Policy configuration device, security policy configuration method of terminal and readable storage medium
A technology of security policy and configuration method, applied in the security field, can solve the problem of long time for security policy configuration
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
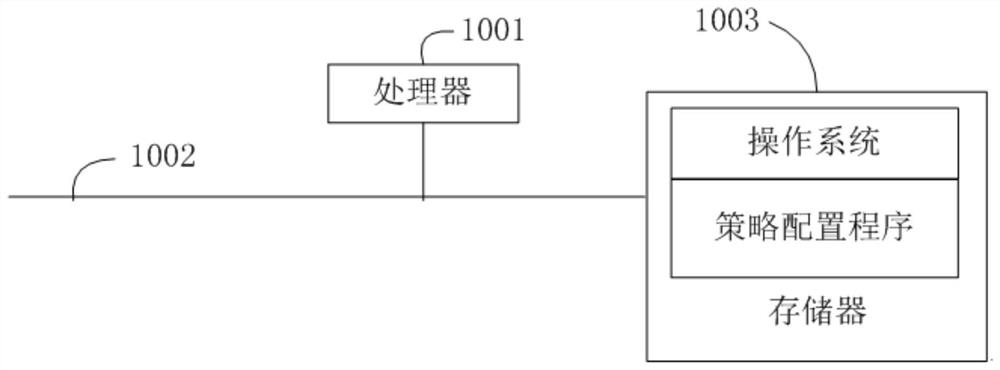
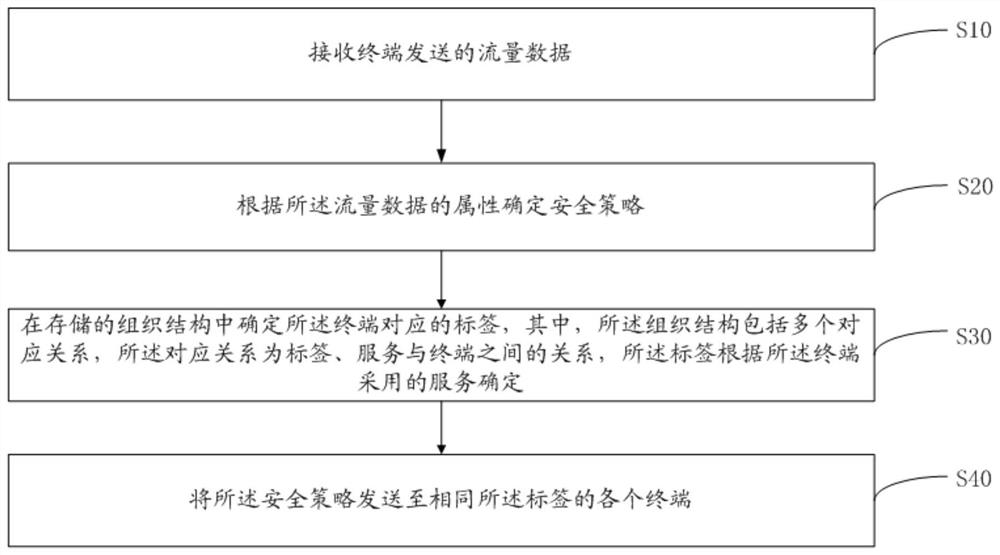
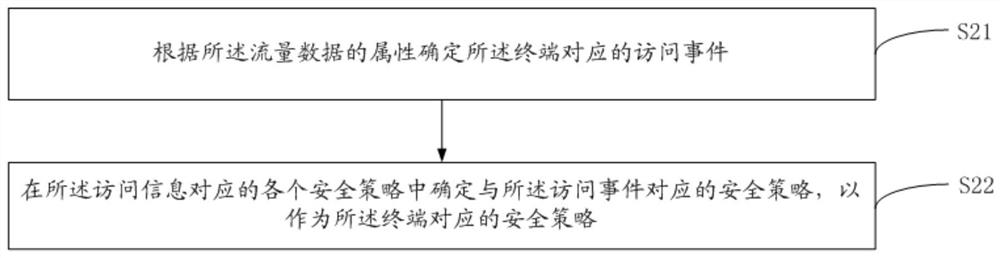
[0038] The main solution of the embodiment of the present invention is: receiving the traffic data sent by the terminal; determining the security policy according to the attribute of the traffic data; determining the label corresponding to the terminal in the stored organizational structure, wherein the organizational structure includes multiple A corresponding relationship, the corresponding relationship is the relationship between a label, a service and a terminal, the label is determined according to the service adopted by the terminal; the security policy is sent to each terminal with the same label.
[0039] Since the organizational structure is stored in the policy configuration device, the device can determine each terminal using the same service based on the organizational structure, and then the device can aut...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More