A detection method for intrusion data
A detection method and data technology, applied in digital transmission systems, instruments, computing, etc., can solve the problems of high recognition rate of most types of sample points, reduce information prevention of minority types, reduce service performance, etc., and reduce the average false negative rate. , the effect of reducing the imbalance between classes and making up for the lack of quantity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] Specific embodiments are given below to further illustrate the present invention.
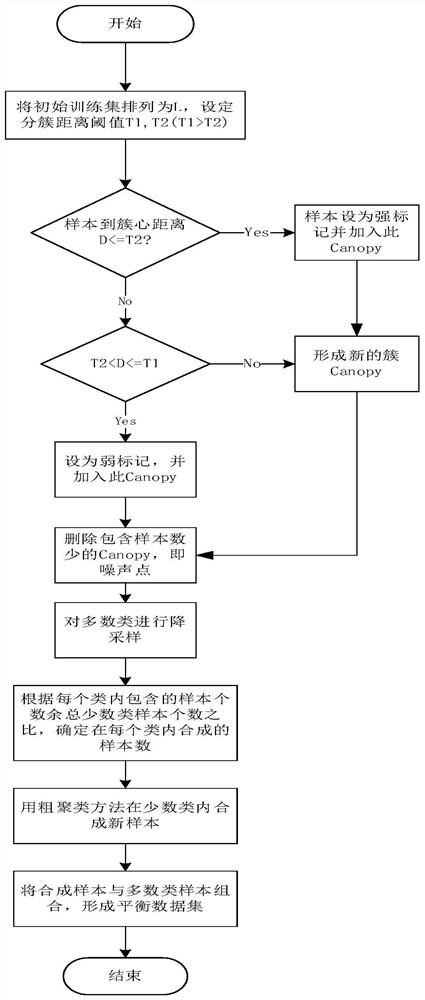
[0038] like Figure 1 to Figure 4 As shown, a detection method for intrusion data specifically includes the following steps:
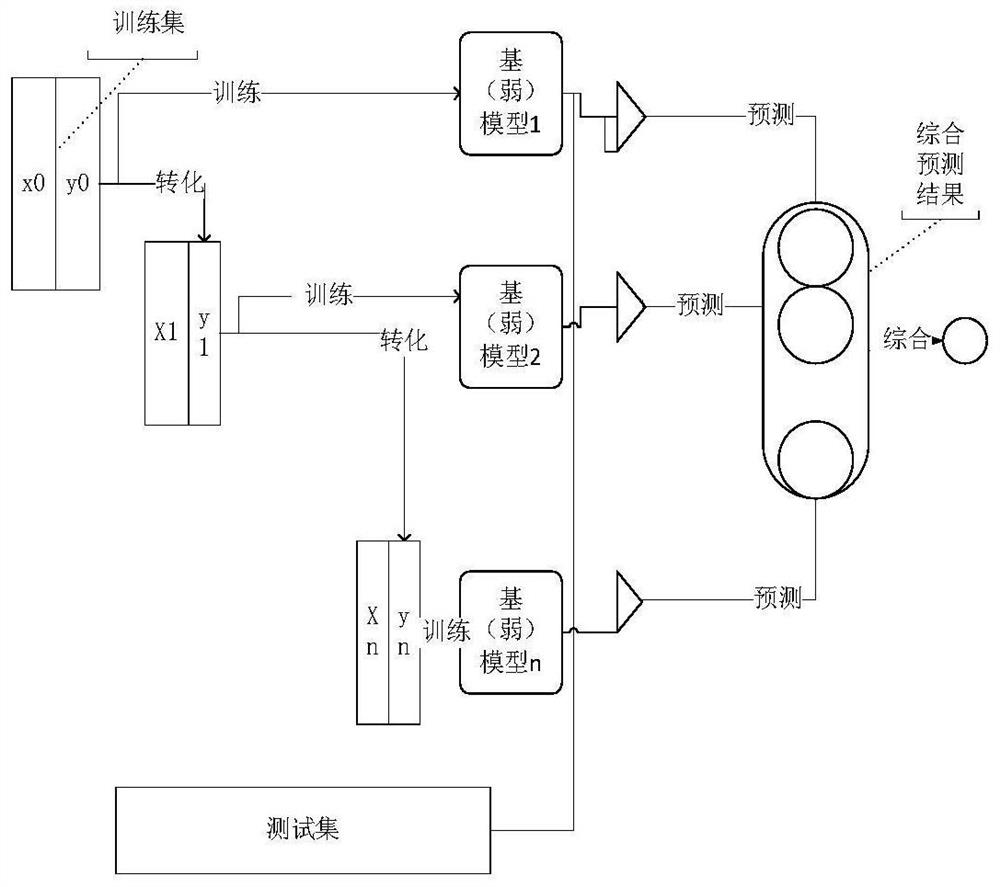
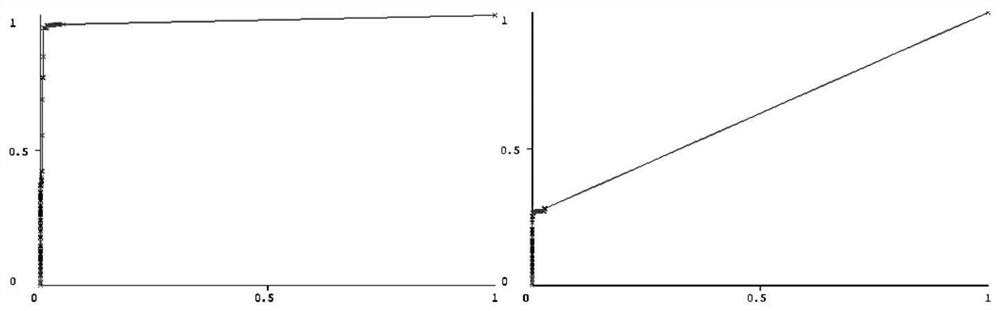
[0039] 1) The steps of obtaining a balanced data set: Use the coarse clustering method to calculate the distance from the sample point to the cluster center point from the training data according to the Euclidean distance, and divide it into multiple cluster subsets, which will contain fewer sample points and longer distances. The clustered subsets of the intrusion data are regarded as noise points, and these noise data are deleted; then different categories of intrusion data are randomly sampled and dimensionality reduction is carried out to reduce the overfitting of different categories of intrusion data models, and the training set is adjusted by the oversampling method. Perform intra-class equalization, increase the number of samples in some categories, and ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More