A Proxy Re-Encryption Method for Improving the Sharing Function of Outsourced Encrypted Data
A proxy re-encryption and encrypted data technology, applied in transmission systems, electrical components, etc., can solve problems such as high overhead, high calculation and transmission overhead, and inability to realize multi-user broadcasting
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0074] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below may be combined with each other as long as they do not constitute a conflict with each other.
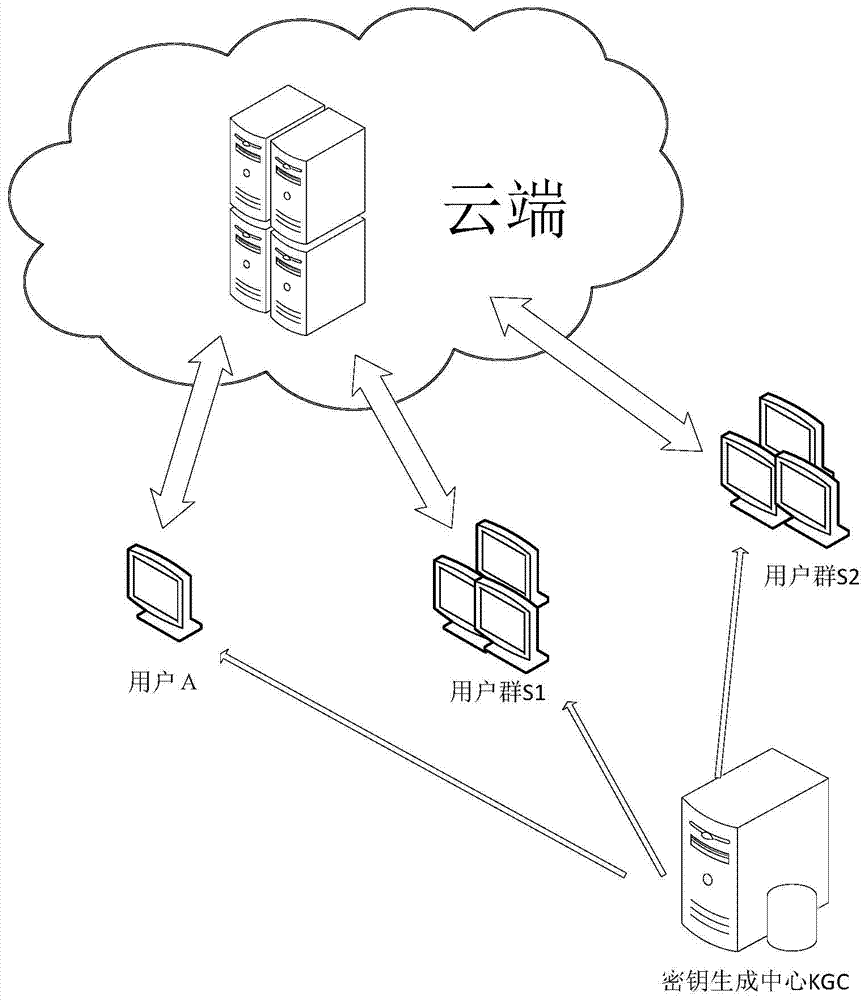
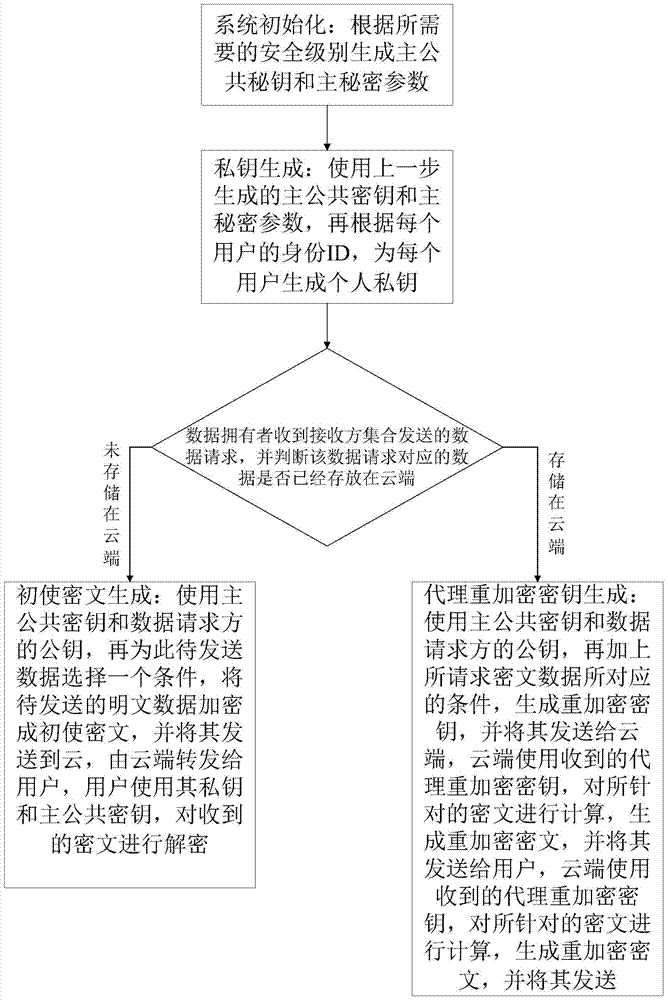
[0075] Such as figure 1 As shown in , it shows the application environment diagram of the method of the present invention. The method involves three entities: a user, a Key Generation Center (KGC for short), and a data storage cloud (Cloud). The user can encrypt the initial ciphertext for a friend and send it to the cloud. If a friend requests an existing ciphertext, the user is responsible for...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap