Network security verification method and system for distributed system
A distributed system and network security technology, applied in the network security verification method and system field of distributed systems, can solve problems such as difficult expansion and maintenance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
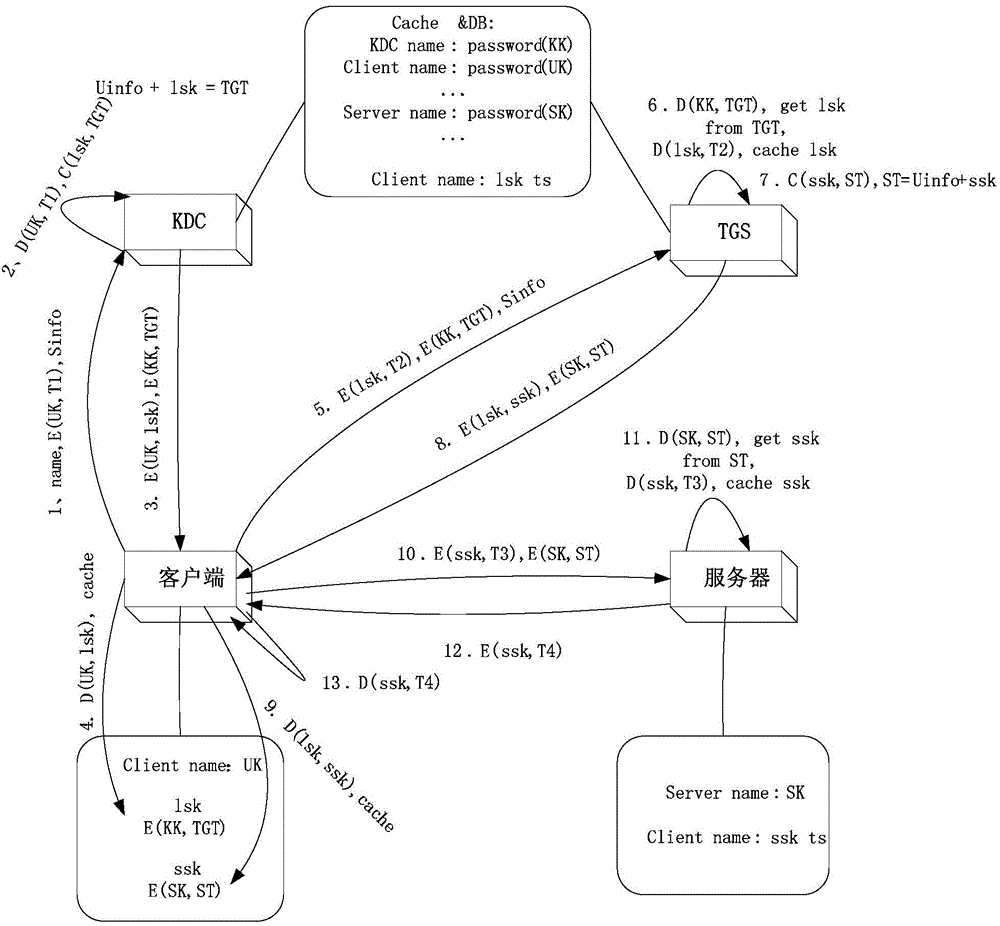
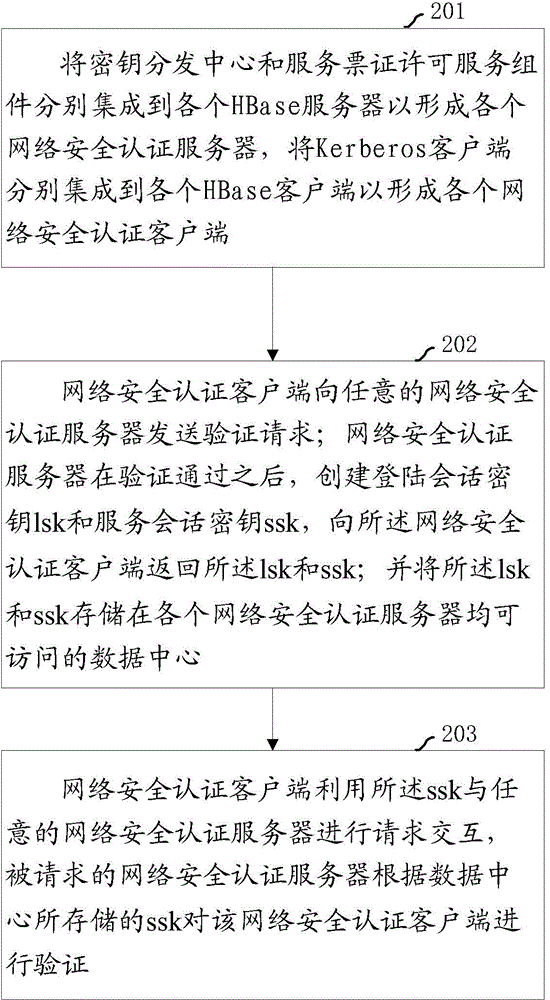
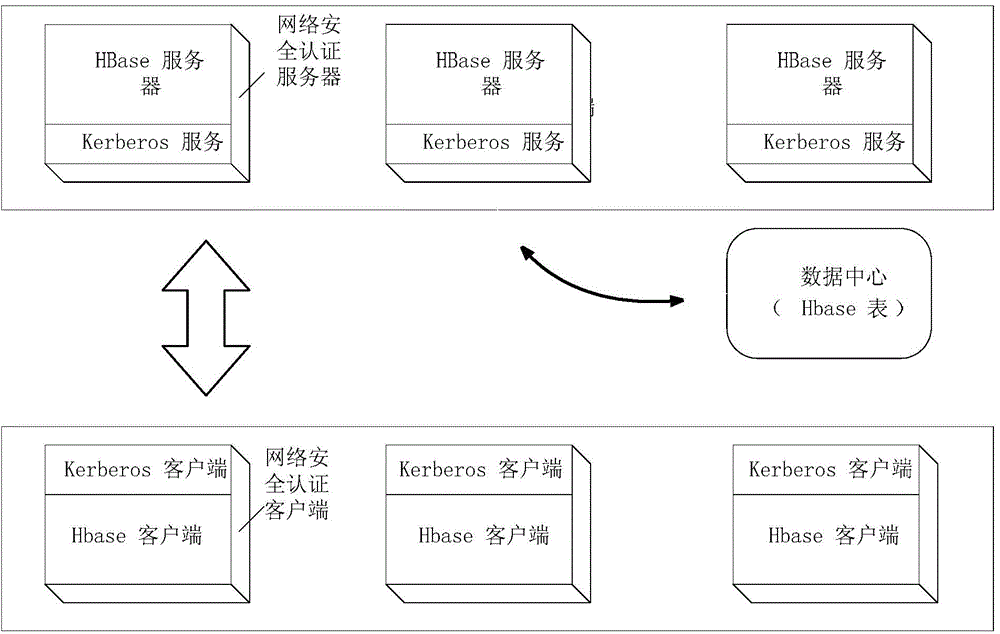
[0044] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
[0045] For the sake of brevity and intuition in description, the solution of the present invention is described below by describing several representative implementation manners. Numerous details in the embodiments are only used to help the understanding of the solutions of the present invention. But obviously, the technical solutions of the present invention may not be limited to these details when implemented. In order to avoid unnecessarily obscuring the solution of the present invention, some embodiments are not described in detail, but only a framework is given. Hereinafter, "including" means "including but not limited to", and "according to..." means "at least according to, but not limited to only based on...". Due to the language habits of Chinese, when t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More