A searchable encryption method based on Chinese in cloud environment
An encryption method and cloud environment technology, applied in the direction of file system, file management system, file access structure, etc., can solve the problem of poor usability of search system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0057] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
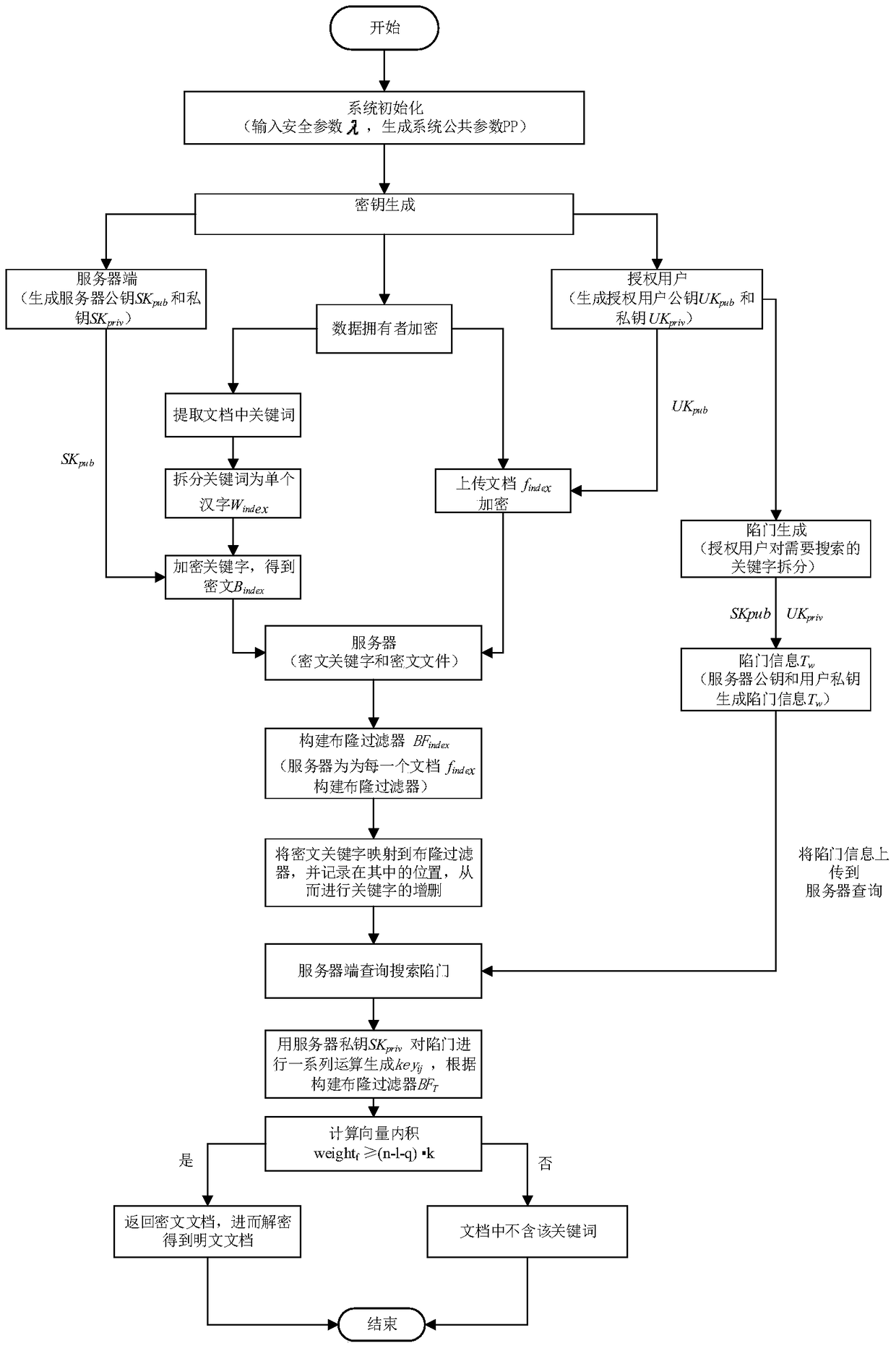
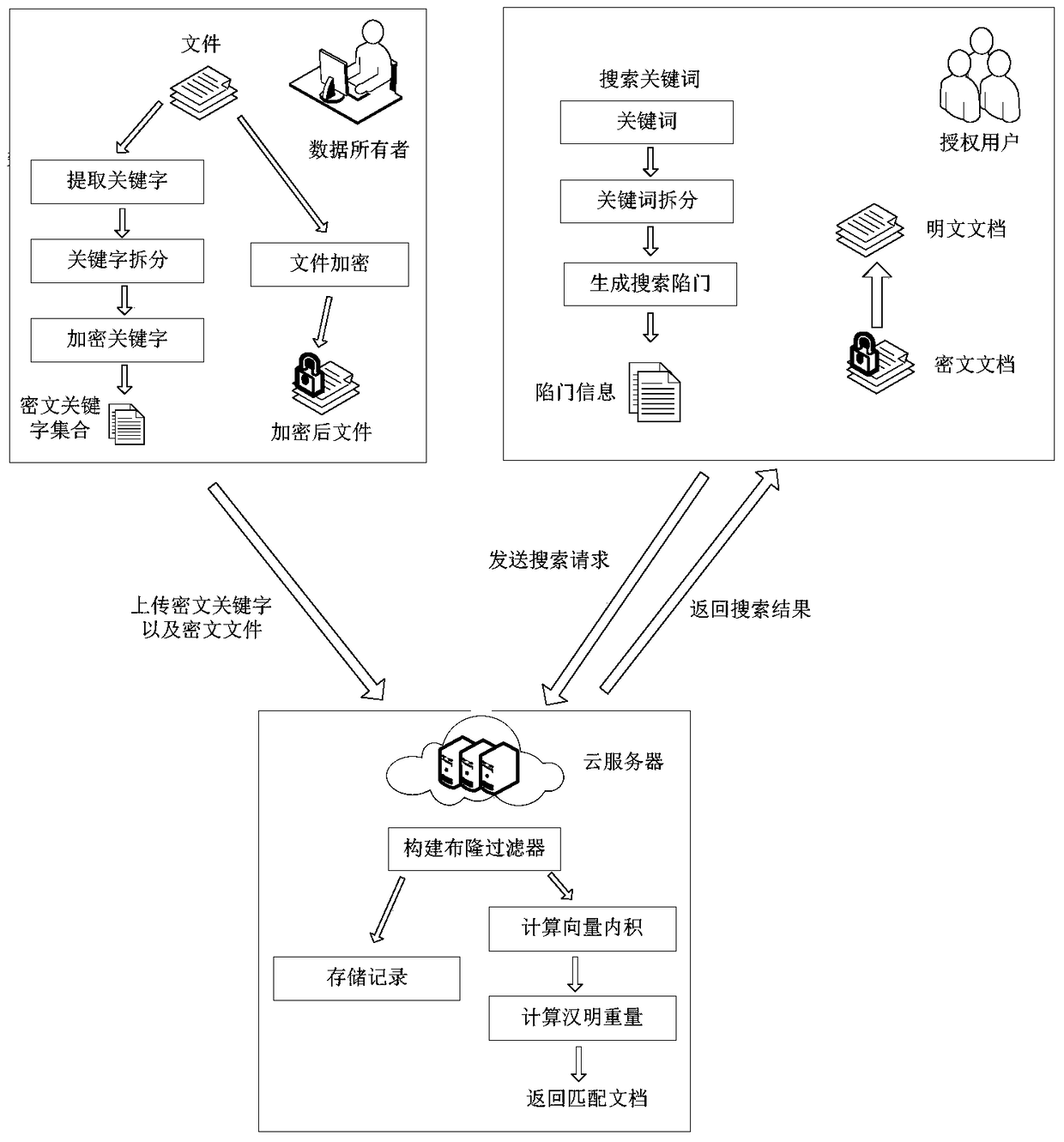
[0058] The invention mainly includes file upload encryption, key generation, keyword encryption, construction of Bloom filter and trapdoor generation, and finally completes ciphertext search. The data owner uses an encryption algorithm to encrypt the file, and the encrypted file set C is formed after encryption. In order to enable authorized users to search for ciphertext in the encrypted file set C, the data owner needs to extract keywords from the files in the file data set F, and perform searchable encryption on the extracted keywords. Encryption processing, and then upload the encrypted document collection C and the ci...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More