Network security situation assessment method based on evidence reasoning rule
A technology for network security and situational assessment, applied in the field of information security to achieve the effect of good situational assessment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0018] In order to facilitate those of ordinary skill in the art to understand and implement the present invention, the present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the implementation examples described here are only used to illustrate and explain the present invention, and are not intended to limit this invention.
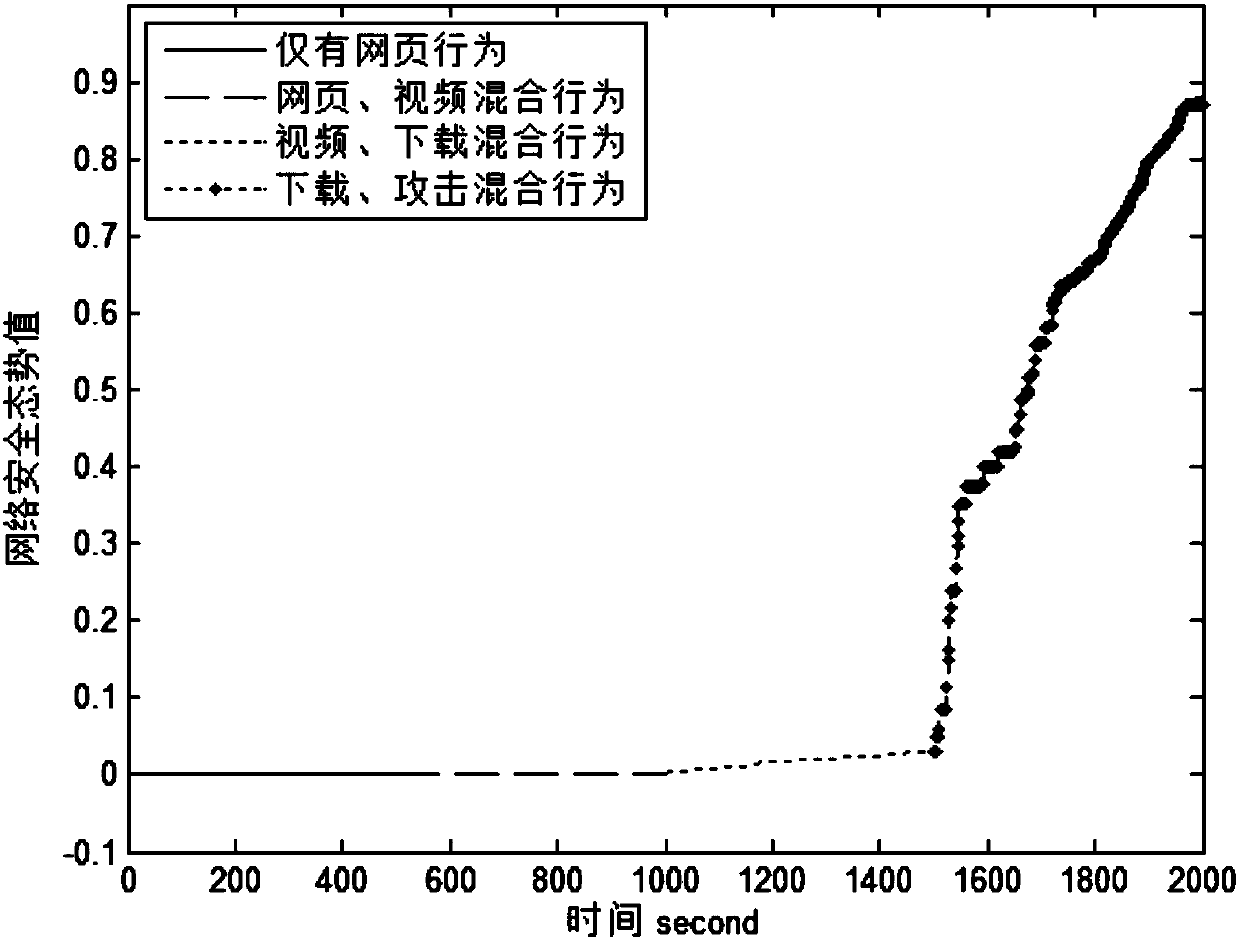
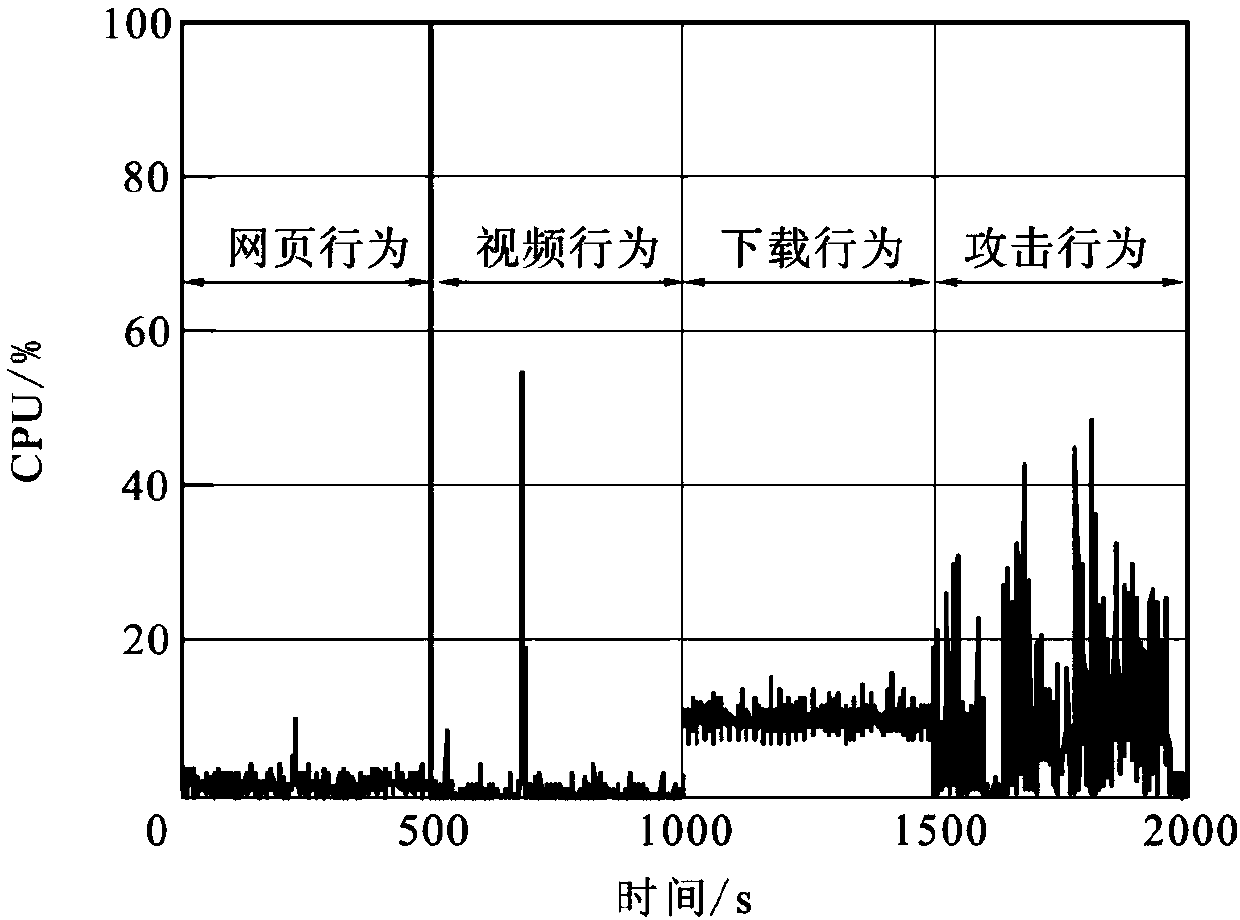
[0019] In this embodiment, after comprehensively comparing various existing methods, the evidence reasoning rules are used for evaluation. Existing assessment methods mainly analyze the security incidents caused by exploit attacks, and do not pay enough attention to the threats caused by normal behavior peaks. Therefore, the present invention comprehensively analyzes the normal behavior and attack behavior in the network environment, so as to evaluate the network security situation.
