Platform identification realizing method suitable for trusted network connection framework of trusted computing group (TCG)
A network connection and implementation method technology, applied in the field of network security, can solve the problems of low efficiency of platform authentication implementation methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
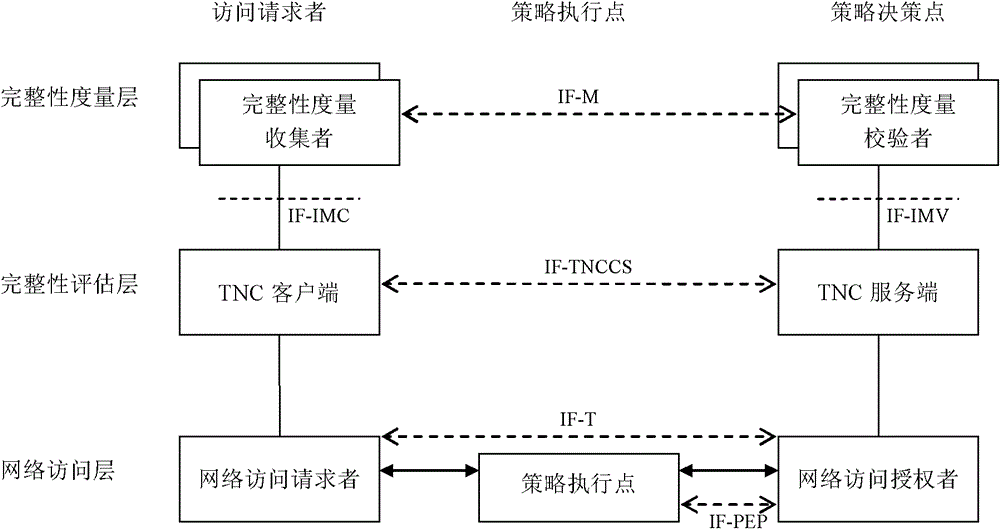
[0048] A detailed description of a platform identification implementation method suitable for the TCG trusted network connection architecture:
[0049] Step 1) When the TNC client initiates platform authentication, the TNC client generates an IF-TNCCS batch and sends the IF-TNCCS batch to the TNC server. The IF-TNCCS batch contains zero or at least one IF-TNCCS message carrying IF-M messages generated by the TNC client, wherein each IF-TNCCS message carrying IF-M messages only carries one An IF-M message sent by an integrity metric collector;
[0050] Step 2) When the TNC server initiates platform authentication, the TNC server generates an IF-TNCCS batch and sends the IF-TNCCS batch to the TNC client. The IF-TNCCS batch contains zero or at least one IF-TNCCS message carrying IF-M messages generated by the TNC server, wherein each IF-TNCCS message carrying IF-M messages only carries one IF-TNCCS message carried by the TNC server. An IF-M message sent by an integrity metric v...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More