System and method for terminal security access authentication
An access authentication and terminal security technology, applied in the field of communication, can solve the problems of poor security, sensitive information leakage, illegal occupation of server resources, etc., and achieve the effect of ensuring safe transmission, ensuring security, and improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] Embodiments of the present invention are further described below in conjunction with accompanying drawings:
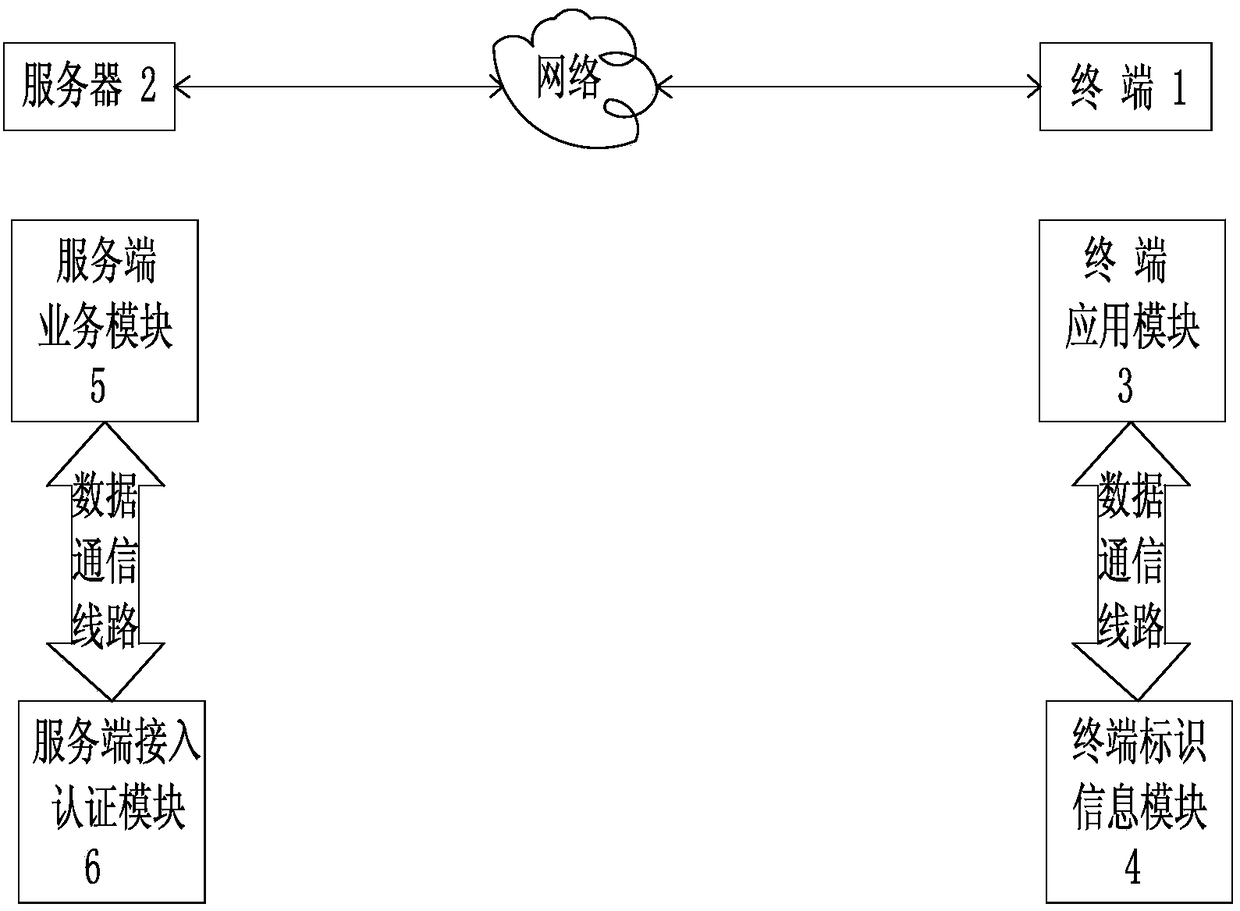
[0026] Such as figure 1 As shown, the system for terminal security access authentication described in the present invention includes a terminal 1 and a server 2, and the terminal 1 and the server 2 are connected through a network;
[0027] The terminal 1 includes a terminal application module 3 and a terminal identification information module 4, and the terminal application module 3 and the terminal identification information module 4 are connected by a data communication line;
[0028] Described server 2 comprises service end service module 5 and service end access authentication module 6, service end service module 5 and service end access authentication module 6 are connected by data communication line;
[0029] The terminal application module 3 is connected to the server service module 5 through a network;
[0030] Such as figure 2 As shown, the authenti...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More