Power data encryption transmission method, system and readable medium for resumption of work and production detection
A technology for encrypted transmission and power data, applied in the field of encryption, it can solve problems such as hidden security risks, easy leakage of secret keys, and information leakage, and achieve the effect of improving security and data security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 2
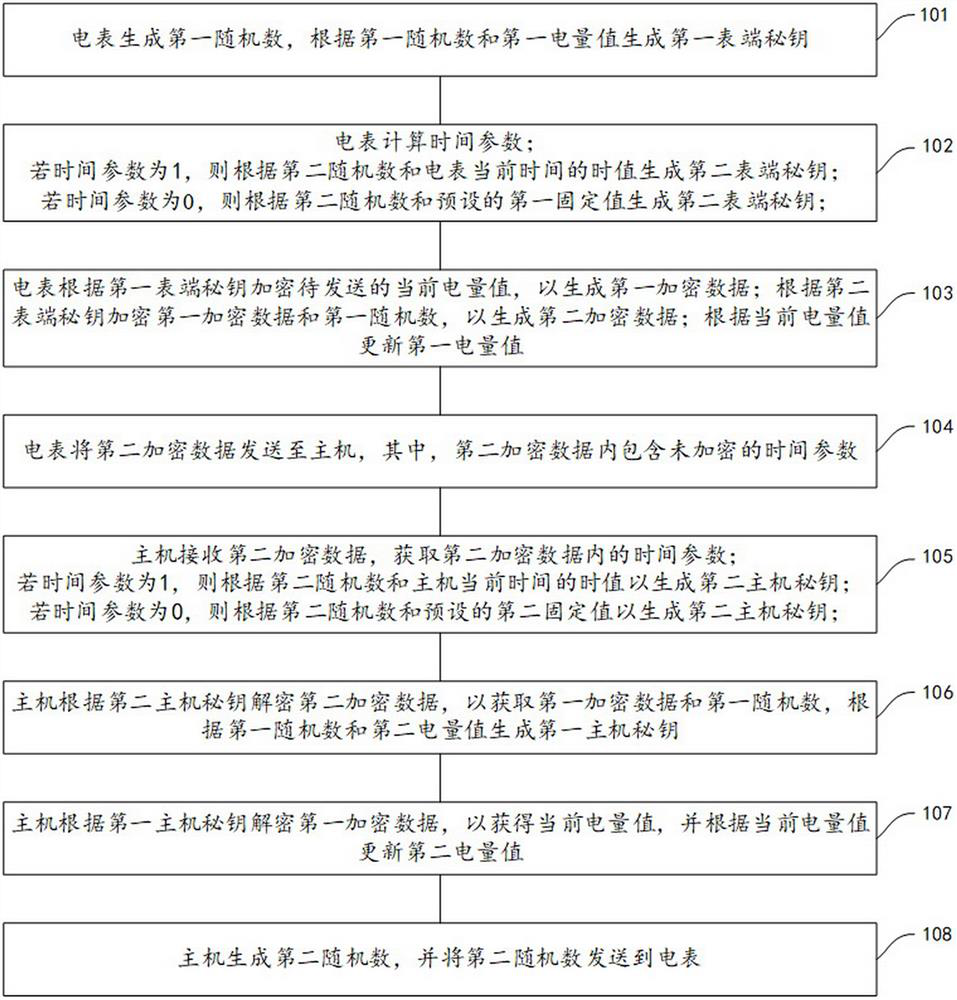
[0113] The power data encrypted transmission method for the inspection of resumption of work and production includes:
[0114] Presetting the initial value of the second power value and the second random number;
[0115] Receive the second encrypted data sent by the meter;
[0116] In response to the second encrypted data, execute as figure 2 A step of:
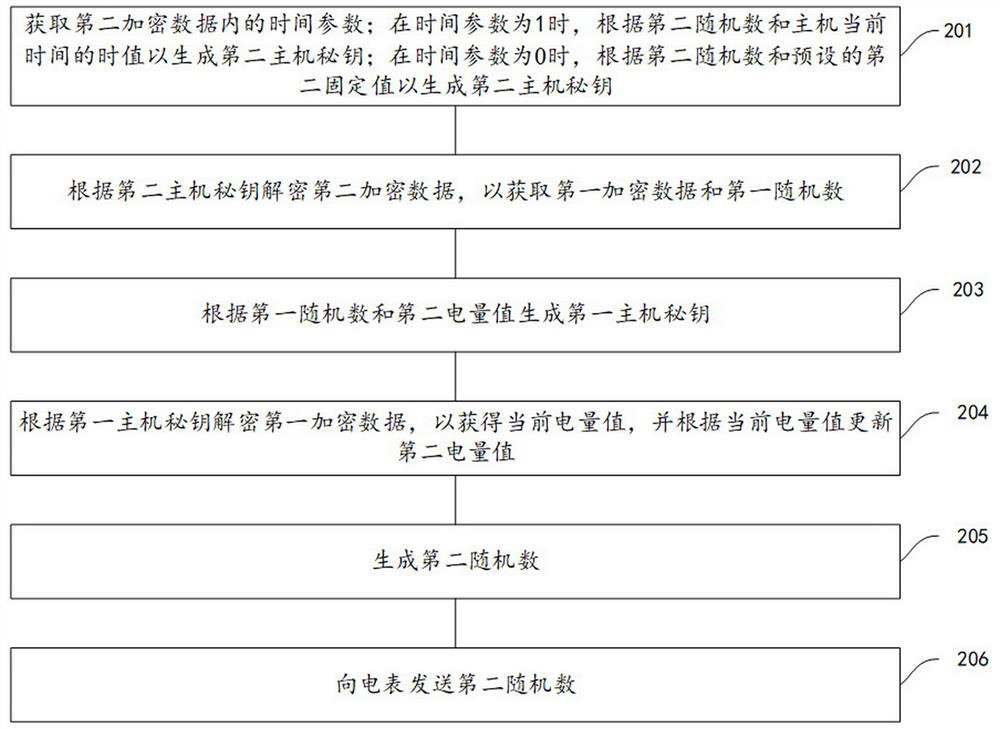
[0117] Step 201, obtain the time parameter in the second encrypted data; when the time parameter is 1, generate the second host key according to the second random number and the current time value of the host; when the time parameter is 0, according to the second A random number and a preset second fixed value to generate a second host key;
[0118] Step 202, decrypting the second encrypted data according to the second host key to obtain the first encrypted data and the first random number;
[0119] Step 203, generating a first host secret key according to the first random number and the second power value;
[0120] Ste...
