Layer cluster type wireless sensor network global key management method
A wireless sensor and global key technology, applied in the field of Internet of Things security and privacy protection, to achieve the effect of easy acquisition, good concealment, avoiding frequent encryption and decryption calculations and multi-level transmission
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
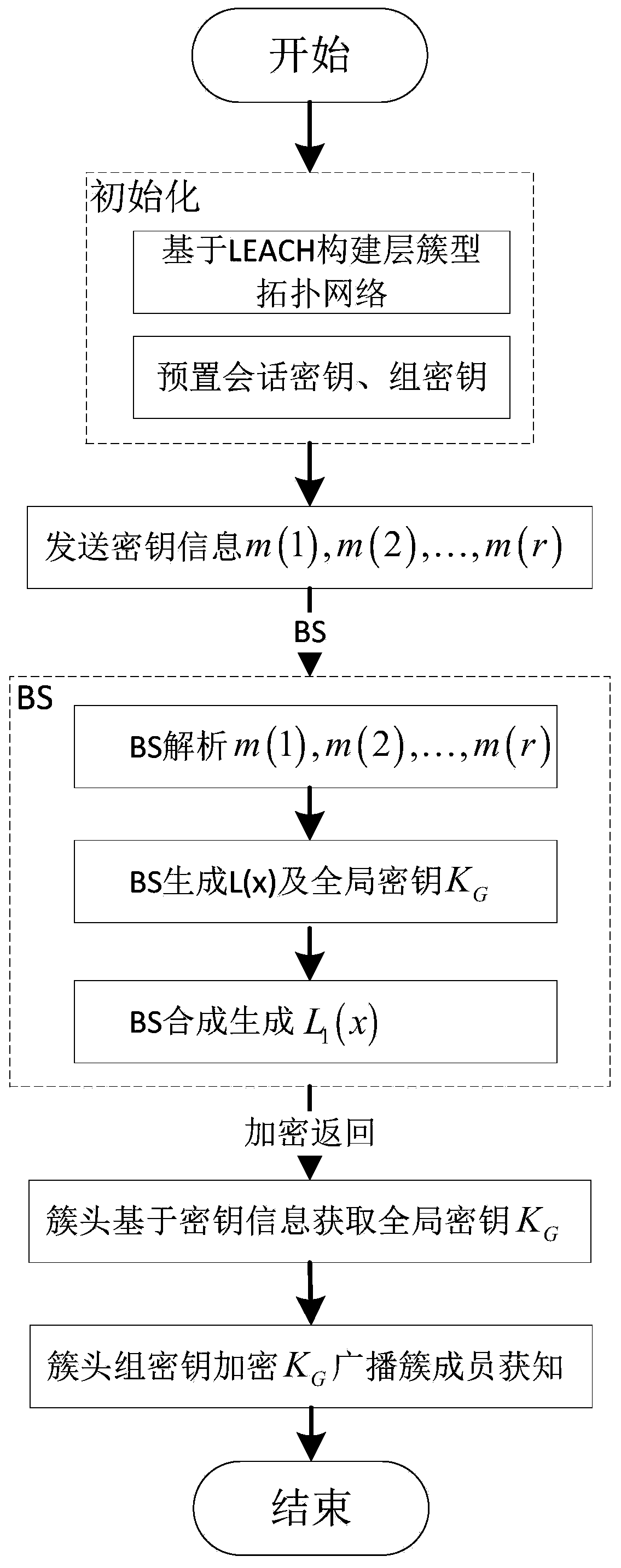
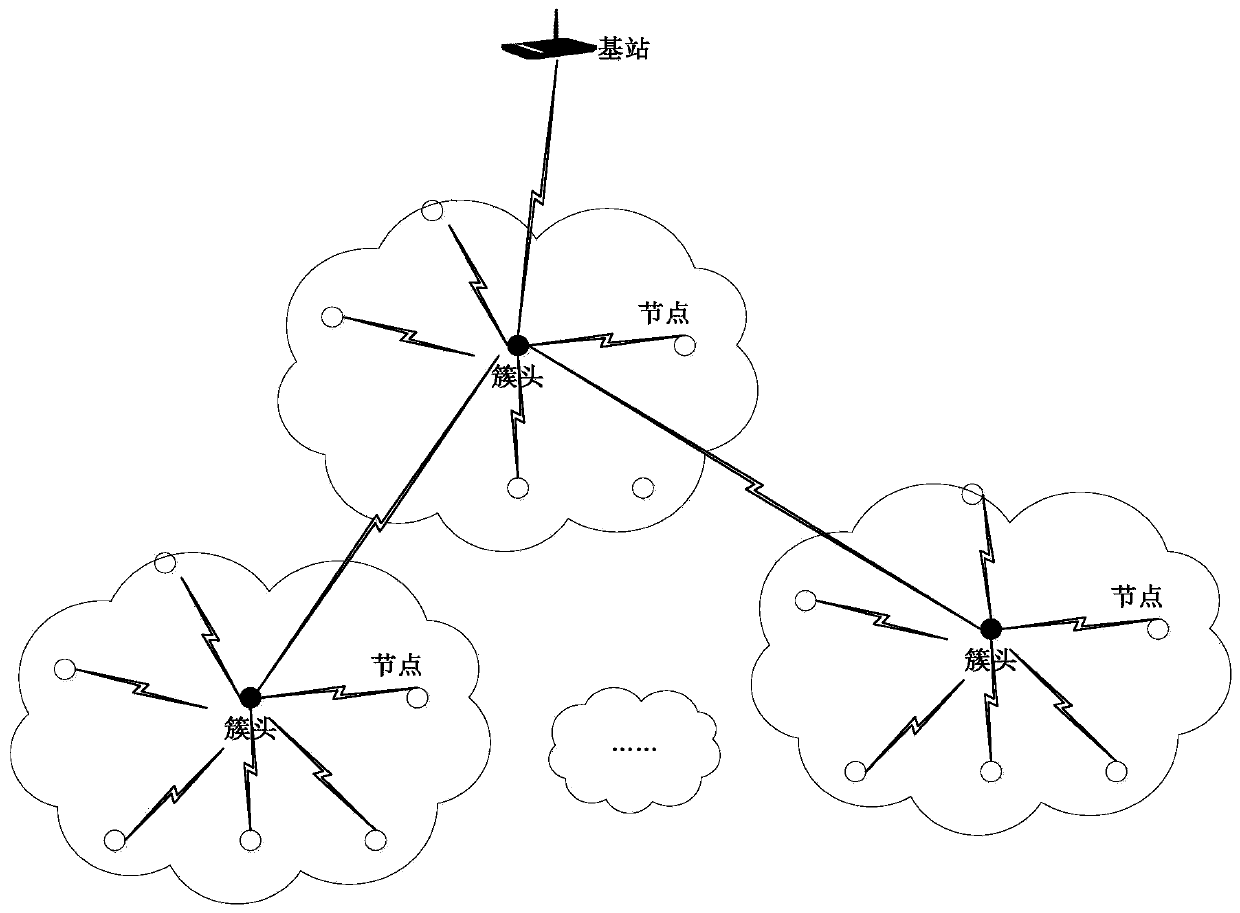
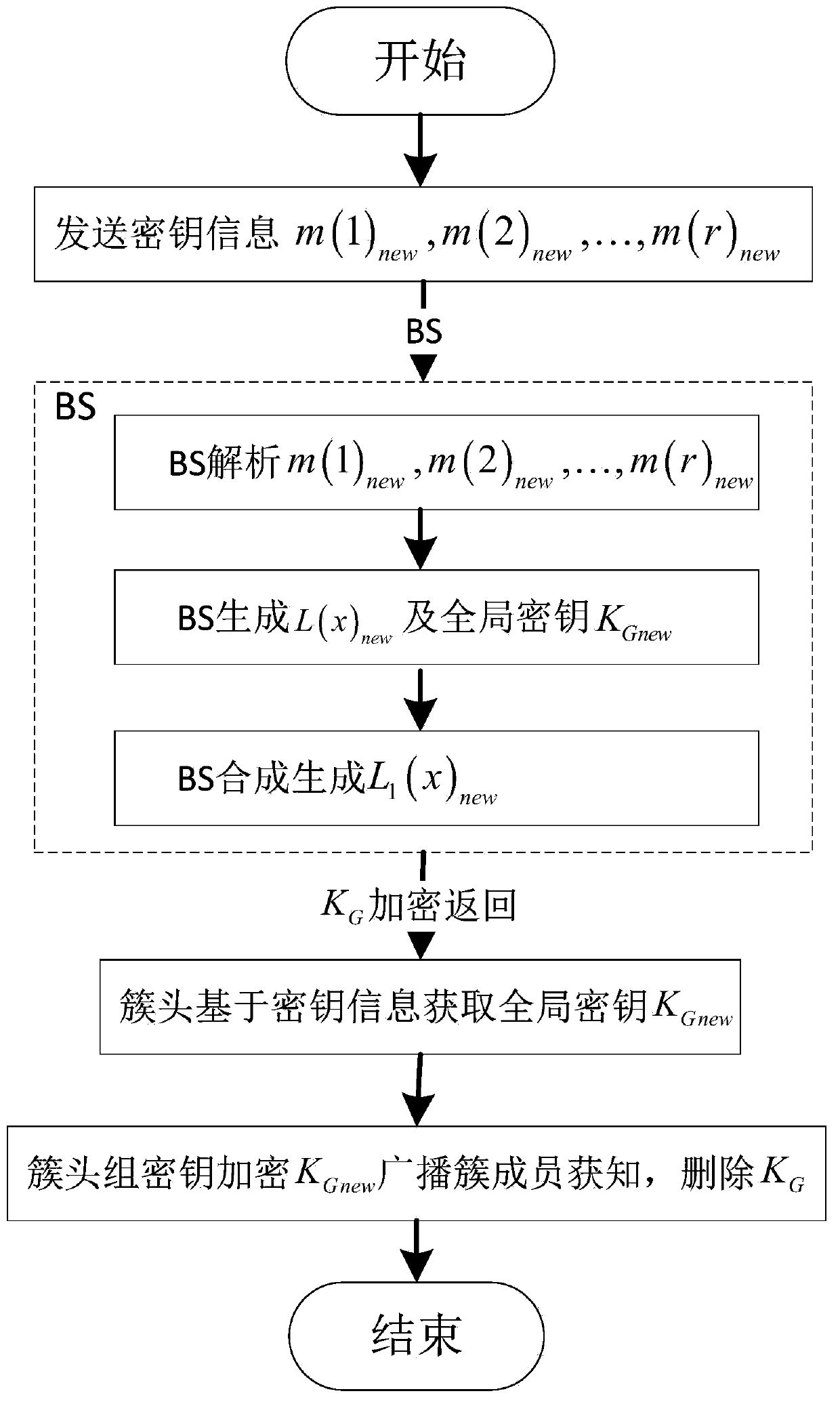
Method used
Image
Examples
Embodiment
[0048] There are two factors that affect the security of the global key: one is the base station, because the global key is completely randomly generated by the base station and has nothing to do with the nodes in the cluster. However, it is completely impossible to capture the base station, so the key source It is absolutely safe; the second is the key information m(i), all cluster heads obtain the global key K through the key information m(i) G . From the generation process of the global key, it is known that the key information m(i) is the key to obtain the key, but it has nothing to do with the key itself, and the transmission of the key information m(i) is completed by the session key , so to obtain the key information m(i), the session key must be parsed. This equivalent security relationship is specifically that the security of the key information m(i) is equivalent to the security of the global key, and the key information The security of m(i) is equivalent to the sec...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More