Systems and methods for providing a covert password manager
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0014]In the following description, reference is made to the accompanying drawings that form a part hereof, and in which is shown by way of illustration specific embodiments in which the invention may be practiced. It is to be understood that other embodiments may be utilized and structural changes may be made without departing from the scope of the present invention.
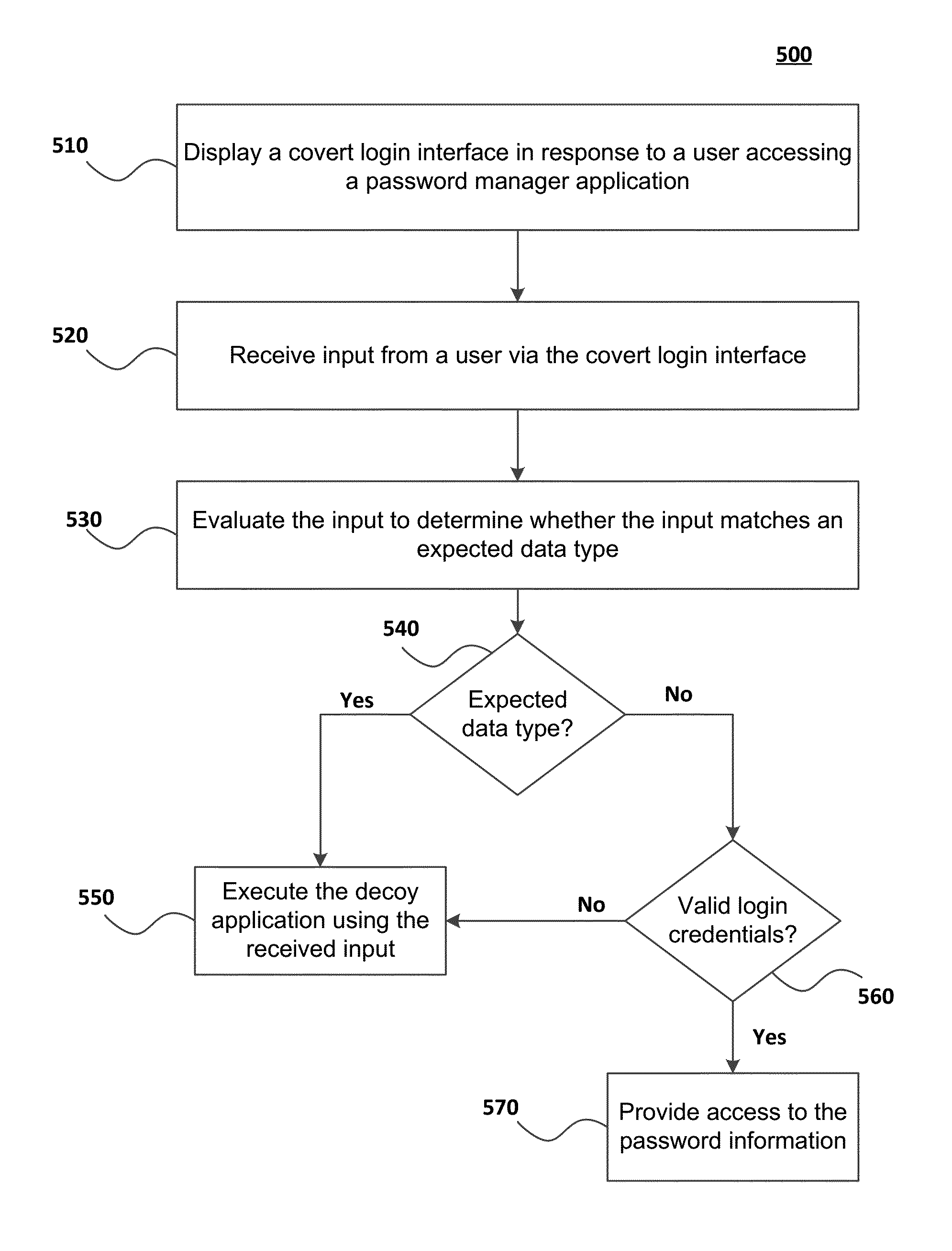
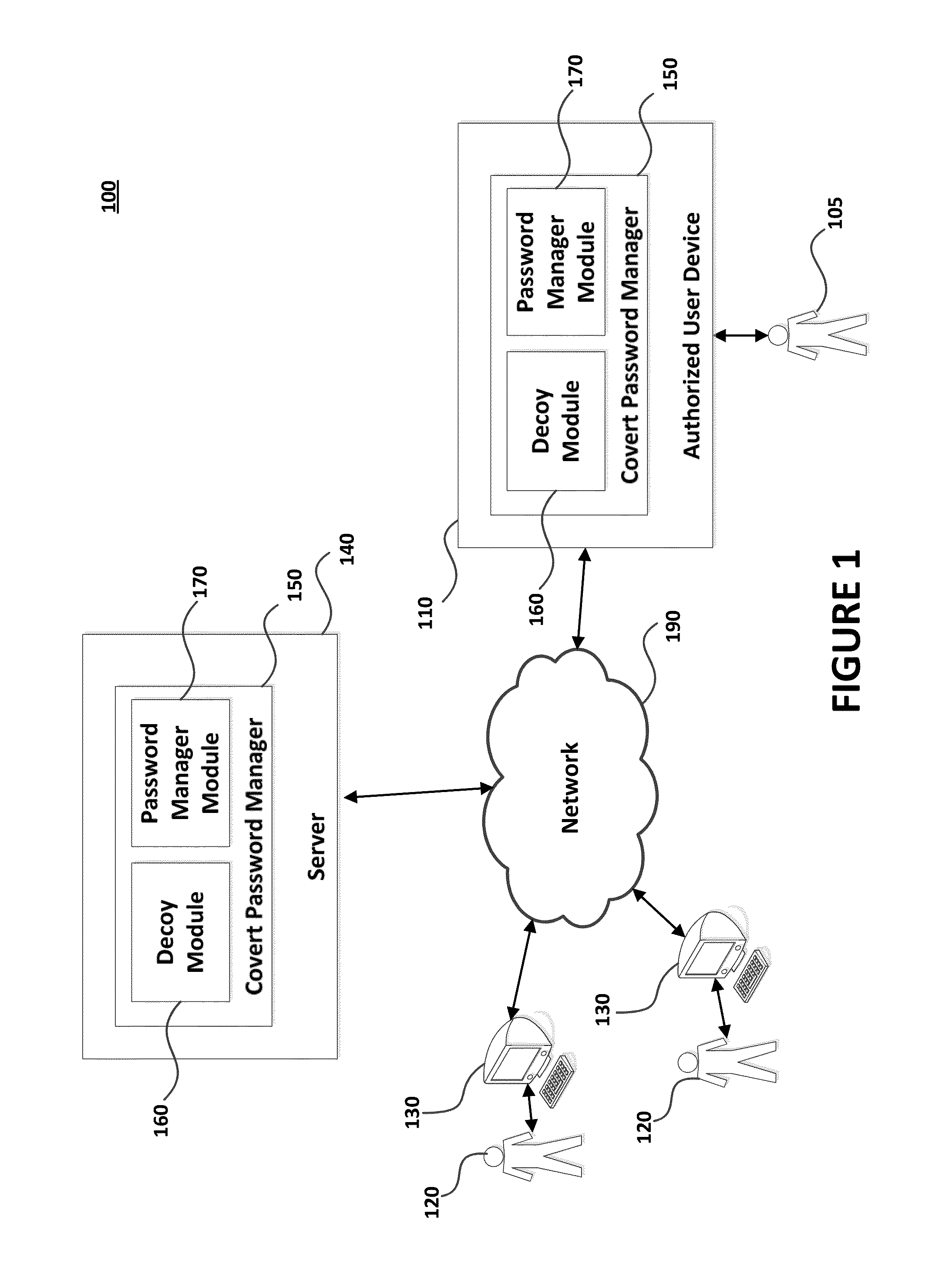
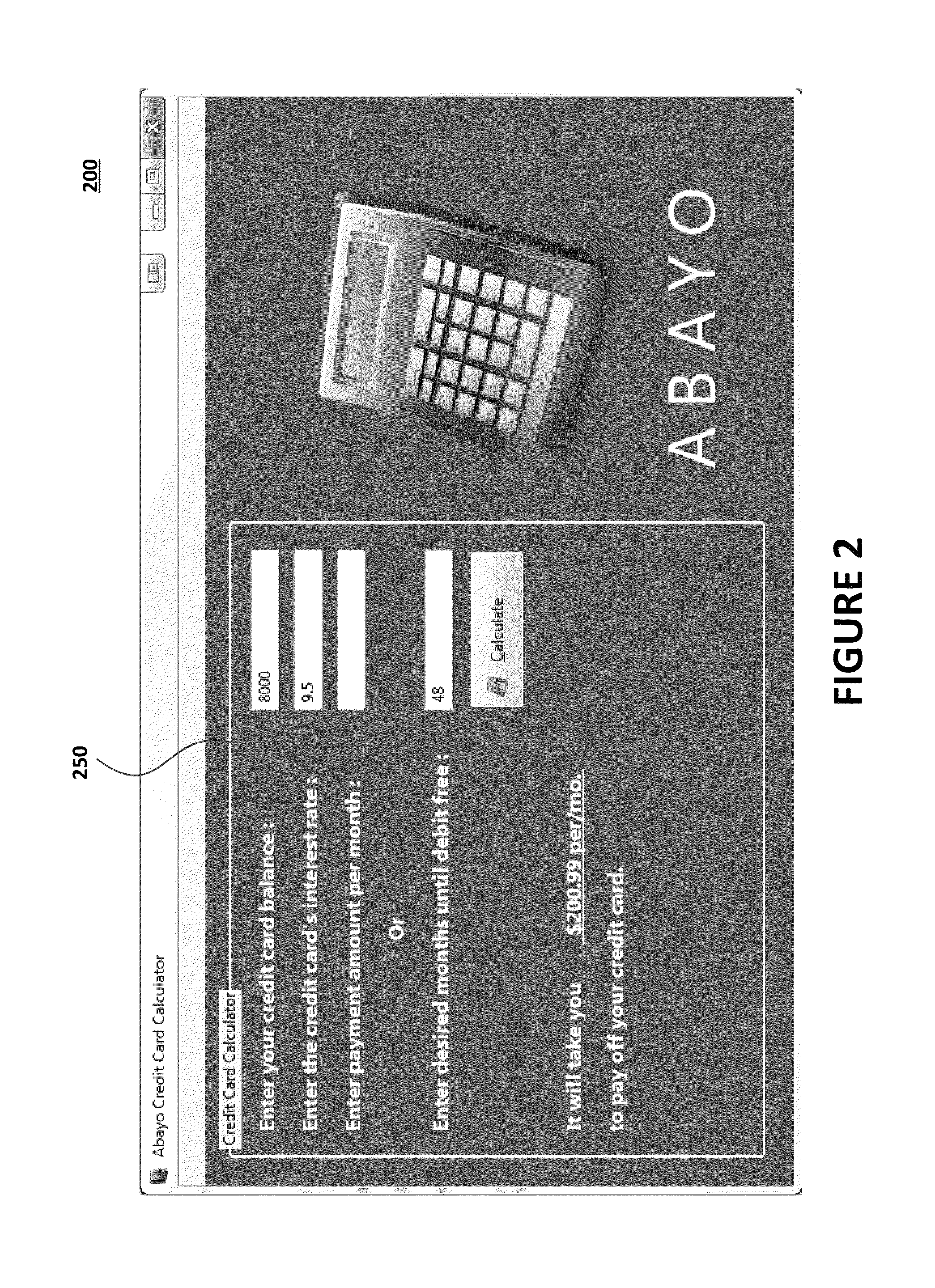
[0015]In accordance with certain embodiments, an application is configured to provide secure access to confidential information. The confidential information may include password information, medical information, financial information, personal contacts information or other type of confidential information. To protect the confidential information, the application may initially present a user with a “decoy application” that is configured to display interfaces and perform functions that are unrelated to managing confidential information. The decoy application may be a separate application that is launched by application t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More