Embodiment 3
[0134] A power data encrypted transmission method for detection of resumption of work and production, a computer-readable medium, including instructions, which, when run on a computer, cause the computer to execute any method described in Embodiment 2.
Embodiment 4
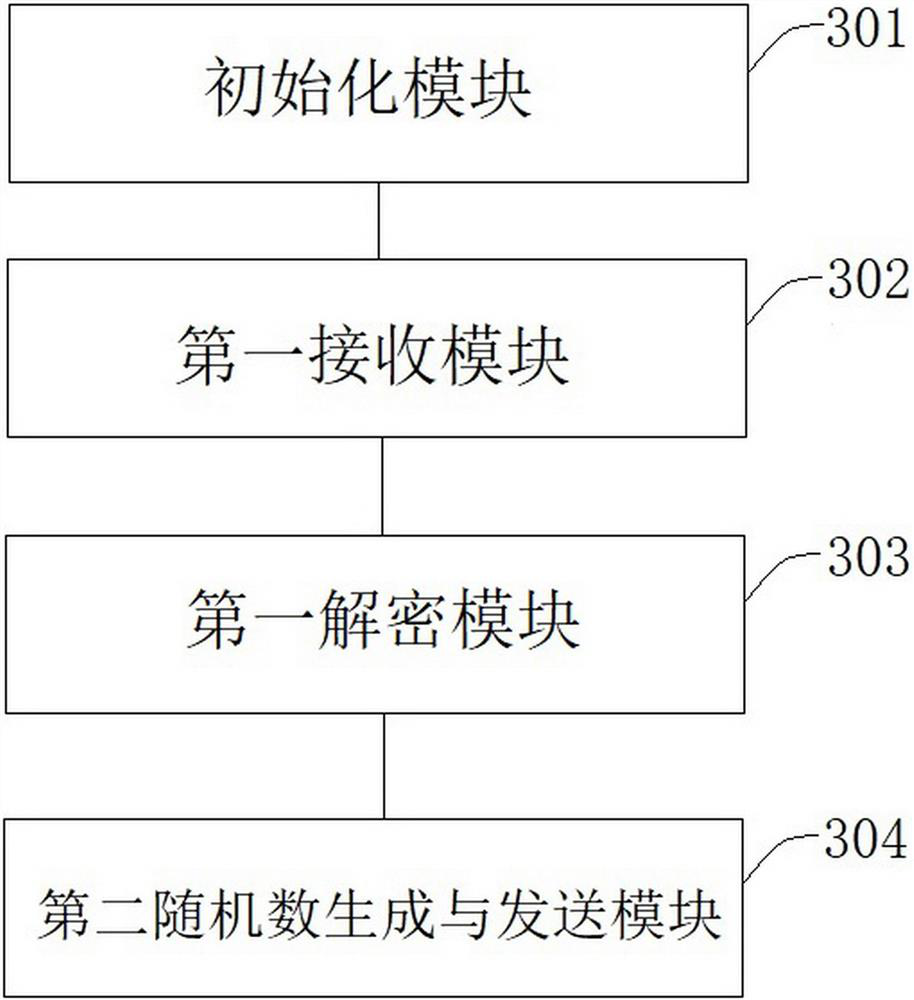
[0135] Embodiment 4, see image 3 , Power data encryption transmission system for resumption of work and production detection, including:
[0136] The initialization module 301 is used to set the initial value of the second power value of the host, so that the second power value of the host is the same as the first power value of the meter, and set the initial value of the second random number of the host, so that the second power value of the host The second random number is the same as the second random number of the meter;
[0137] A first receiving module 302, configured to receive second encrypted data;
[0138] The first decryption module 303 is configured to obtain the time parameter in the second encrypted data, if the time parameter is 1, then generate the second host secret key according to the second random number and the time value of the current time of the host; if the time parameter is 0 , the second host key is generated according to the second random number an...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap