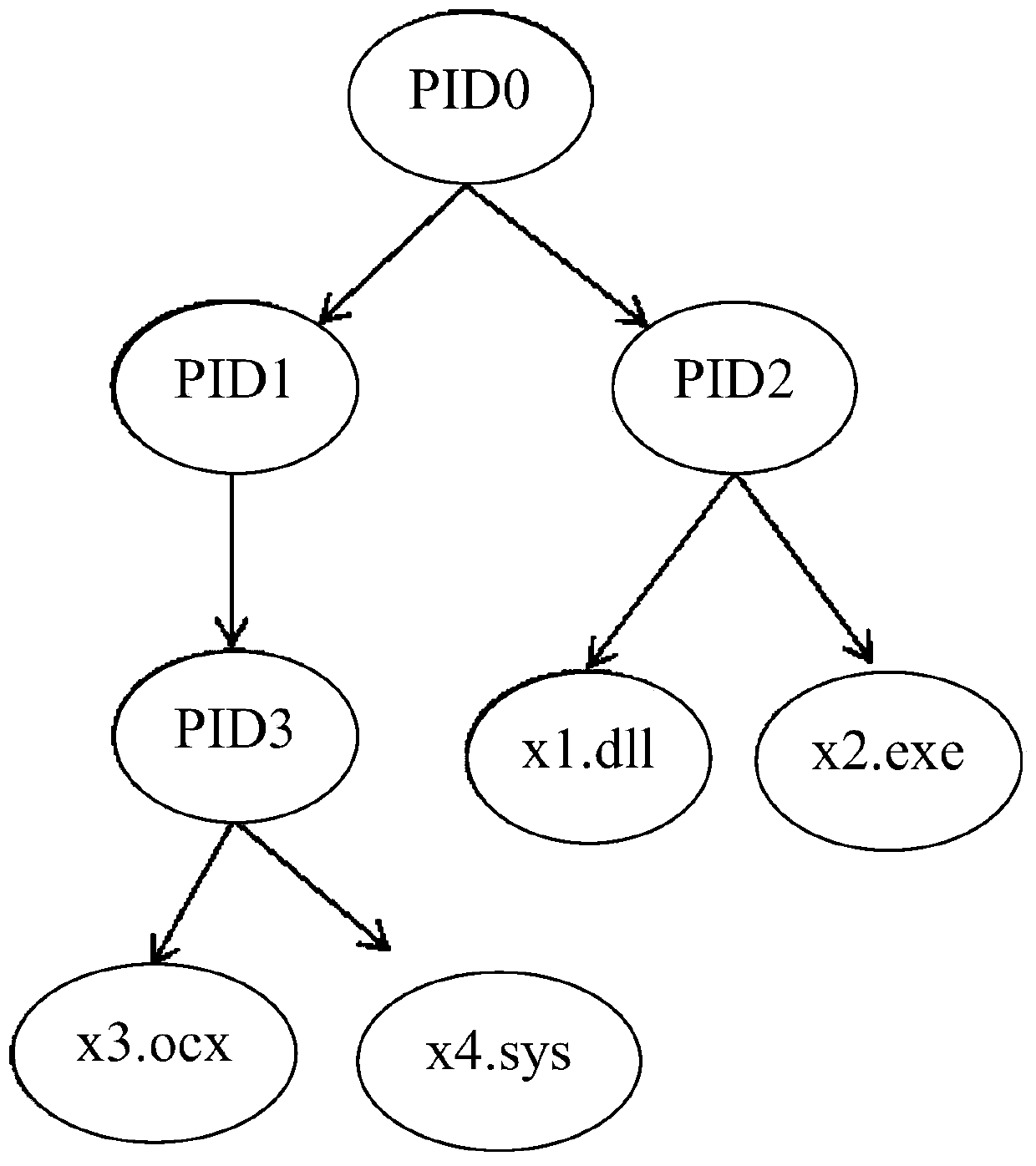
[0024] Embodiment: A method for realizing installation tracking based on a file filtering driver. The present invention provides security protection for the host when the installation package is installed. When the installation package needs to be installed, the operation of the whitelist is not stopped, and the installation package is authorized to release files or process and allow the released file or process to enter the running state, and update the white list to allow the installed program to run. The method comprises the following steps:
[0025] S1: The application passes the path of the installation package to the file filter driver, the application runs in user mode, and the file driver runs in kernel mode;
[0026] The operating system is divided into two levels of operation, user mode and kernel mode. User programs run in the user state, with a low level; the operating system, device drivers, etc. run in the kernel state, with a high level, running in two states m...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More