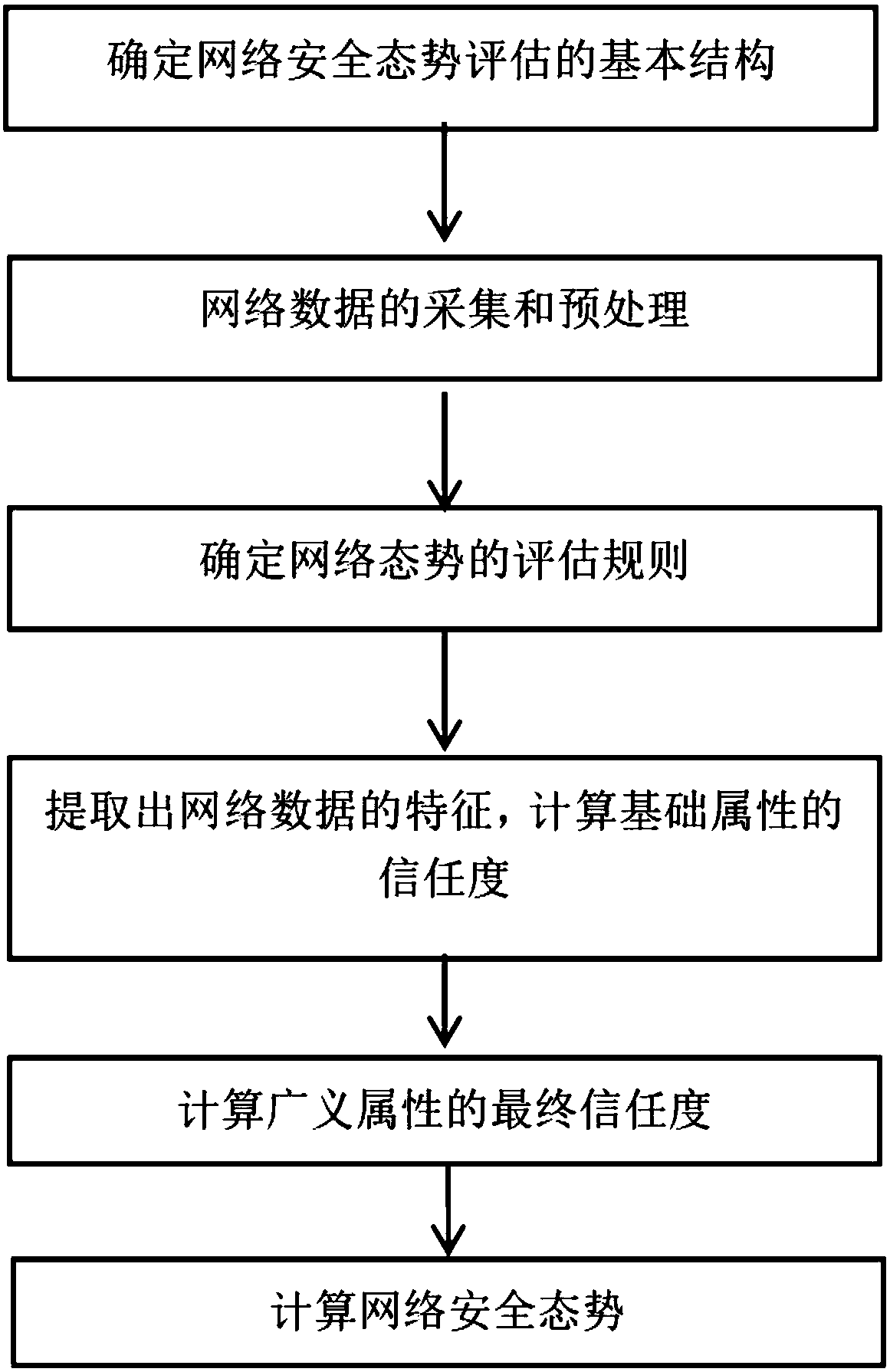
[0020] please see figure 1 , a network security situation assessment meth...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More