Unattended key management method
A key management and key technology, applied in the field of unattended key management, can solve problems such as hidden dangers, increase hidden dangers, and wrong key storage, and achieve the effect of avoiding damage, reducing hidden dangers, and ensuring reasonable utilization.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
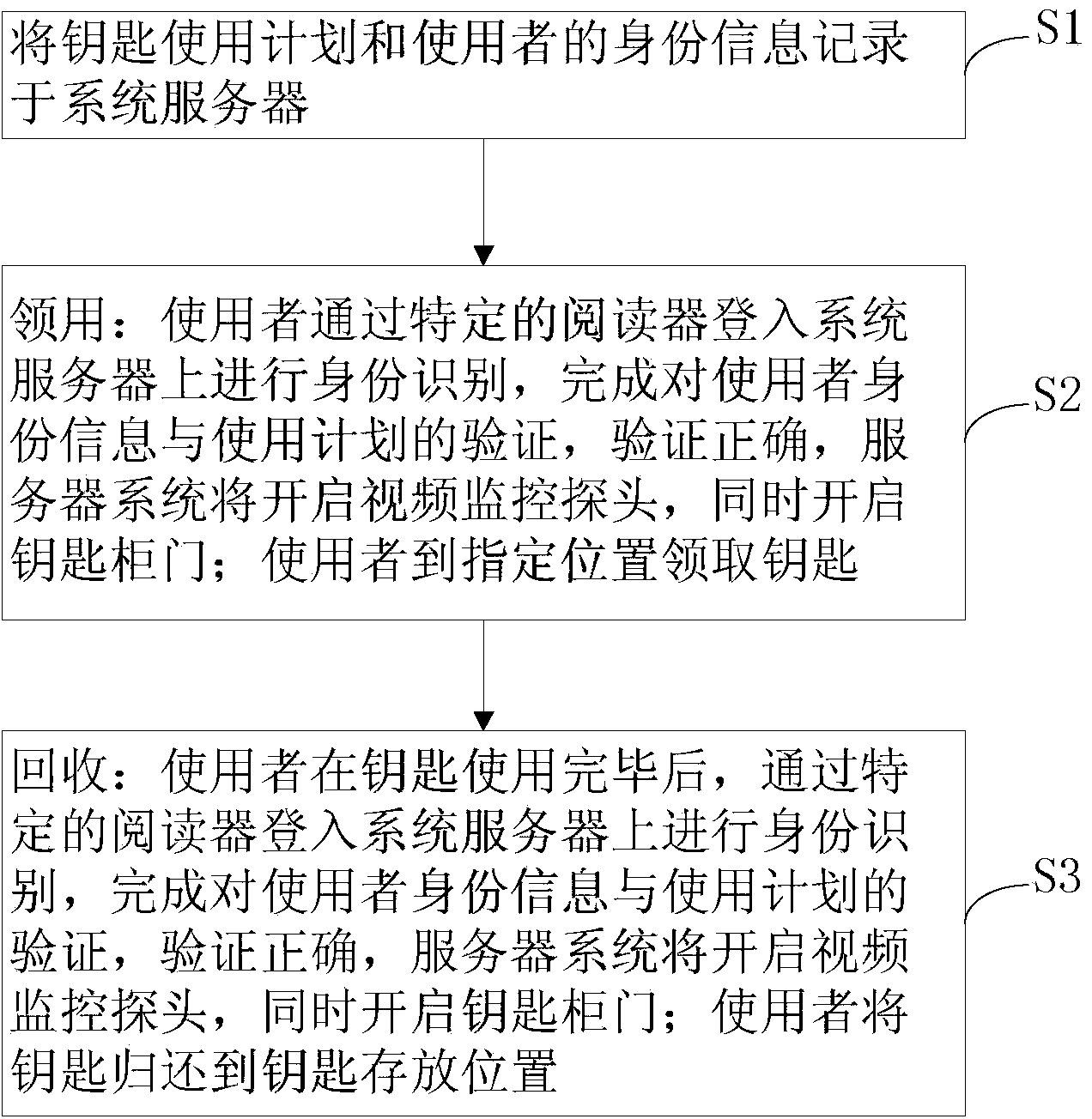
[0025] see figure 1 , the invention provides an unattended key management method, comprising the following steps:
[0026] S1. Record the key usage plan and the identity information of the user in the system server;
[0027] S2. Receiving: The user logs in to the system server through a specific reader for identification, and completes the verification of the user's identity information and usage plan. If the verification is correct, the server system will open the video surveillance probe and open the key cabinet door at the same time; use The visitor picks up the key at the designated location;
[0028] S3. Recycling: After using the key, the user logs in to the system server through a specific reader for identification, and completes the verification of the user's identity information and usage plan. If the verification is correct, the server syst...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More