A method and apparatus for obtaining a valid registry key name
A registry and key-value technology, applied in the computer field, can solve the problems of slow running speed of the host, complex data structure, consumption, etc., and achieve the effect of speeding up reading
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
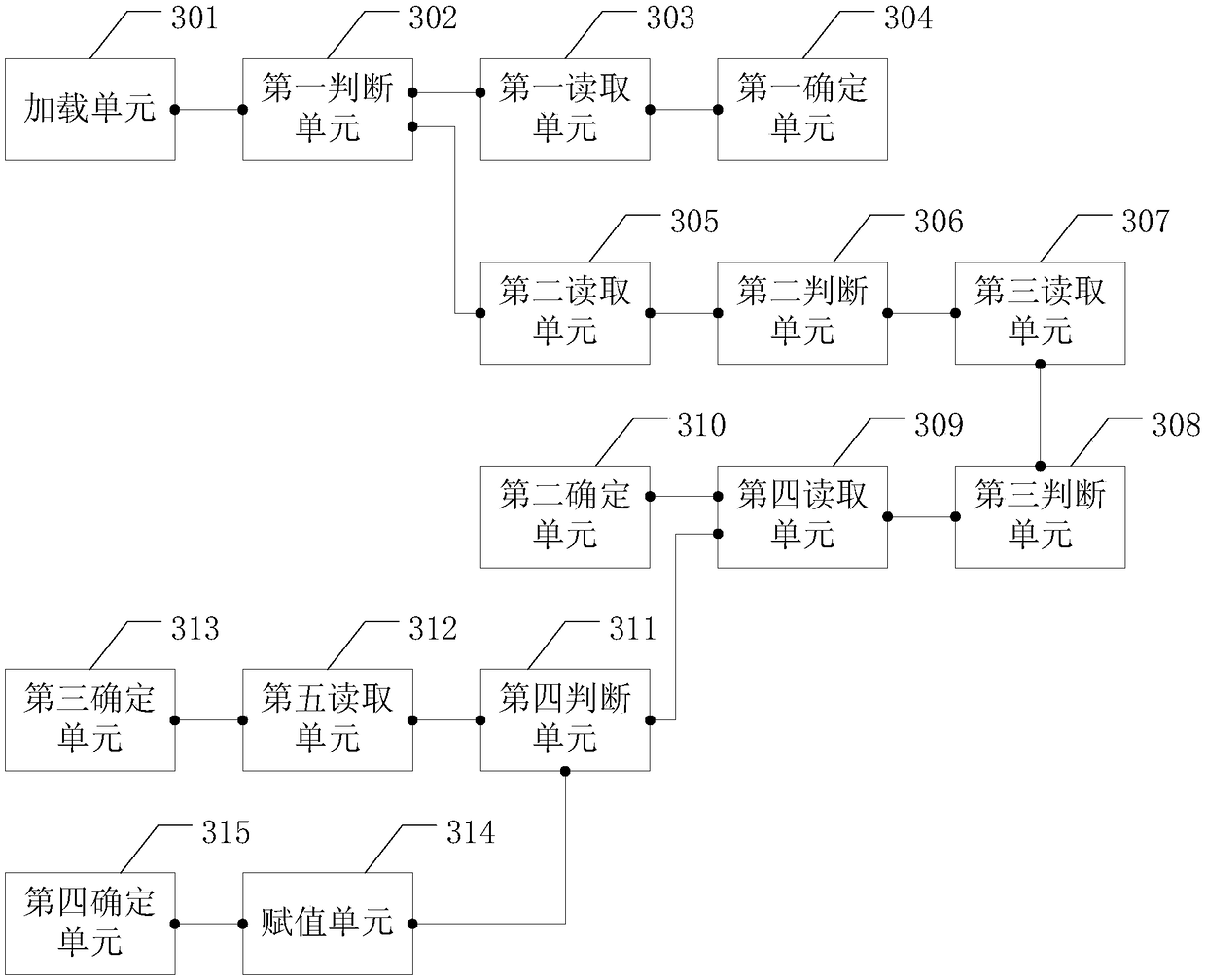
[0049] The embodiment of the present application provides a method and device for obtaining valid registry key names, which are used to pre-set the method for reading valid registry key names for ADML-type security baseline items, and speed up the reading of valid registry key names. speed.
[0050] see figure 1 , figure 1 It is a schematic diagram of an embodiment of a method for obtaining a valid registry key name in the embodiment of the present application. An embodiment of the method for obtaining a valid registry key name in the embodiment of the present application includes:
[0051] 101. The host loads the XML data in the ADML-type security baseline project into the memory;
[0052] In this embodiment, when the host is writing a security baseline check program check software not officially developed by Microsoft, in order to quickly extract the valid registry key name in the ADML-type security baseline item, the host can first add an XML of an ADML-type security baseli...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More