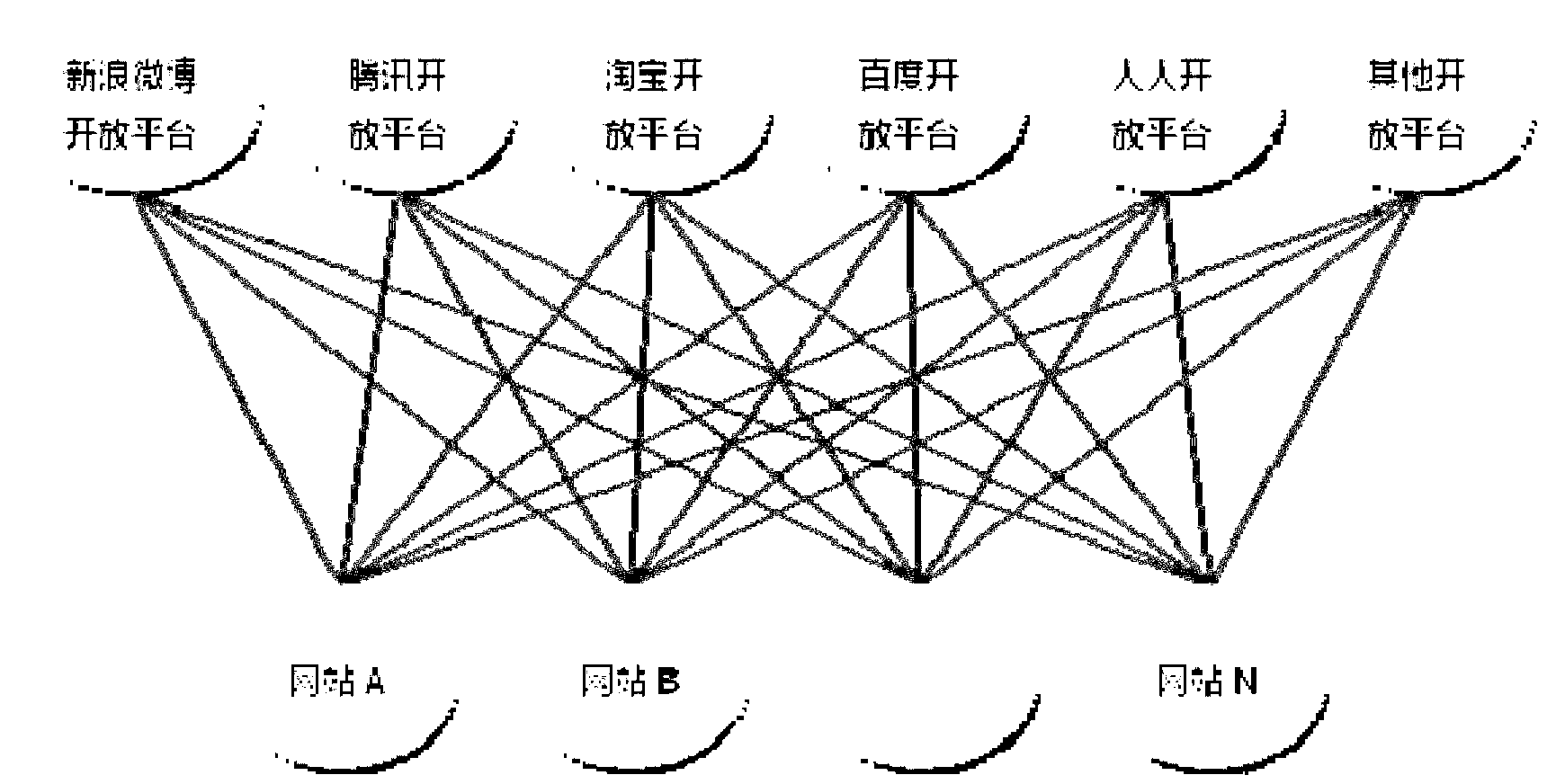
Social log-in method, system and device
A login method and a login request technology, applied in the computer field, can solve complex problems and achieve the effects of reducing complexity, improving efficiency, and reducing workload
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
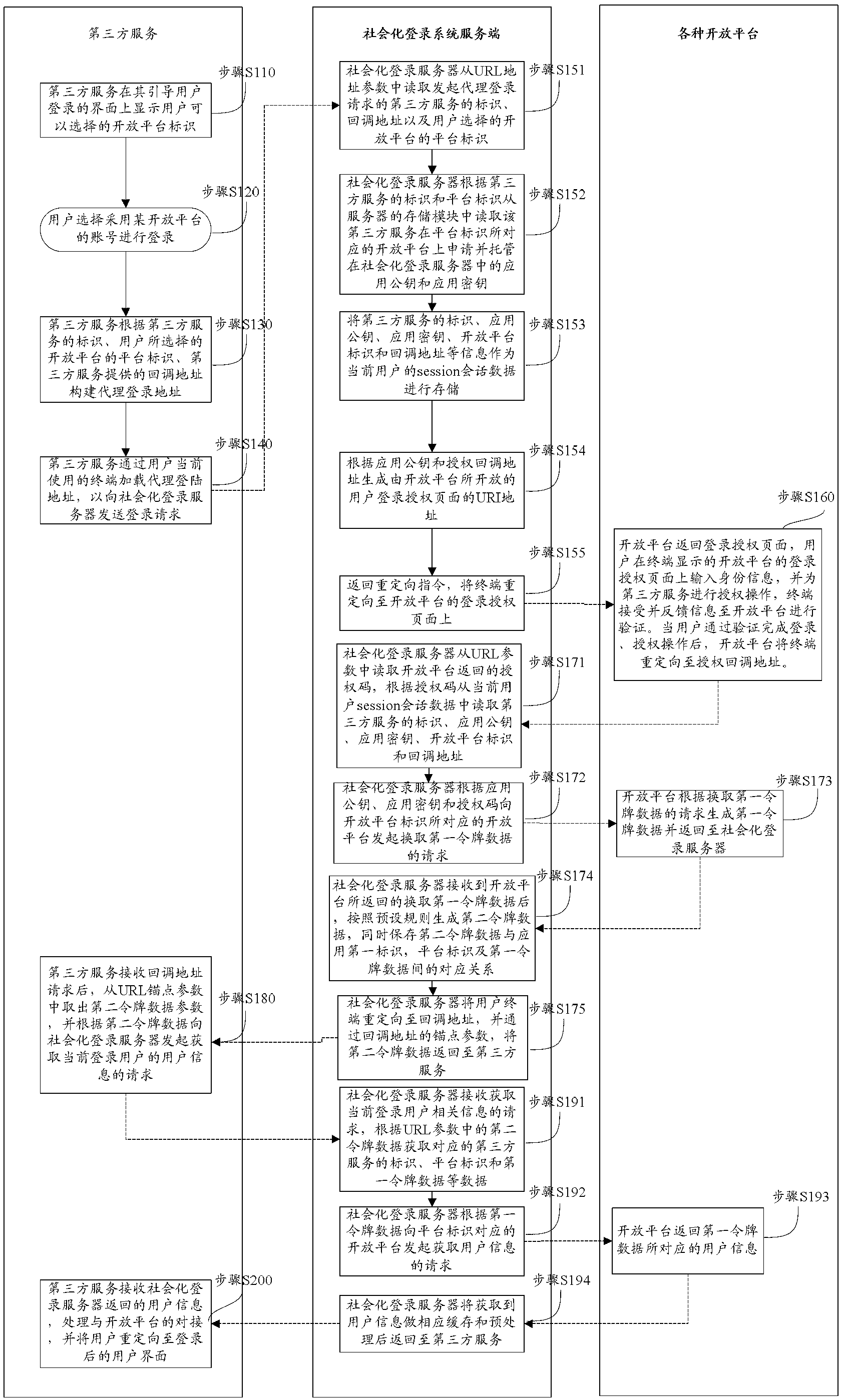
[0054] Embodiments of the present invention are described in detail below, and examples of the embodiments are shown in the drawings, wherein the same or similar reference numerals denote the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary only for explaining the present invention and should not be construed as limiting the present invention.
