Multi-mobile terminal-based data security protection method and device
A mobile terminal and data security technology, applied in the field of data security, can solve problems such as inconvenient operation, and achieve the effect of good convenience and data protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] In order to make the technical problems solved by the present invention, the technical solutions adopted and the technical effects achieved clearer, the technical solutions of the embodiments of the present invention will be further described in detail below in conjunction with the accompanying drawings. Obviously, the described embodiments are only the technical solutions of the present invention. Some, but not all, embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without creative efforts fall within the protection scope of the present invention.
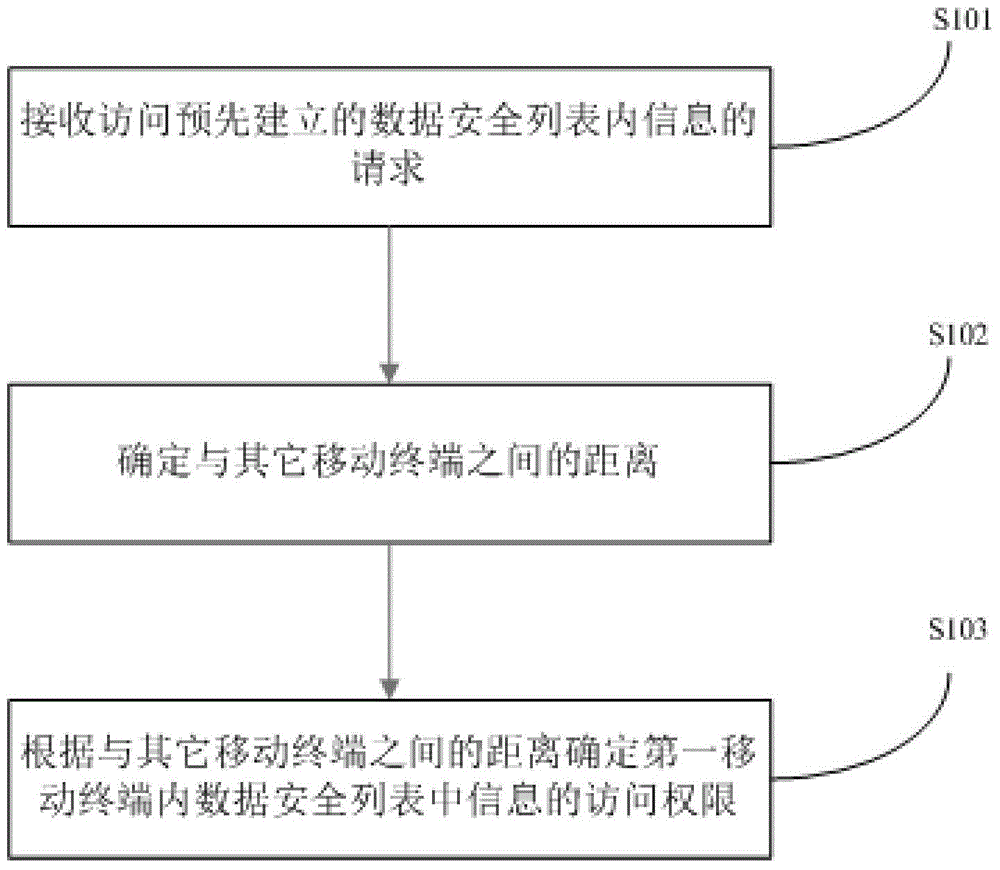
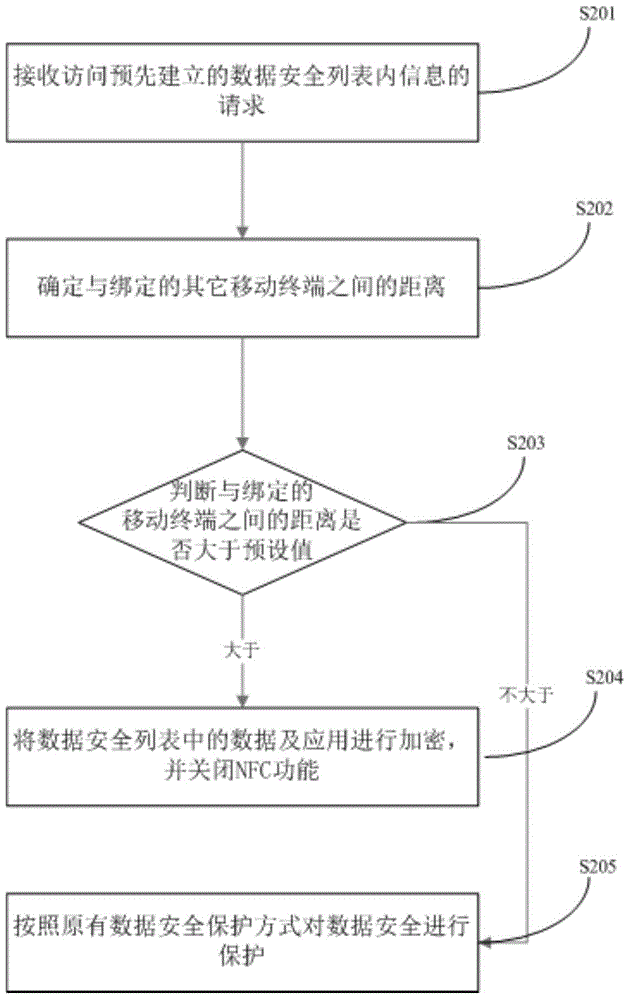
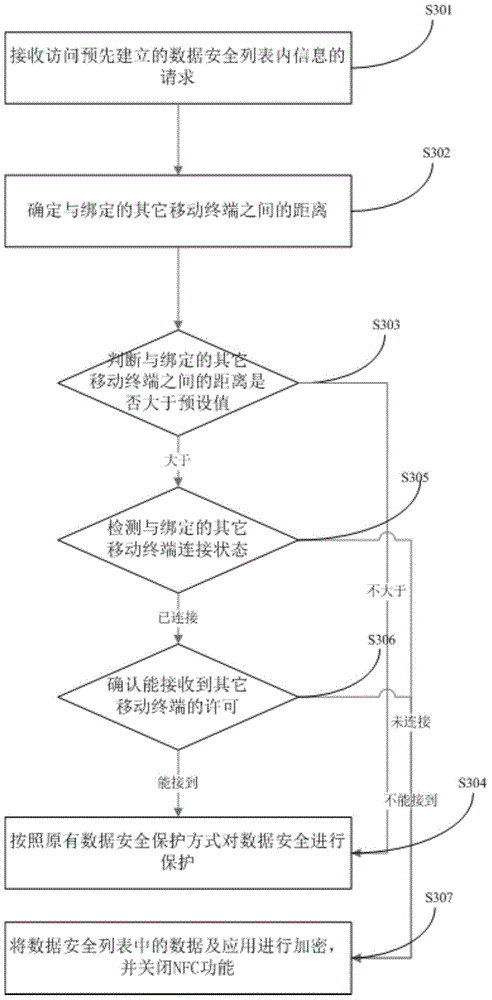
[0037] refer to figure 1 , figure 1 It is a method for protecting data security based on multiple mobile terminals in the first embodiment of the present invention, wherein the mobile terminal refers to computer equipment that can be used on the move, broadly speaking, it includes mobile phones, notebooks, tablet computers, POS machines, and even vehi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More