System, method and computer readable medium for providing security measures under the ble protocol
A computer and protocol technology, applied in the field of data distribution security, can solve problems such as lack of security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0019] In the following description, reference is made to the accompanying drawings which form a part hereof, and in which are shown by way of illustration specific embodiments in which the disclosure may be practiced. It is to be understood that other embodiments may be utilized and structural changes may be made without departing from the scope of the present disclosure.
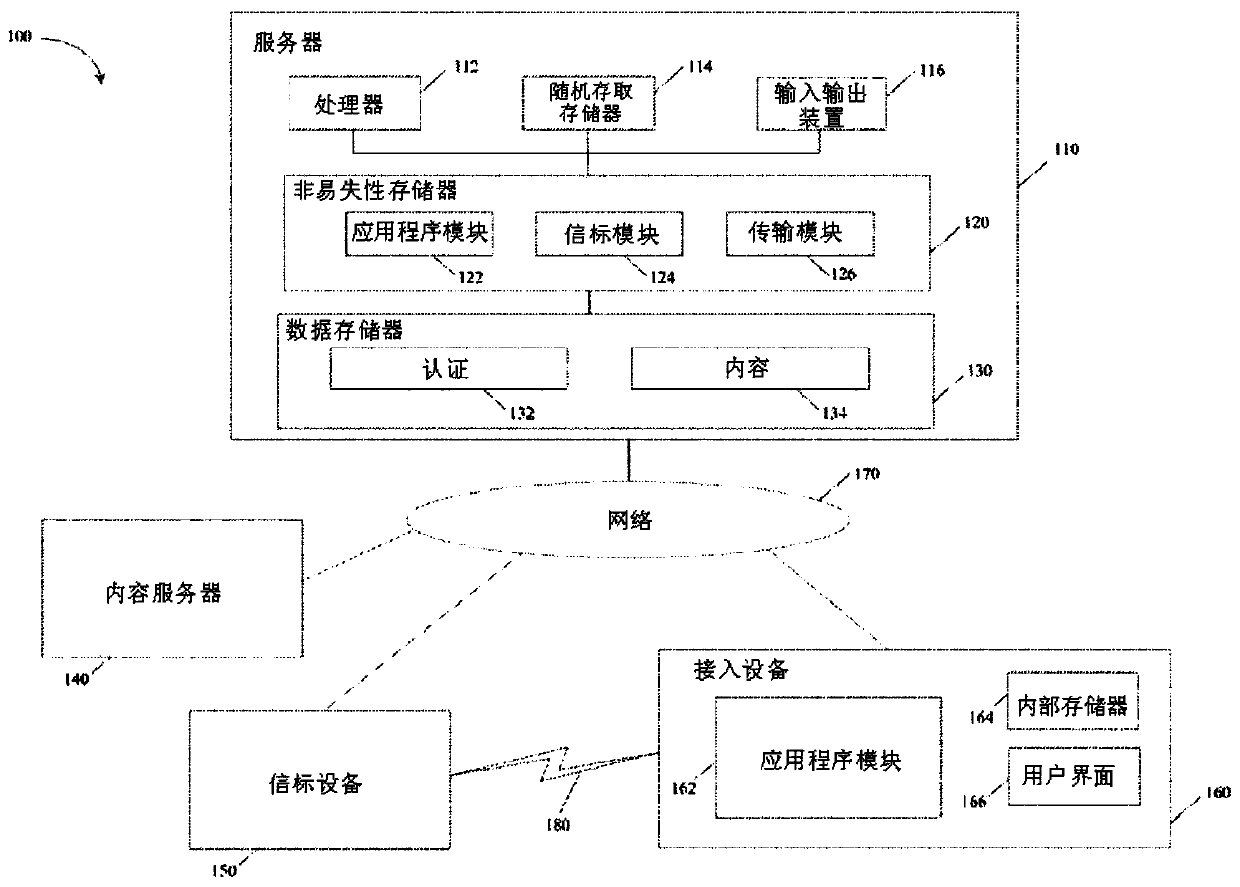
[0020] now refer to figure 1 , shows an example of a suitable computing system 100 within which embodiments of the disclosure may be implemented. Computing system 100 is an example only, and is not intended to suggest any limitation as to the scope of use or functionality of the present disclosure. Neither should the computing system 100 be interpreted as having any dependency or requirement relating to any one or combination of components illustrated.
[0021] For example, the present disclosure operates with numerous other general or special purpose computing consumer electronics, network PCs, minicomp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More