Key management method and device thereof, electronic equipment and readable storage medium
A key management and key seed technology, applied in the information field, can solve problems such as key security damage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
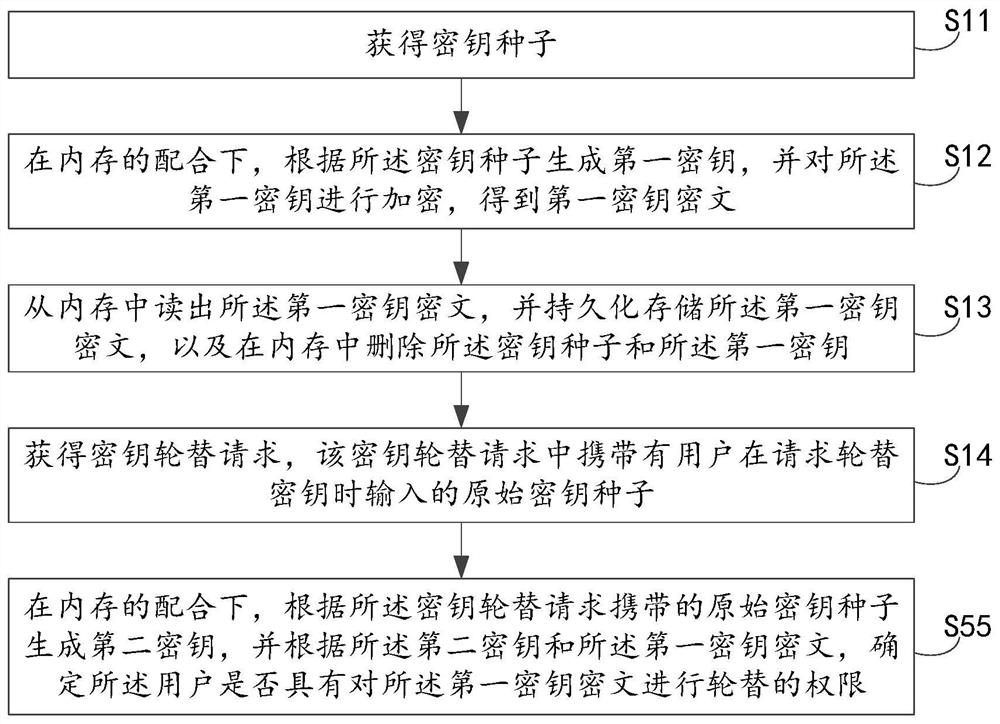
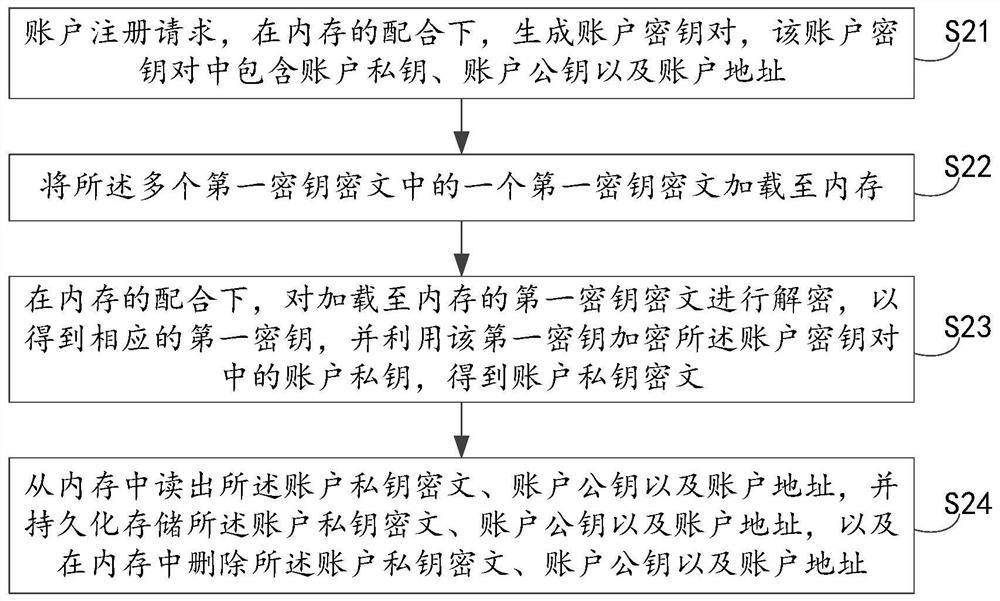
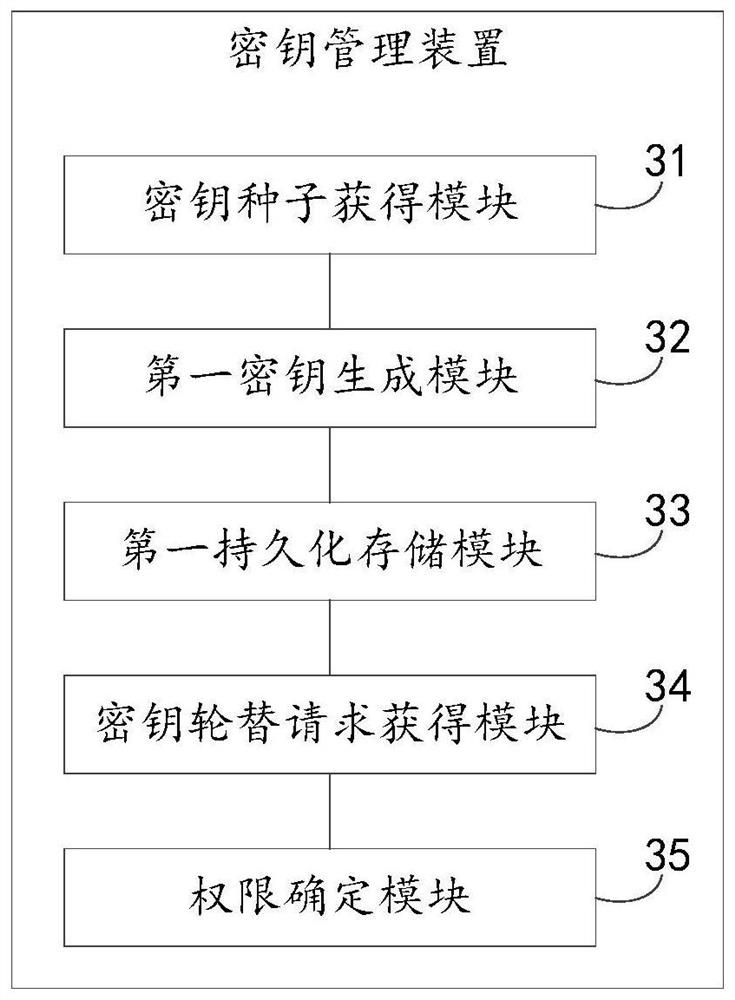
[0028] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the drawings in the embodiments of the present invention. Apparently, the described embodiments are some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0029] In related technologies, when registering a new account, the user usually needs to input a key seed into the system. The system generates a key based on the key seed entered by the user and stores the key persistently. This key can be used to encrypt other keys, and can also sign or encrypt and decrypt business data during business operations.
[0030] In addition, after the system generates the key, it also saves the key seed used to generate the key. The saved key se...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More