Software secret key updating method and device
A software and key technology, which is applied to secure communication devices and key distribution, can solve problems such as updating software keys, and achieve the effect of preventing the problem of being unable to update
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
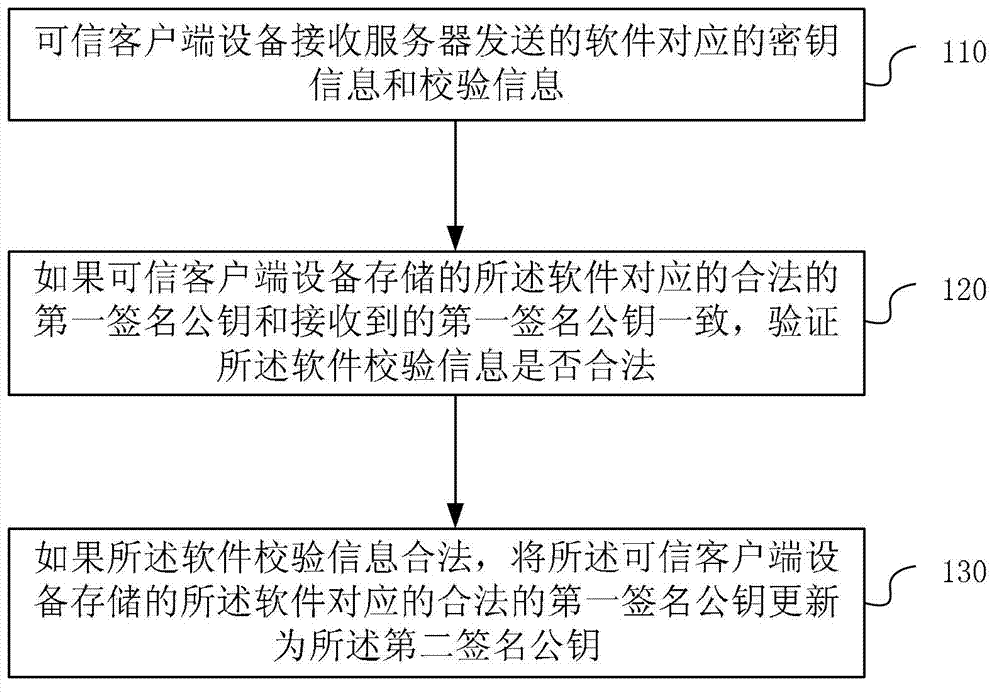
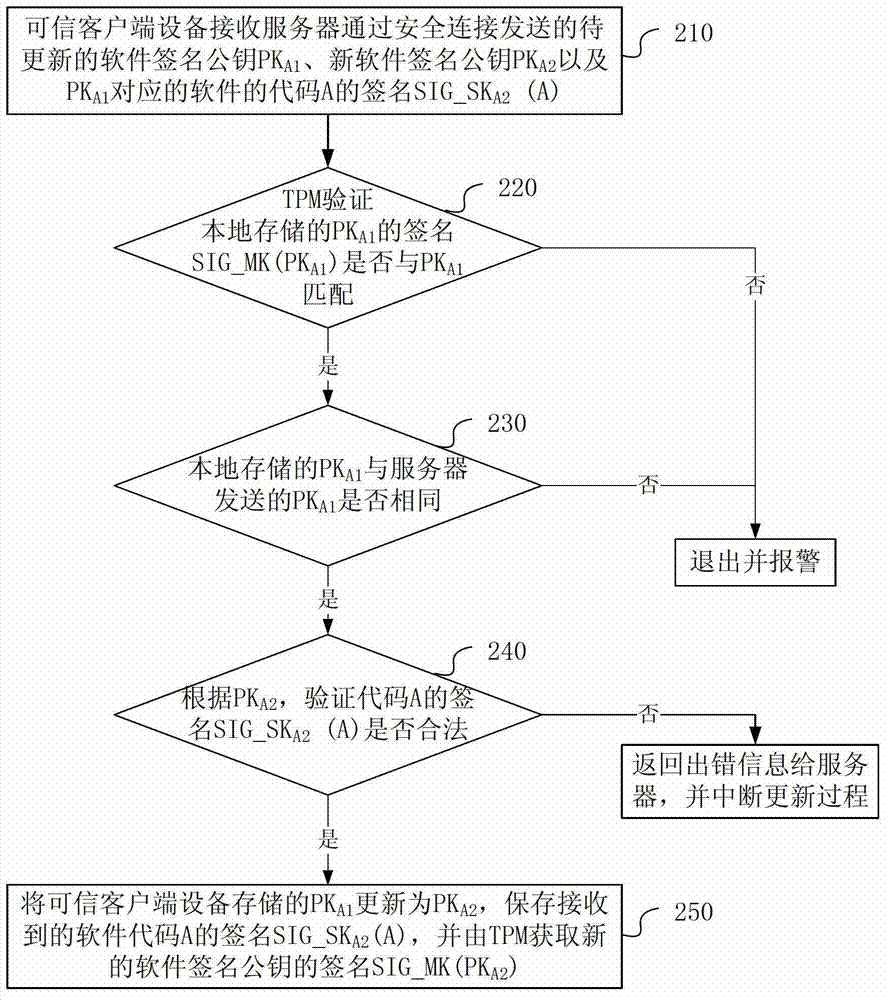
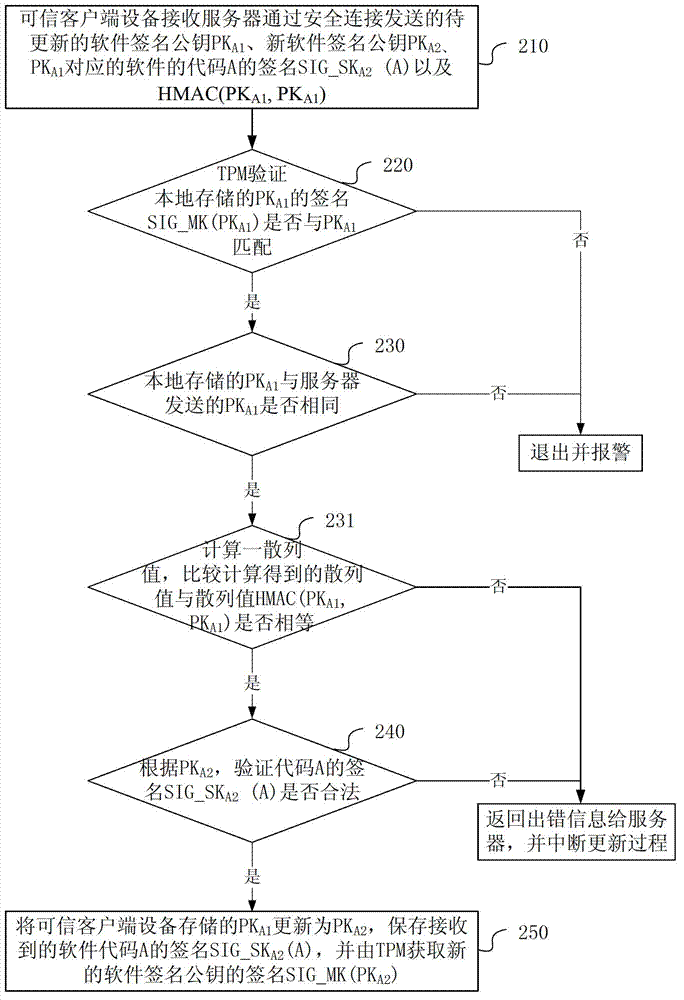
[0028] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. All other embodiments obtained by those skilled in the art based on the embodiments of the present invention belong to the protection scope of the present invention.
[0029] It should be noted that, in the case of no conflict, the embodiments of the present invention and the features in the embodiments can be combined arbitrarily with each other.
[0030] At present, the existing TrE technology has relatively mature and reliable solutions for managing and storing sensitive information. Due to the existence of the trust chain in the trusted environment, unauthorized access and modification of the software in the trusted client device is not allowed, and the legality ve...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More