Cloud data privacy protection public auditing method based on symmetric keys
A privacy protection and symmetric key technology, which is applied in the field of cloud computing security, can solve the problems of not being able to provide public auditing and privacy protection security performance at the same time, and high overhead, and achieve the effect of saving computing and storage costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0017] In order to make the technical means, creative features, goals and effects achieved by the present invention easy to understand, the present invention will be further described below in conjunction with specific illustrations.
[0018] Before giving the specific implementation process of the scheme, explain the four definitions:
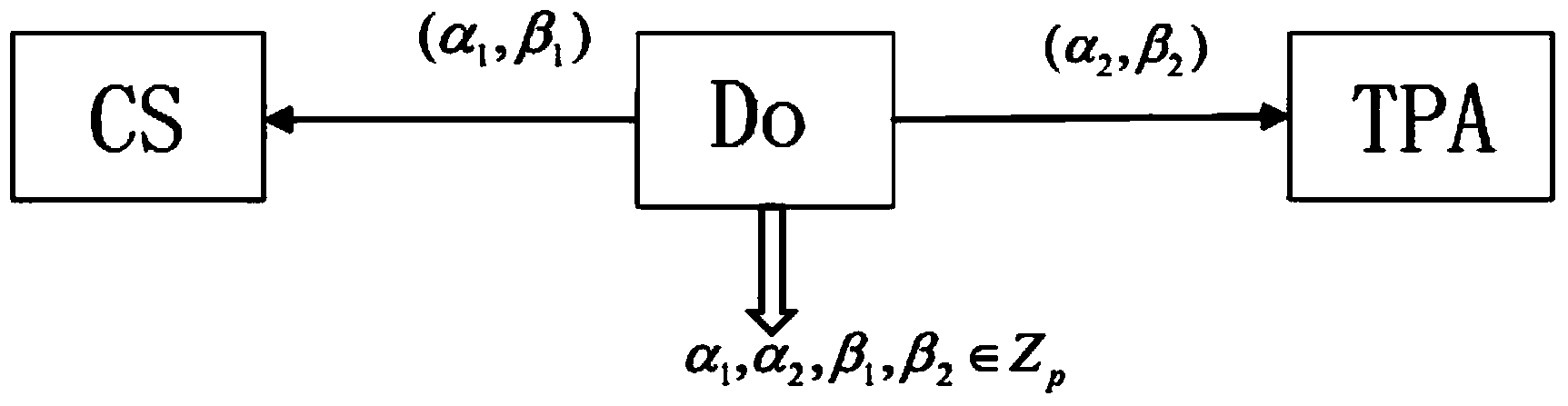
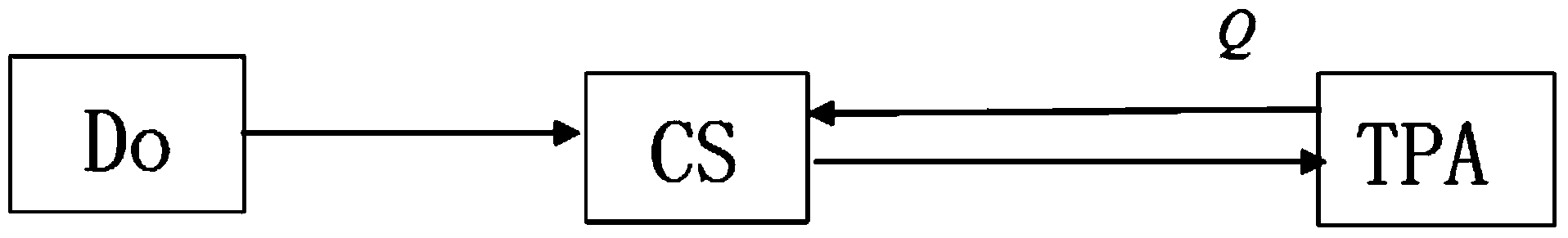
[0019] (1) Four entities in the scheme: data owner DO, cloud server CS, third-party audit TPA and users. DO has a set of data blocks M, for each data block m i ∈M generates a signature σ i , a set of signatures σ i Represented by Φ; the main function of CS is to be responsible for content management, storing data block M and signature Φ, all data information related to service content is stored on CS, and allows the client to download or update content information; when receiving When the user data audit request is received, TPA submits the request to the cloud service provider, audits the relevant data information returned by the cloud ser...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More