Edge computing node identity authentication method based on AES algorithm
A technology of identity authentication and edge computing, which is applied in identity authentication-related applications to achieve high performance, flexibility, low latency, and high dynamics
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0047] An AES algorithm-based edge computing node identity authentication method provided by the present invention will be described in detail below.
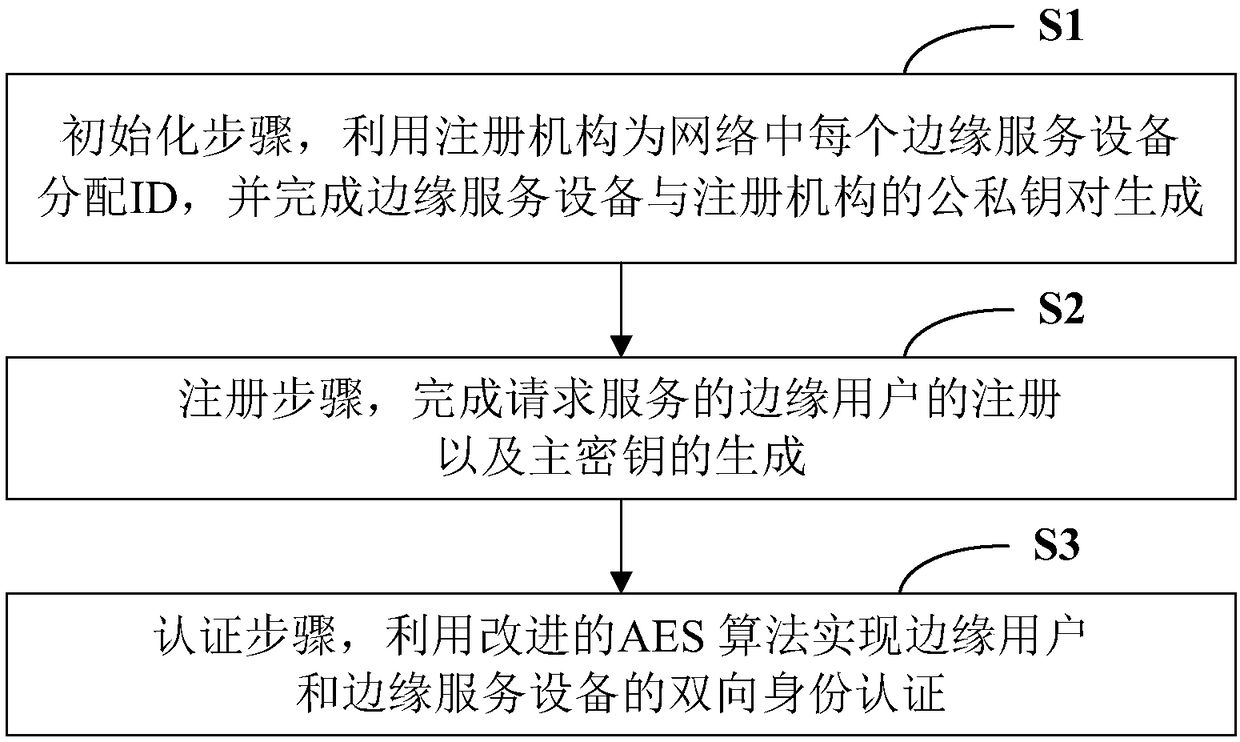
[0048] see figure 1 , is a flowchart of an AES algorithm-based edge computing node identity authentication method in an embodiment of the present invention.
[0049] In step S1, the initialization step uses the registration agency to assign an ID to each edge service device in the network, and completes the generation of a public-private key pair between the edge service device and the registration agency.
[0050] In this embodiment, edge computi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More