User behaviour based data verification method and device
A data verification and user technology, applied in the direction of digital data authentication, etc., can solve the problem of low security, achieve the effect of reducing security risks and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
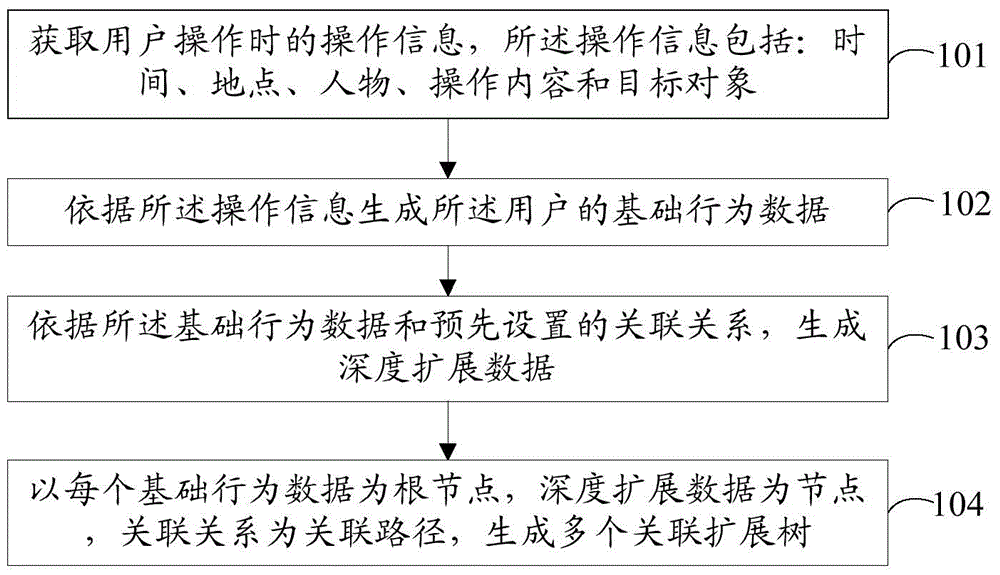
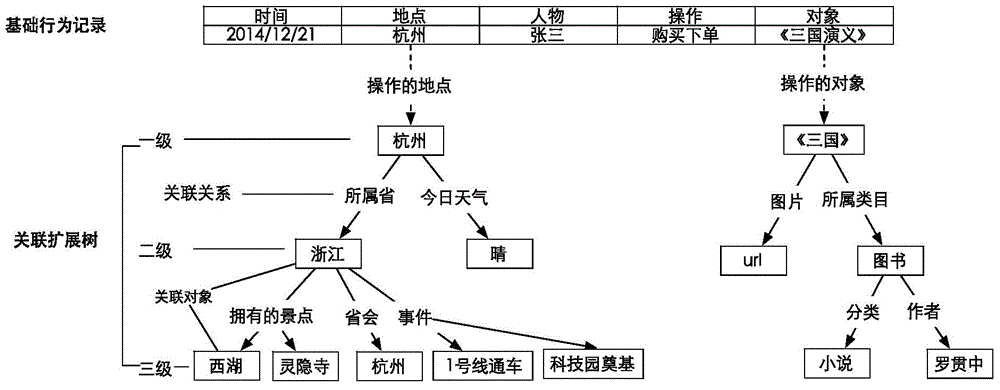
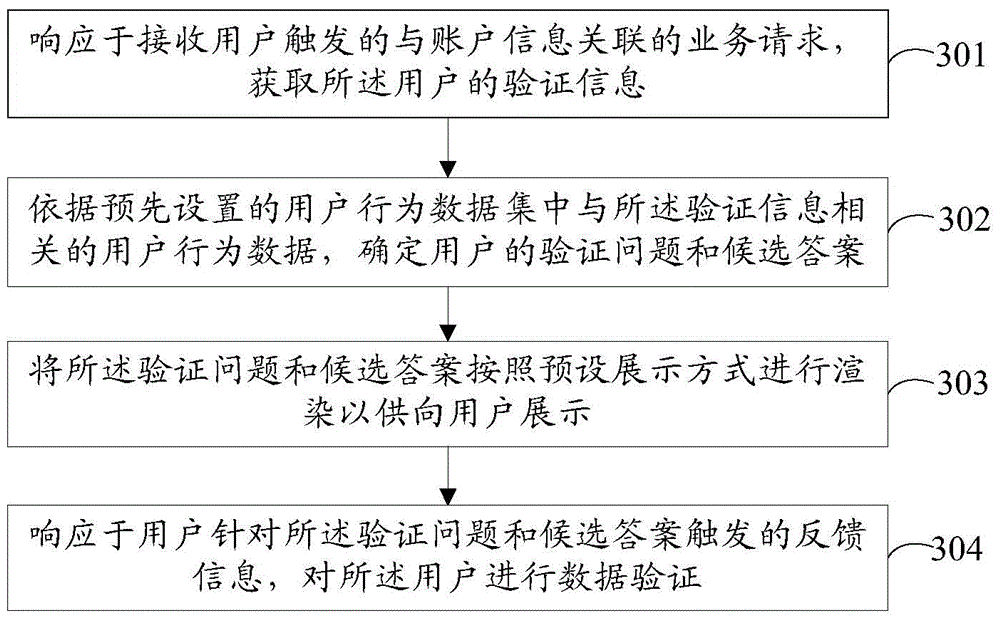
Method used
Image
Examples
Embodiment Construction
[0037] The technical solutions in the embodiments of the present application will be clearly and completely described below with reference to the drawings in the embodiments of the present application. Obviously, the described embodiments are only a part of the embodiments of the present application, but not all of the embodiments. Based on the embodiments in the present application, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of the present application.
[0038] The present application may be used in numerous general purpose or special purpose computing device environments or configurations. For example: personal computers, server computers, handheld or portable devices, tablet-type devices, multi-processor devices, distributed computing environments including any of the above, and the like.
[0039] The application may be described in the general context of computer-executable instructio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More