Privacy protection K-NN (Kth Nearest Neighbor) classification method based on vector homomorphic encryption
A homomorphic encryption and privacy protection technology, applied in the field of vector classification, can solve the problems of estimated density diffusion, heavy calculation burden, etc., and achieve the effect of accurate classification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
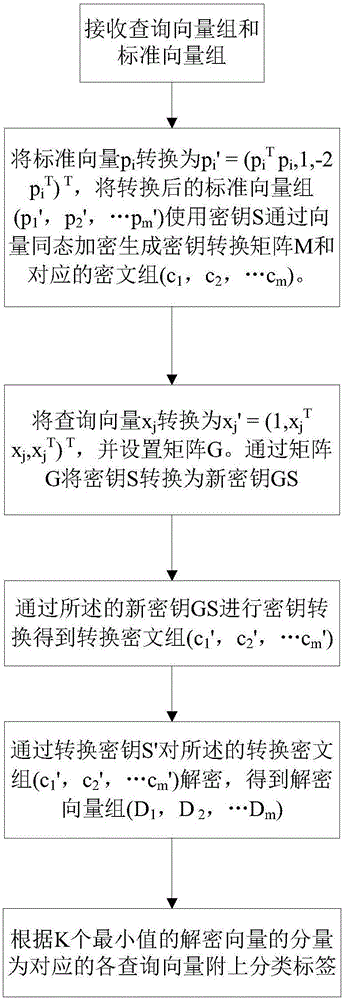
[0040] Such as figure 1 The privacy protection K-NN classification method of the present invention based on vector homomorphic encryption includes the steps:
[0041] A. Receive query vector group (x 1 , X 2 ,...X n ) And the standard vector group (p 1 , P 2 ,...P m ), where the standard vector group (p 1 , P 2 ,...P m ) Corresponds to the standard classification label (t 1 , T 2 ,...T m );
[0042] B. Since there is a formula Sc=ωx+e, S is the key, c is the ciphertext, ω is a large integer, x is the query vector, e is the error term, and the value of each element of e is not greater than At the same time |S| (n represents the number of rows of the query matrix G, which is the number of vectors in the query vector group, w represents the number of columns of the query matrix G, which is the dimension of each query vector), then: (GS)c=ωGx+Ge, It can be seen that Gx is encrypted into ciphertext c under the secret key GS. Therefore, through the query vector group (x 1 , X 2 ,...X...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More