Network vulnerability identification method based on removal of timing sequence
An identification method and vulnerability technology, applied in the field of network vulnerability identification based on timing removal, can solve problems such as limited effects, achieve optimal effects, optimize deliberate attack effects, and improve early attack sensitivity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
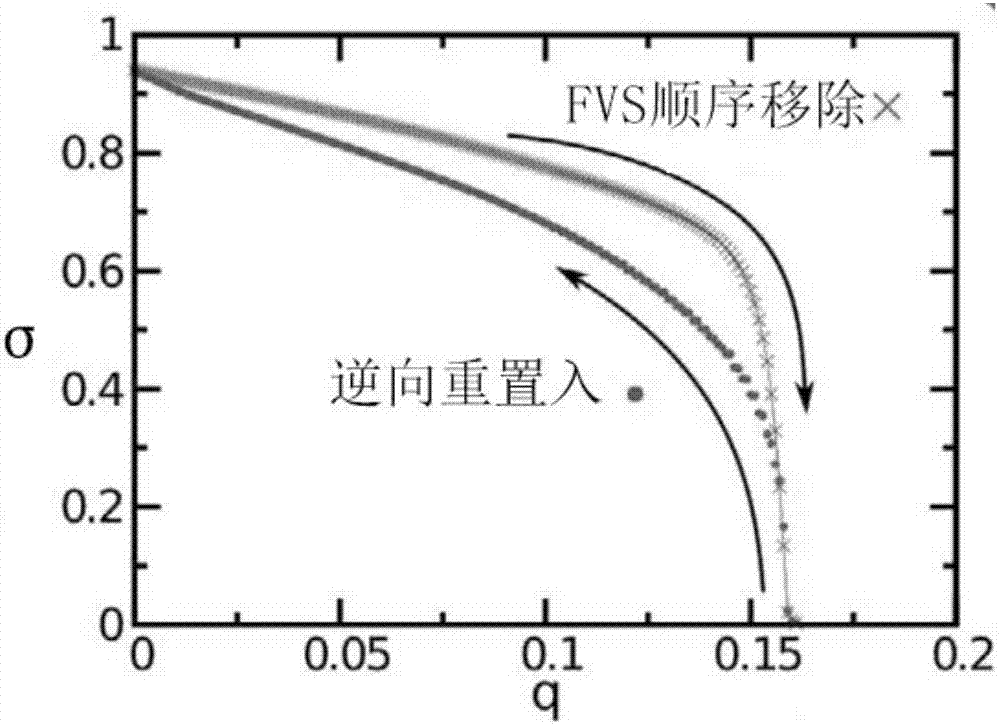
[0062] The present invention provides a network vulnerability identification method based on timing removal. In order to further clarify its technical means and effects, the technical method of the present invention will be described in detail below in conjunction with an ER random model network embodiment.
[0063] A network vulnerability identification method based on timing removal in the present invention, see Figure 4 As shown, its specific implementation steps are as follows:
[0064] Step 1. First, the node and edge information need to be given according to the model network. Take the ER random model network as an example (the number of nodes N=10000, the number of edges M=17482, the probability of connecting edges p=0.00035), where the ER random network represents a network composed of N nodes, any node and other nodes with probability p Generates a random model network of connected edges. For the model network, no node attribute can be set; the node number starts f...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More