Method and device for verifying identity of user
A user identity and user technology, applied in the field of information security, can solve the problems of forgetting answers, unable to provide continuous verification, mobile phone Trojan horses, etc., to ensure security and achieve the effect of sustainable identity verification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0060] In order to make the above objects, features and advantages of the present invention more comprehensible, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
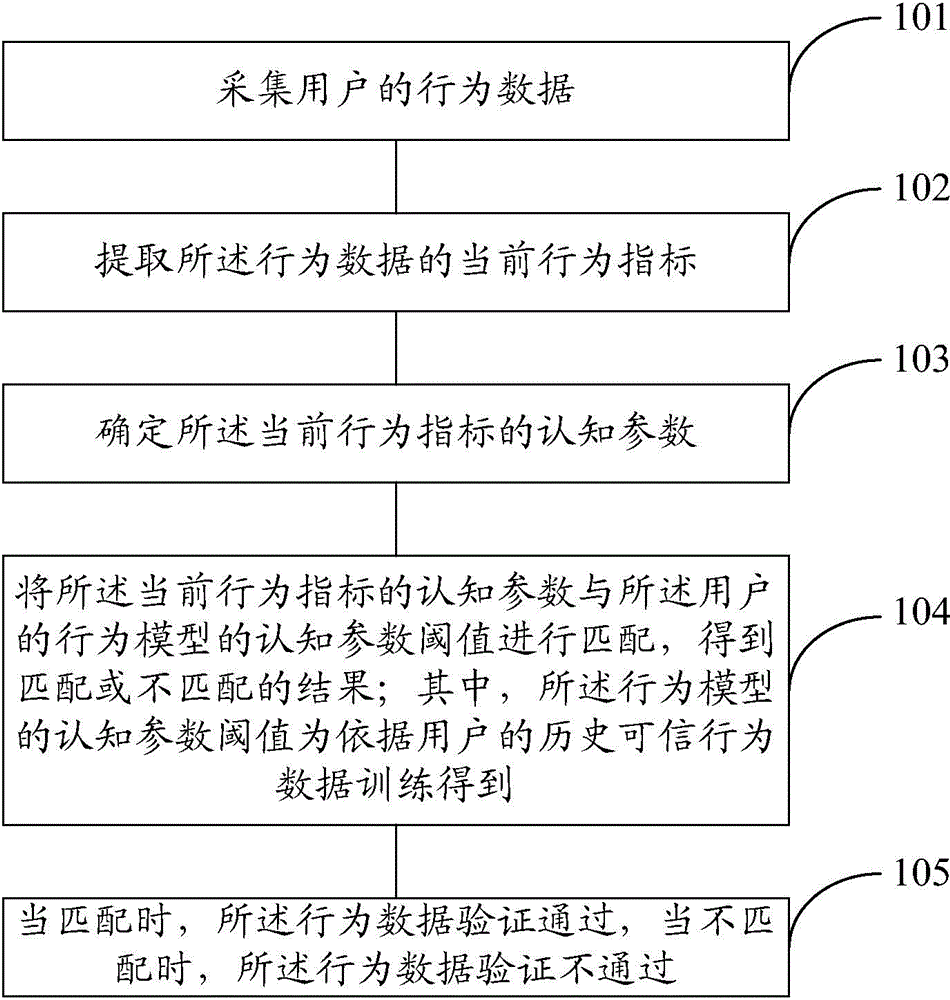
[0061] refer to figure 1 , which shows a flow chart of steps of an embodiment of a method for verifying user identity in the present invention, which may specifically include the following steps:
[0062] Step 101, collecting user behavior data;
[0063] Embodiments of the present invention can be applied to interactive interfaces of various Internet applications such as browsers and APP (Application Programs, Application) clients. Behavioral data of users, so as to realize continuous authentication of user behavior data. Wherein, websites of various Internet applications can be run on the browser, and APP clients can be clients of various online banks and various e-commerce companies.
[0064] In a specific implementation, the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More