Suspicious process processing method and device, storage medium and electronic equipment
A process processing and process technology, applied in the field of data security, can solve problems such as leakage of sensitive files, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
[0035] It should be clear that the described embodiments are only some of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
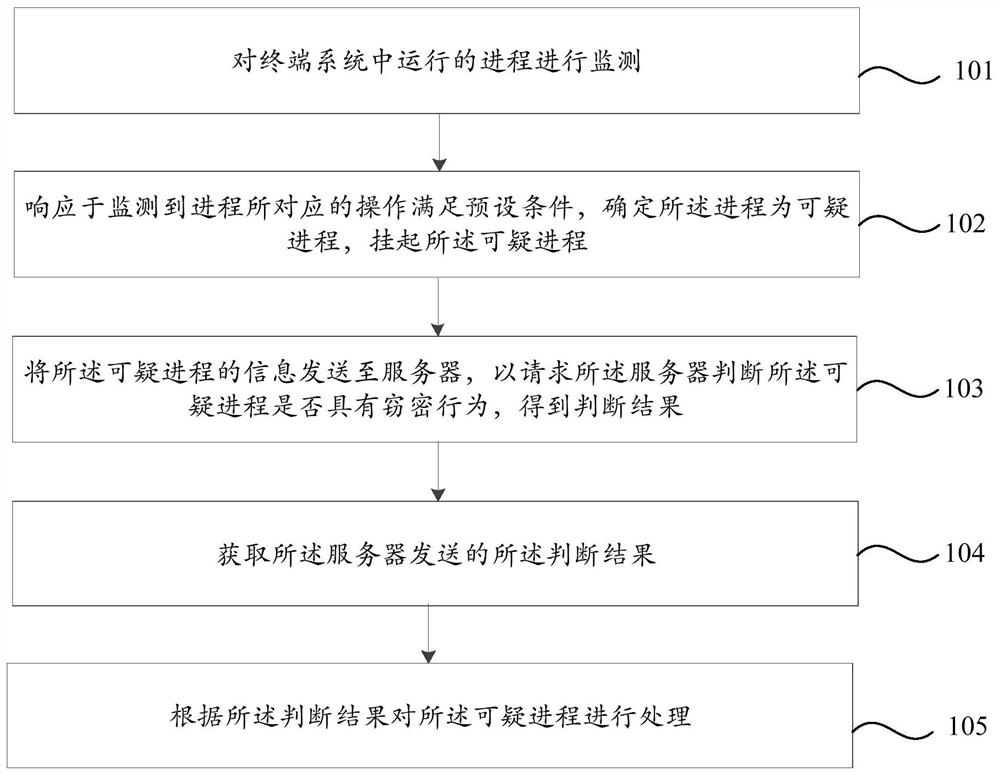
[0036] figure 1 is a flowchart of a suspicious process processing method shown according to one or more embodiments of the present invention, the method can be applied to a terminal, for example, can be executed by a terminal, such as figure 1 As shown, the method includes:
[0037] Step 101: Monitor the processes running in the terminal system;
[0038] For example, it is possible to periodically detect whether the processes running in the terminal system meet the preset conditions at preset time intervals.
[00...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More