Key instruction processing method and terminal
An instruction processing and terminal technology, applied in the security field, can solve the problems of user economic loss, remote monitoring, positioning and alarm failure, and no protection measures for keys, and achieve the effect of preventing malicious operations.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
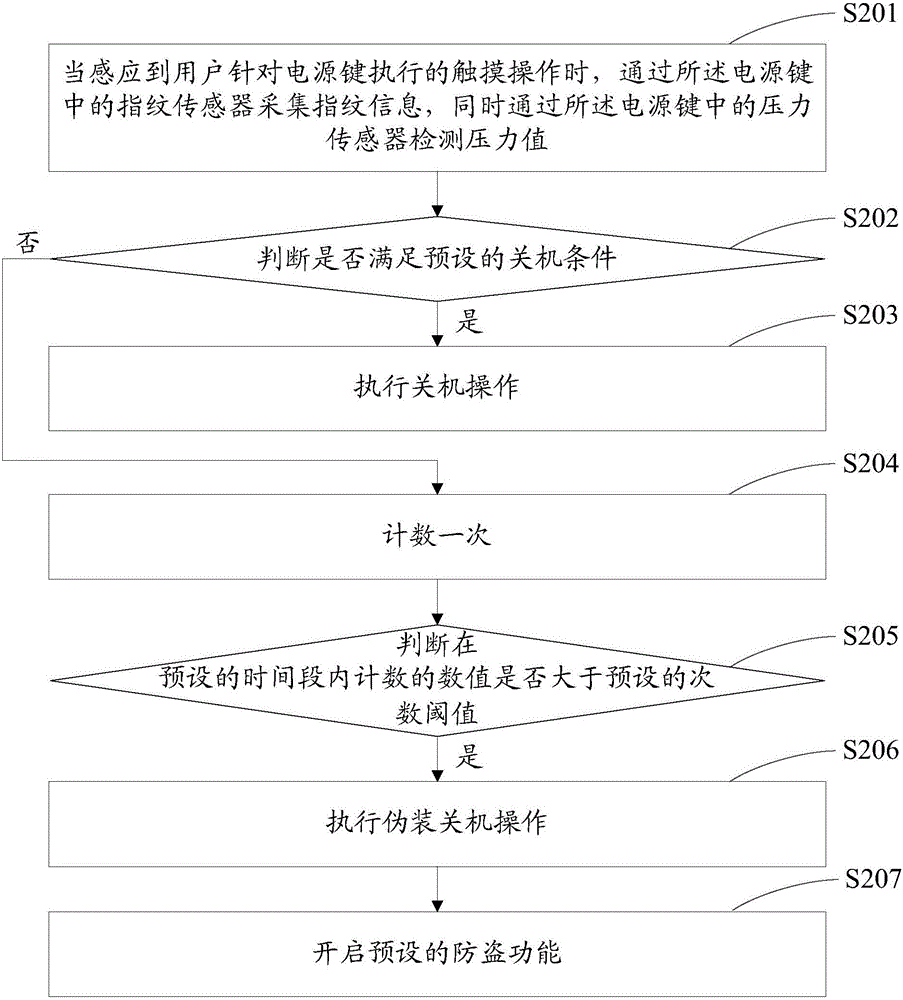
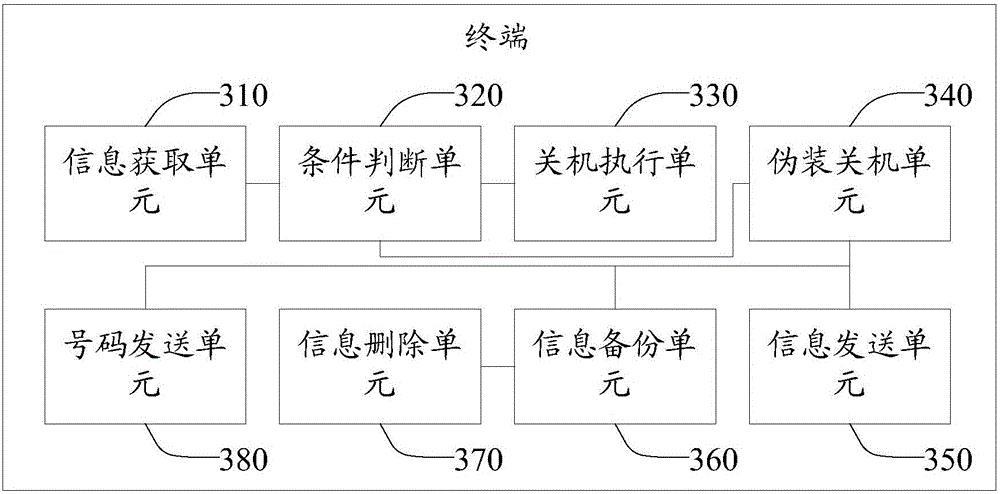
[0020] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are some of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
[0021] The shutdown method provided by the embodiment of the present invention is implemented in a terminal, and the terminal includes electronic devices such as smart phones, tablet computers, digital audio and video players, e-readers, handheld game consoles, or vehicle-mounted electronic devices. Wherein, a fingerprint sensor and a pressure sensor are arranged in the keys of the terminal.
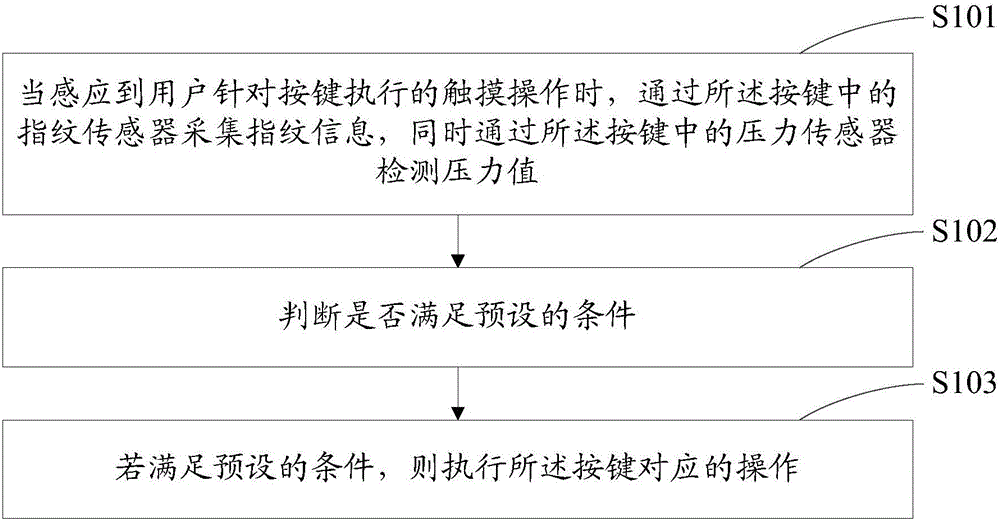
[0022] figure 1 It is a schematic flow chart of a key inst...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More