User interaction method and device based on access control system
An access control system and user technology, applied in the direction of user identity/authority verification, instruments, time registers, etc., can solve the problem that hidden danger information is difficult to guarantee the authenticity, and achieve the effect of guaranteeing the authenticity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
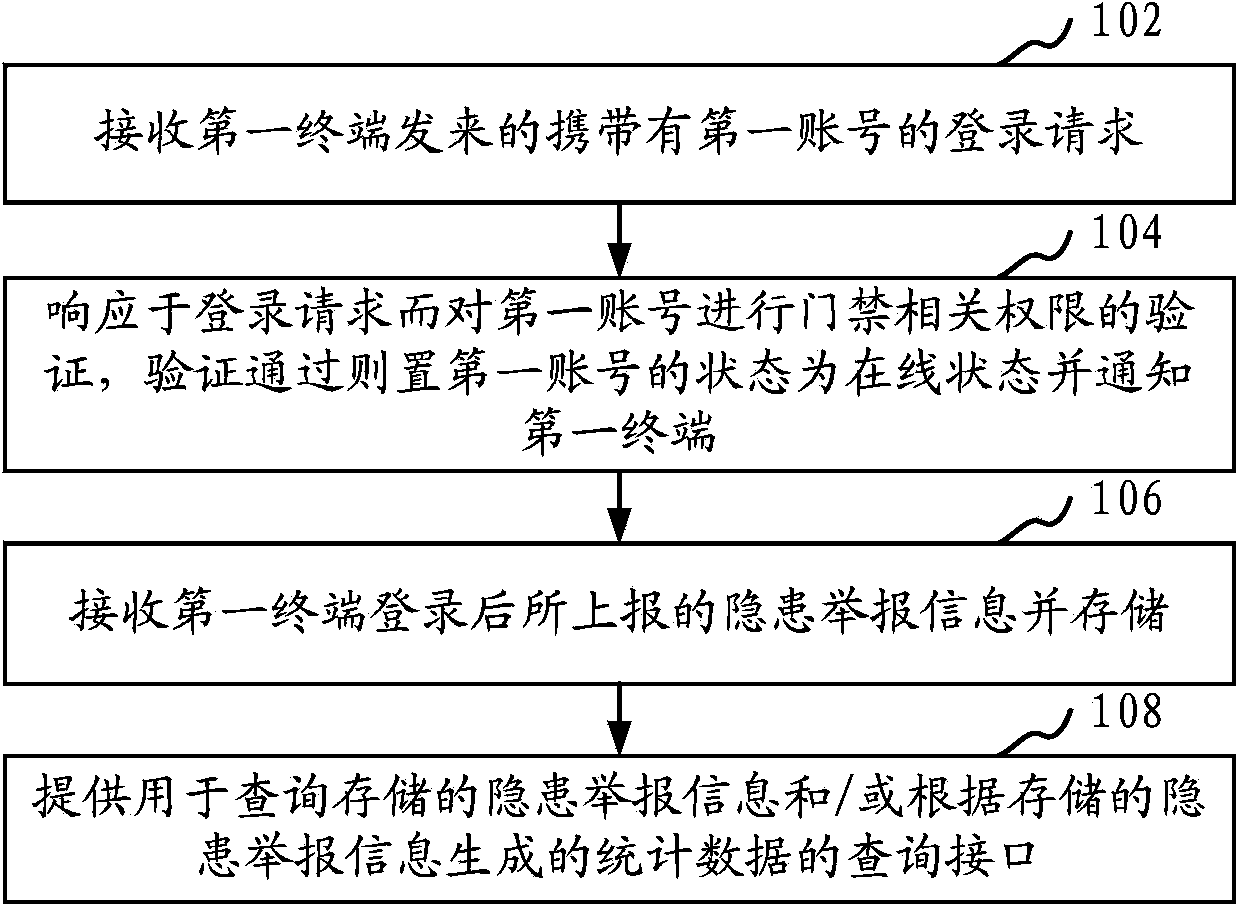
[0023] Such as figure 1 As shown, in one embodiment, a user interaction method based on an access control system is provided, and this embodiment is described by taking the method applied to an application server as an example. The method specifically includes the following steps:
[0024] Step 102, receiving a login request carrying the first account from the first terminal.
[0025] The first description of the first terminal is used to distinguish it from the second terminal and the third terminal described below. The first terminal can run a specified application client, and the application ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More