Storage object tamper-proof method, device and apparatus
A technology for storing objects and anti-tampering, applied in memory systems, preventing unauthorized use of memory, instruments, etc., can solve problems such as poor data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
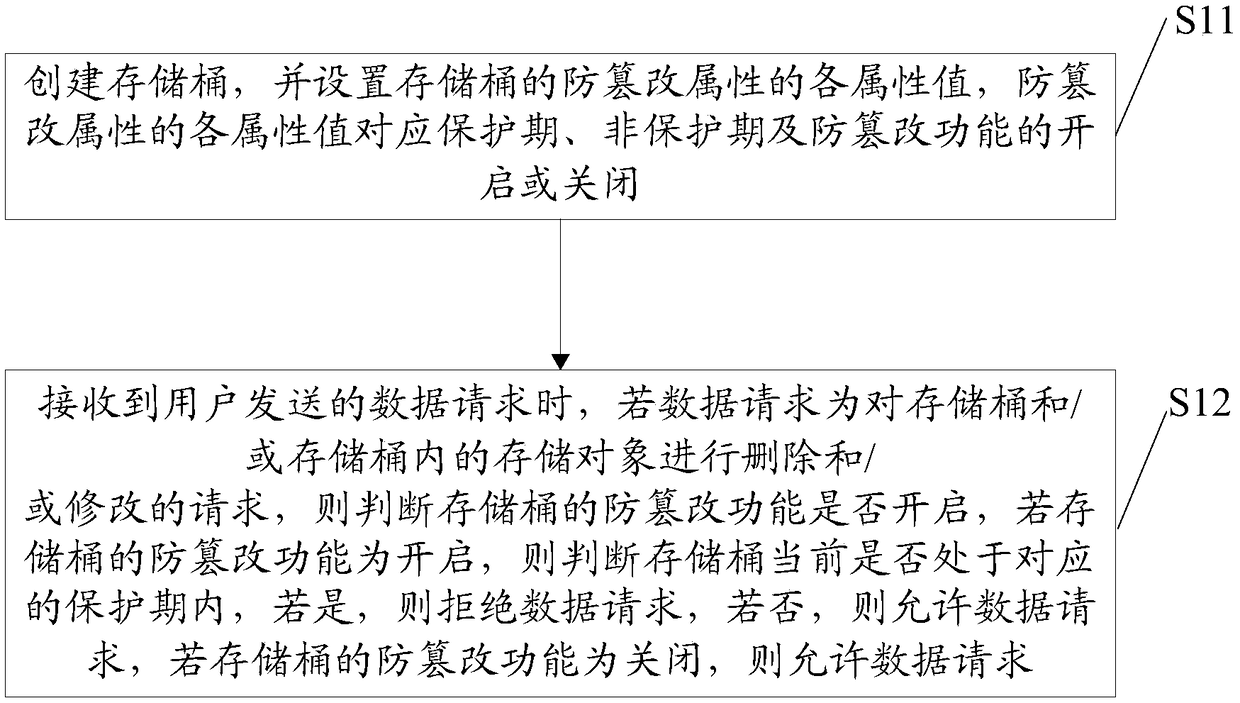
[0035] see figure 1 , which shows a flow chart of a storage object tamper-proof method provided by an embodiment of the present invention, which may include:
[0036] S11: Create a storage bucket, and set each attribute value of the tamper-resistant attribute of the storage bucket, and each attribute value of the tamper-resistant attribute corresponds to the protection period, the non-protection period, and the on or off of the tamper-proof function.
[0037]...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap