Data encryption method and system
A data encryption and data technology, applied in the field of communication, can solve the problems of low security and cracking by illegal users, and achieve the effect of improving security and convenience, improving security, and improving user experience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
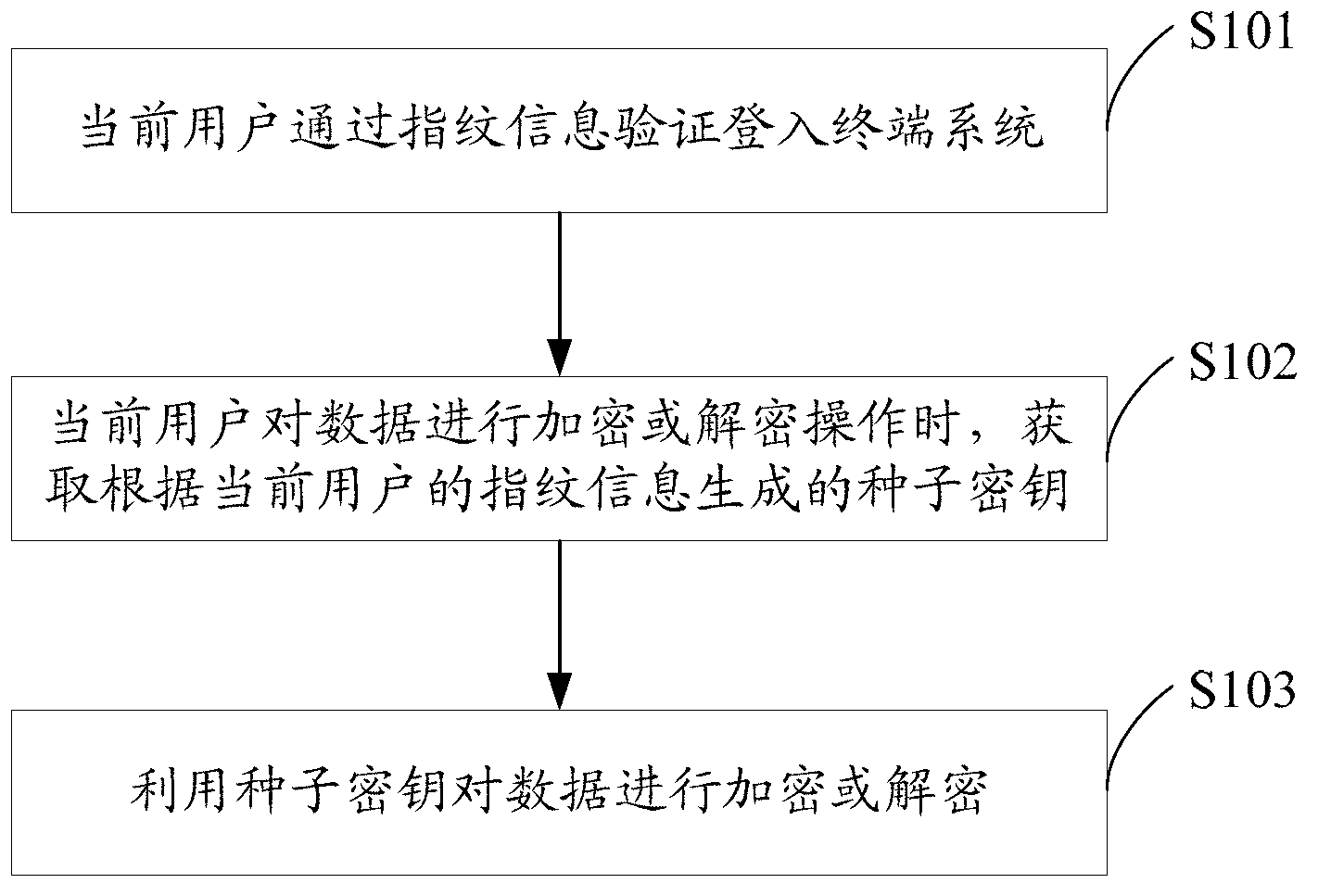
[0037] see figure 1 , propose the first embodiment of the data encryption method of the present invention, the data encryption method includes the following steps:
[0038] Step S101, the current user logs into the terminal system through fingerprint information verification.
