User information collection method
A technology of user information and collection method, applied in the field of communication, can solve problems such as insufficient understanding, inconsistent user terminal information needs, inaccurate user positioning, etc., to achieve the effect of improving health quality and realizing health protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
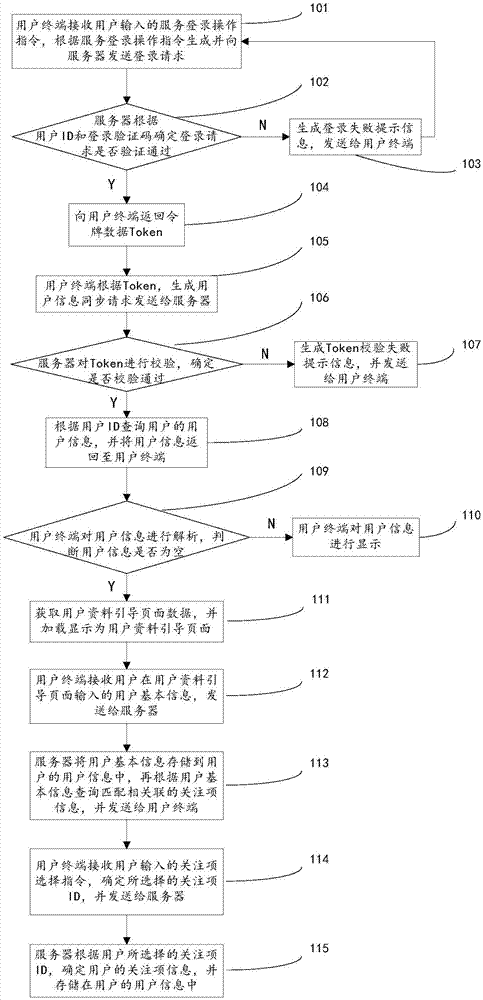
[0038] figure 1 It is a schematic flowchart of the method for collecting user information provided by Embodiment 1 of the present invention. The following combination figure 1 As shown, the method for collecting user information provided by Embodiment 1 of the present invention will be described.
[0039] Step 101, the user terminal receives the service login operation instruction input by the user, generates and sends a login request to the server according to the service login operation instruction;
[0040] Specifically, the login request includes the user ID and the login verification code of the user; therefore, the login request obtained by the server includes the user ID and the login verification code of the user.
[0041] Step 102, the server determines whether the login request is verified according to the user ID and the login verification code;
[0042] In a specific process, the server receives the user ID and login verification code; generates a random string ...
Embodiment 2
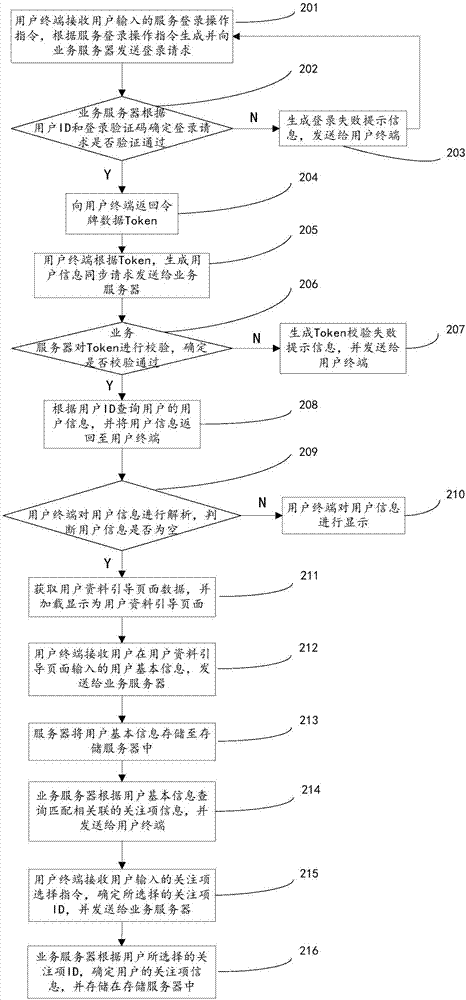
[0076] figure 2 It is a schematic flowchart of the method for collecting user information provided by Embodiment 2 of the present invention. The following combination figure 2 As shown, the method for collecting user information provided by Embodiment 2 of the present invention will be described.
[0077] Step 201, the user terminal receives the service login operation instruction input by the user, generates and sends a login request to the service server according to the service login operation instruction;
[0078] Specifically, the login request includes the user ID and the login verification code of the user; therefore, the login request obtained by the service server includes the user ID and the login verification code of the user.
[0079] Step 202, the service server determines whether the login request is verified according to the user ID and the login verification code;
[0080] In a specific process, the business server receives the user ID and login verificati...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More