Key agreement method in WAPI authentication mechanism
A key agreement and key technology, applied in the direction of synchronous sending/receiving encryption equipment, data exchange through path configuration, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
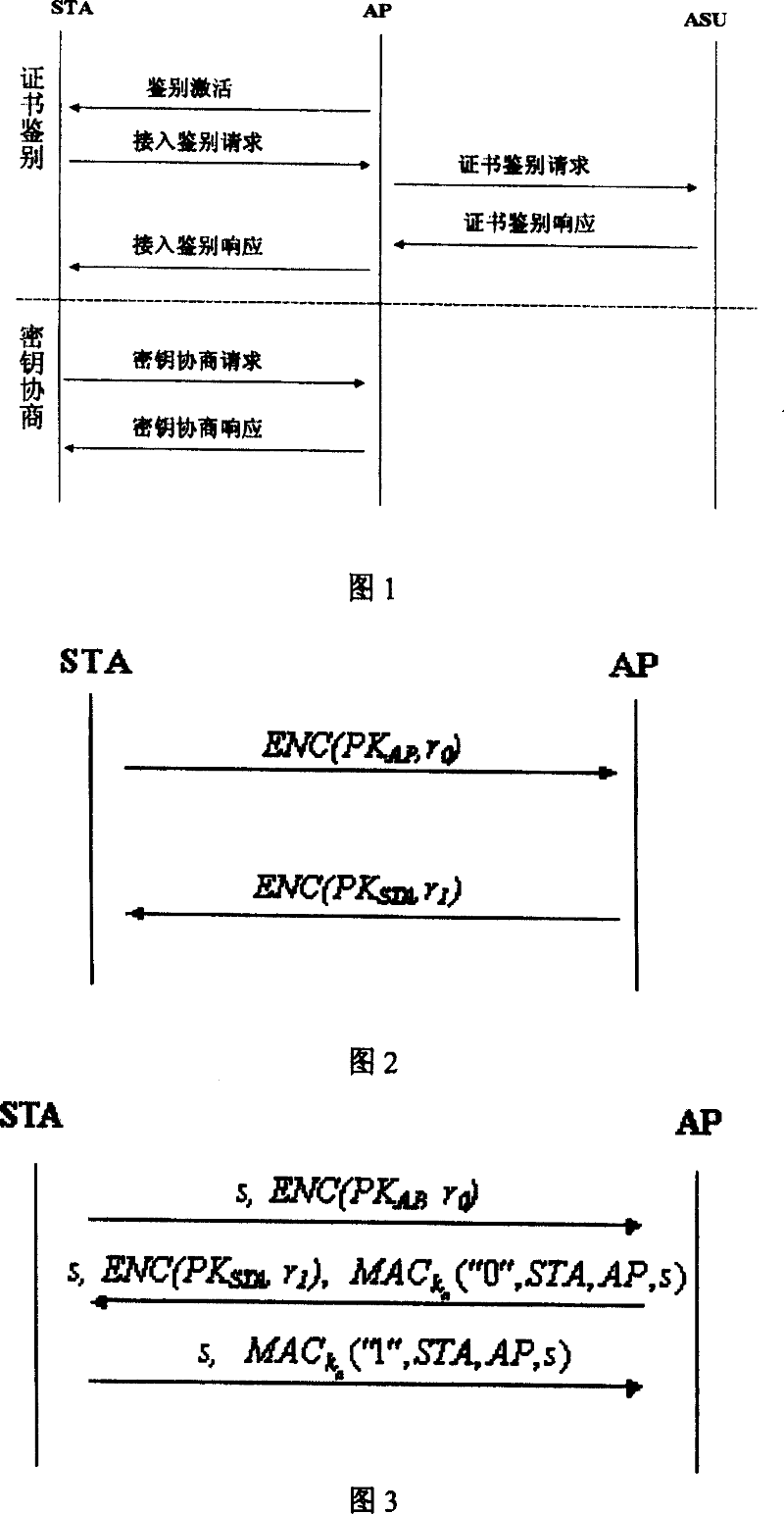
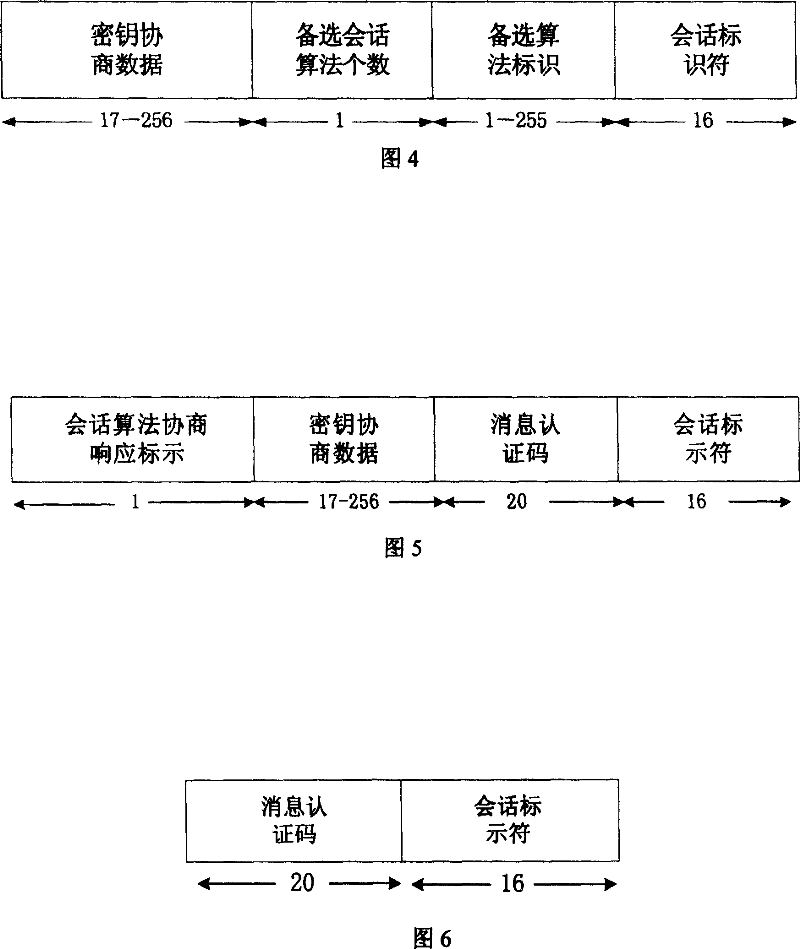
[0064] When implementing the WAPI authentication and security infrastructure of the wireless LAN, firstly, the client STA and the access point AP obtain their respective public-private key pairs through the key generation algorithm, and then apply for their respective public key certificates from the authentication service unit ASU. The certificate can adopt the format stipulated in the national standard GB15629.11 for wireless local area network. Then, start the protocol interaction of the wireless local area network authentication infrastructure WAI, which includes two parts: certificate authentication and key negotiation. Among them, the certificate authentication process adopts the steps stipulated in the national standard GB15629.11, and the specific interactive process of the key negotiation is carried out according to the three messages shown in Figure 3 .
[0065] 1. The first message is that the client STA sends a key negotiation request to the access point AP. The r...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com