Data protection method and device
A data protection and data technology, applied in the field of operating systems, can solve problems such as low data security, inability to save application data, loss of important data, etc., and achieve the effect of improving data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
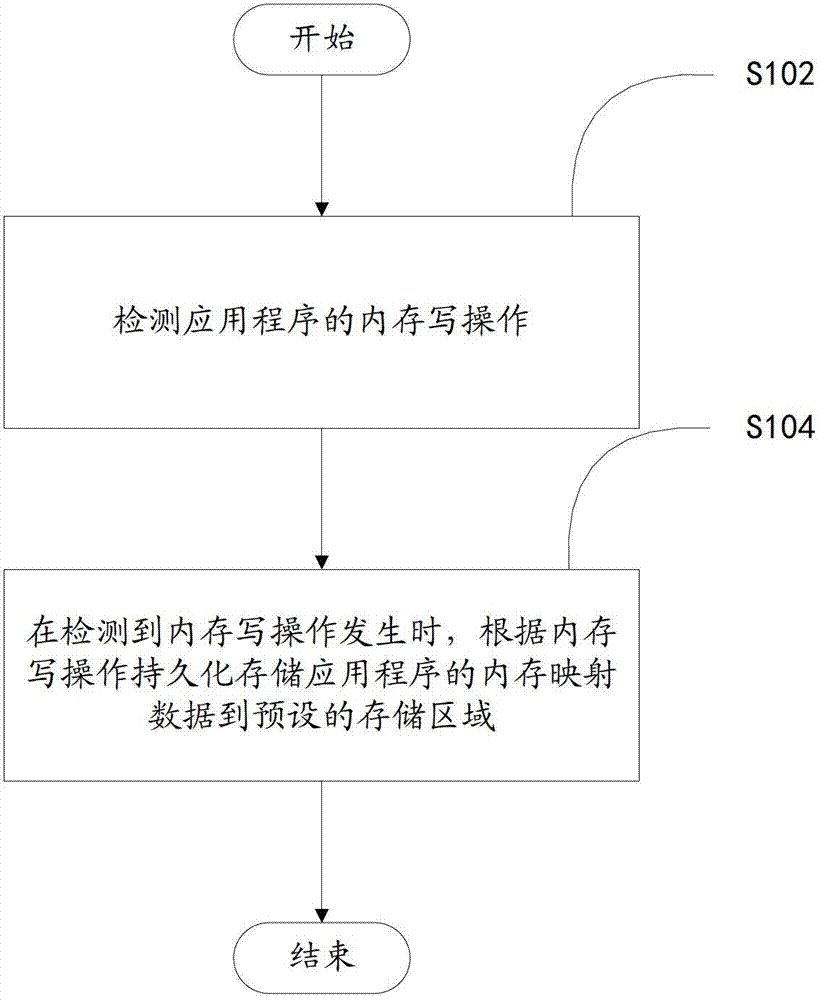
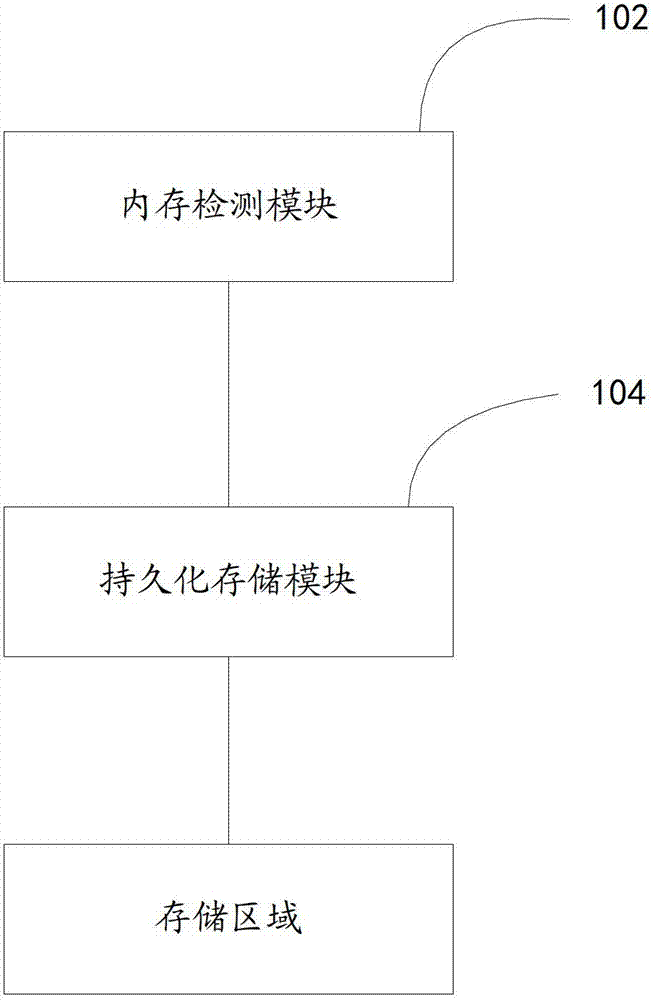
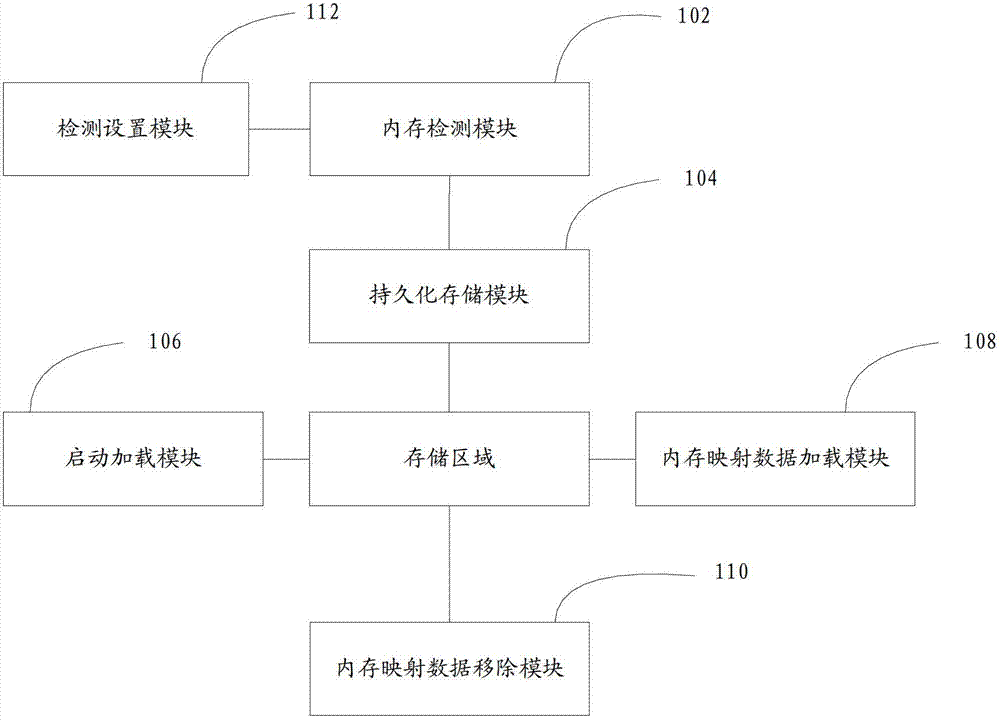
[0036] In one embodiment, such as figure 1 As shown, a data protection method includes the following steps:
[0037] Step S102 , detecting the memory write operation of the application program.
[0038] A memory write operation is an operation input by a user through an application program. For example, when a user is editing a document, the user can obtain the user's typing operation through the keyboard, and write the memory according to the typing operation, and generate a character string in the memory according to the writing operation. The text entered by the user is recorded in the memory through the memory write operation.
[0039] Step S104, when it is detected that a memory write operation occurs, persistently store the memory mapping data of the application program to a preset storage area according to the memory write operation.
[0040] Persistent storage is about storing data on disk, flash memory, or in a database. The data in the memory cannot be saved afte...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More