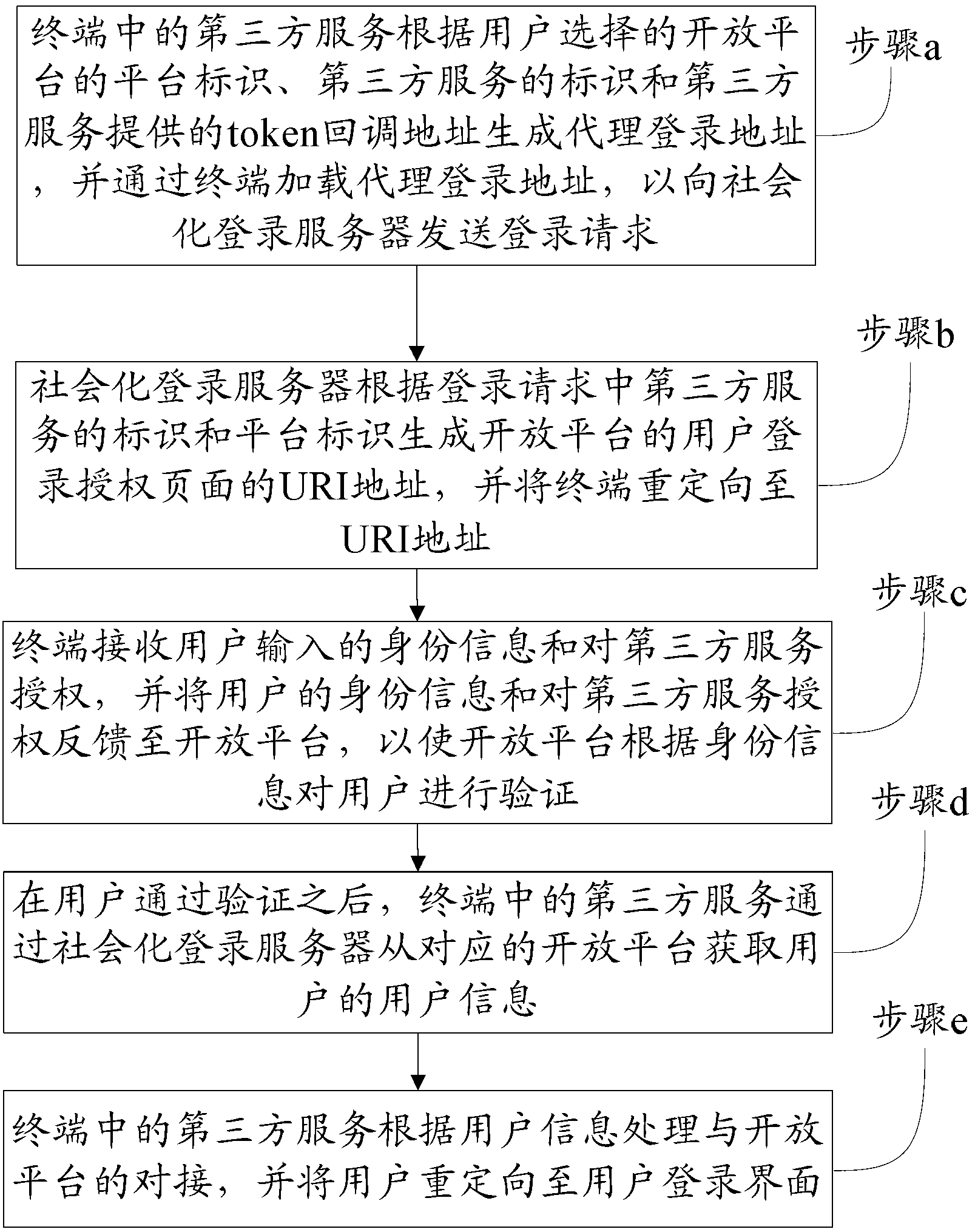
[0055] Refer below figure 2 A social login method according to an embodiment of the present invention is described, including the following steps:
[0056] Step a: The third-party service in the terminal generates a proxy login address based on the platform logo of the open platform selected by the user, the logo of the third-party service, and the token callback address provided by the third-party service, and loads the proxy login address through the terminal to contribute to the socialization The login server sends a logi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More