Method and system for detecting malicious application of Android system
A malicious application and Android system technology, applied in computer security devices, instruments, electrical digital data processing, etc., can solve problems that are difficult to popularize and apply, and achieve the effects of good usability, high accuracy, and reduced performance overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0051] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be described in further detail below in conjunction with specific embodiments and with reference to the accompanying drawings.
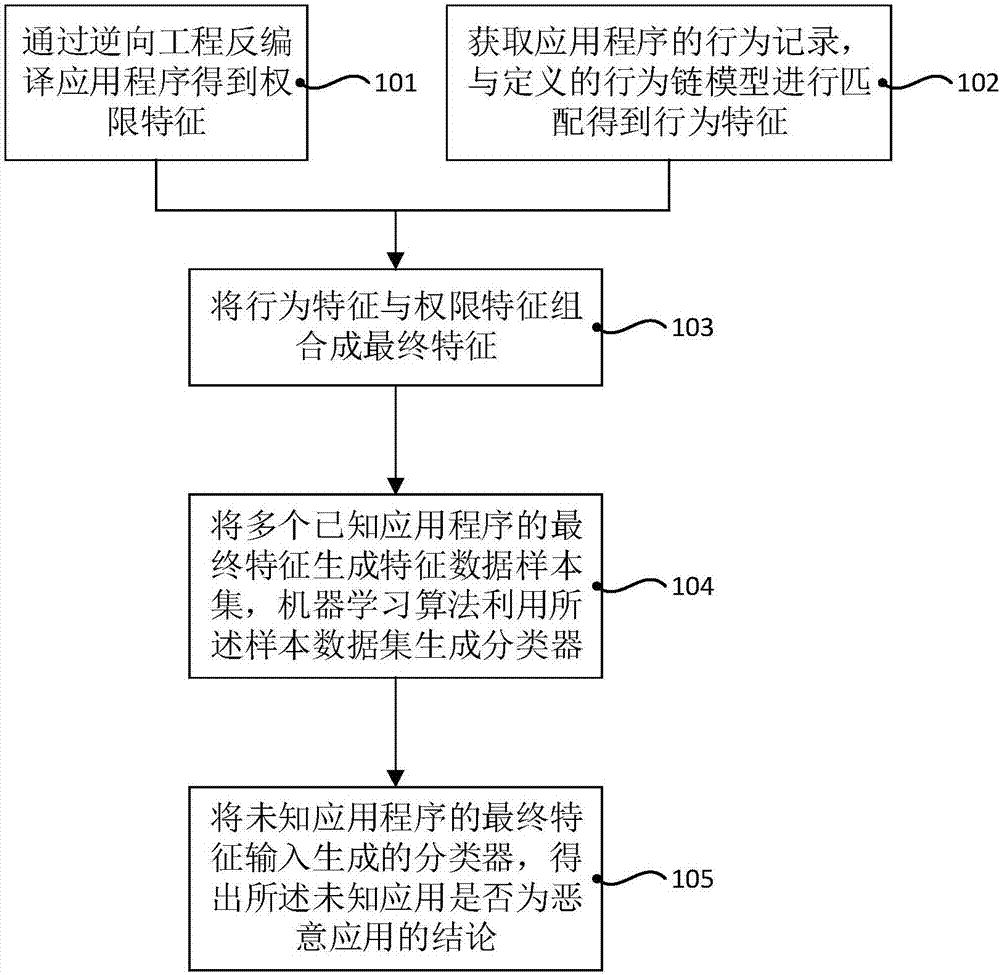
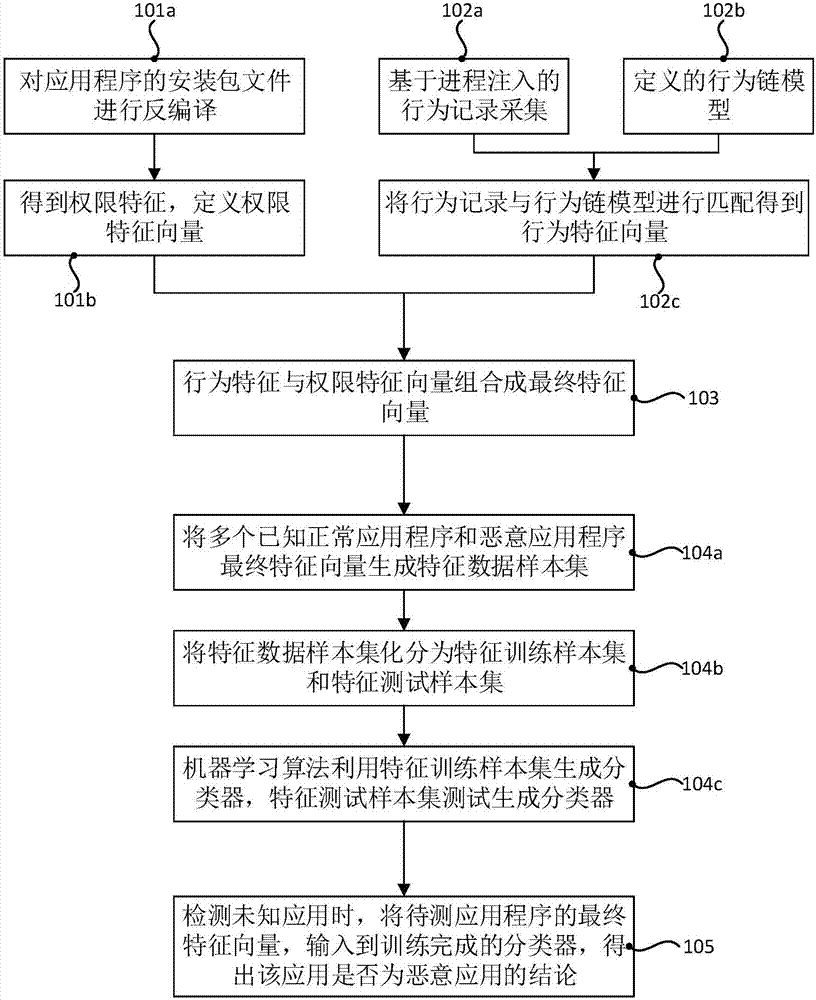
[0052] Such as figure 1 Shown is a flow chart of an embodiment of the Android system malicious application detection method provided by the present invention, the detection method comprising:
[0053] Step 101, decompile the installation file of the application program through reverse engineering to obtain the permission feature;
[0054] Step 102, obtain the behavior record of the application program through the dynamic behavior capture technology, and match the behavior record with the defined behavior chain model to obtain the behavior feature;
[0055] Step 103, combining the behavior feature and the authority feature into a final feature;
[0056] Step 104, generating a feature data sample set from the final featur...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More