A system and method for vulnerability detection of power Internet of Things protocol based on fuzzing
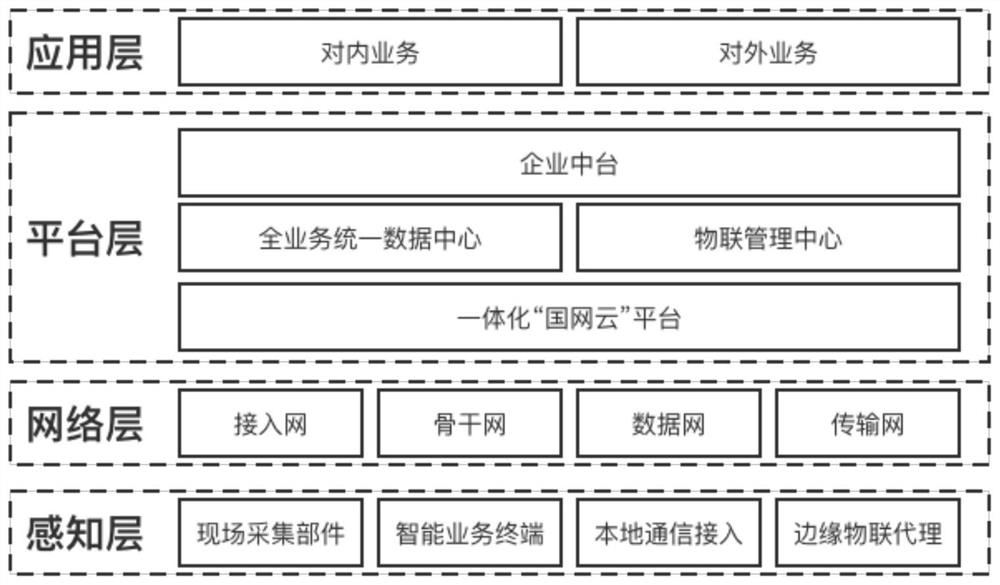
A technology for power Internet of Things and vulnerability detection, applied in the field of Internet of Things, can solve problems such as inability to detect protocol vulnerabilities, and achieve the effects of flexible sample generation, commission efficiency, and improved ability.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041] In order to make the purposes, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly and completely described below with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments These are some embodiments of the present invention, but not all embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative work fall within the protection scope of the present invention.
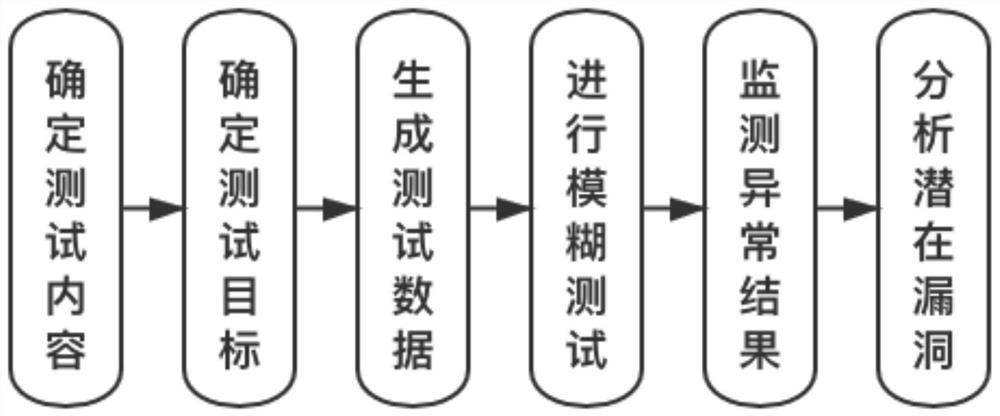
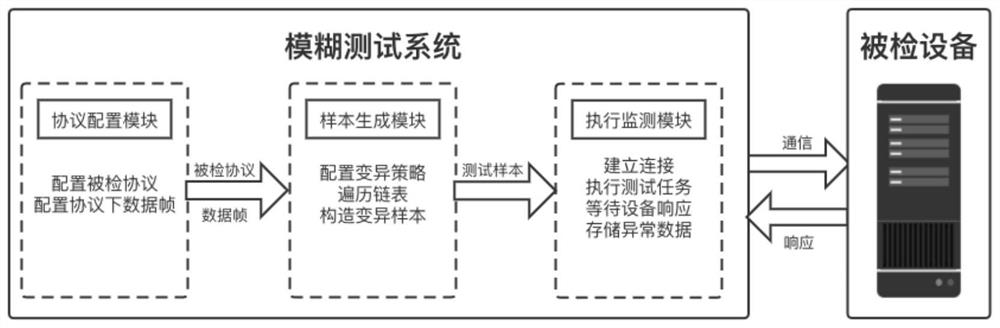
[0042] Fuzzy testing is widely used in software testing as a vulnerability mining method, and the present invention uses the fuzzing testing method to perform security detection on the protocol. Fuzz testing mainly generates the required test samples through certain rules, and automatically sends the test samples to the test target to cause ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More