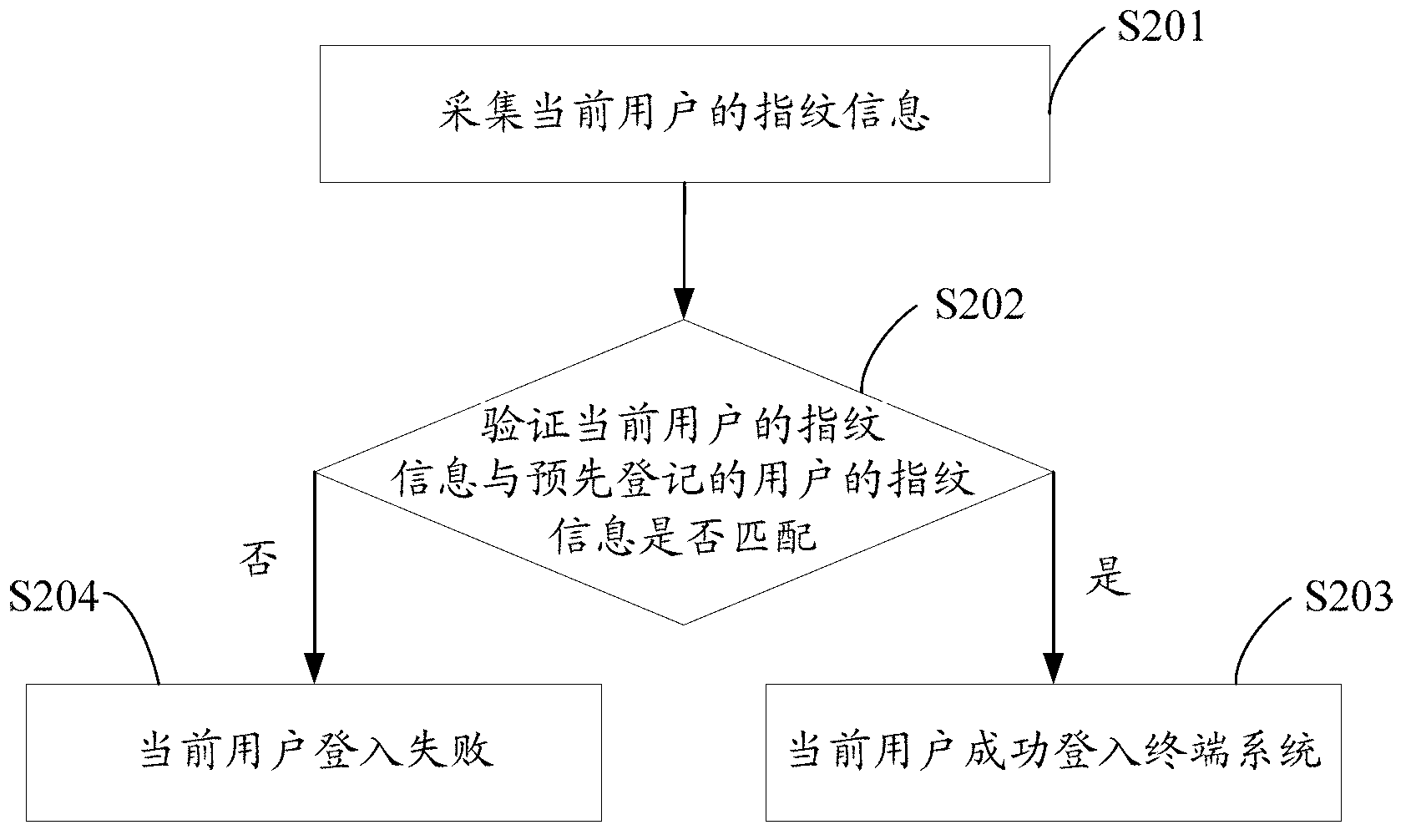
[0039] The fingerprint information of several users can be pre-registered in the terminal system to realize the management of multiple users in the same terminal system. The specific steps are: first create a user, then collect the fingerprint information of one or more fingers of the user, and finally generate the fingerprint of the user Information Sheet. Then pre-registered users can log in to the system through user authentication, that is, the current user logs in to the terminal system through fingerprint information verification, as follows: figure 2 Shown:
[0040] Step S201, collecting fingerprint information of the current user.
[0041] The current user inputs fingerprint information to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More